Cloud and CSAM Investigations: Compatible or Ill-Considered?
In 2021 alone, there were 85 million reports[1] related to Child Sexual Abuse Material (CSAM) worldwide. Let’s repeat that for a second to try and understand it – 85 million. As incomprehensible as this number is, it does not include all the unreported material or the hundreds of thousands of additional reports involving child sex tourism, trafficking, molestation, and enticement.
The COVID-19 pandemic has exacerbated the issue, with a 64% year-on-year increase in confirmed child sexual abuse reports[2], and with the US now hosting more child sexual abuse content online than any other country in the world[3].
Wherever in the world child sexual abuse material is found, the investigation into the victimization of our most vulnerable starts with routing the reports to the appropriate law enforcement agency.
For law enforcement to achieve justice within child exploitation cases, they must deal with the added sensitivity of its evidence. In these cases, the files are not only digital evidence, but are also digital contraband; the sexual abuse of a child is forever captured in photos and videos. The first – and most foundational – step to achieving their objective is to ensure the effective management of their investigations.
Law enforcement agencies are looking to digital transformation to meet growing backlogs, and the cloud has proven to be an effective force multiplier. But what happens when cloud and the management of CSAM investigations converge? Are they incompatible?

Cloud computing – Source: Shutterstock
If the bad guys put CSAM in the cloud to facilitate their operations, should law enforcement be using the same means to combat CSAM? The answer is they must.
While the mind immediately races to security, let’s first look at the traditional processes. Today digital forensics examiners apply their expertise to identify and catalog CSAM. Our examiner knows this evidence is key a child’s safety and the pursuit of justice. This digital contraband will be used in a criminal prosecution and, more importantly, to save a child. Naturally, the examiner functions as part of an investigative team, and the evidence is commonly copied to physical media to facilitate the necessary collaboration.
First, our investigator receives his copy, which is treated as original evidence by policy for the law enforcement agency. The investigator makes a working copy, which is not a bad idea considering industry leader SanDisk warranties most thumb drives for not more than five years, and many for only two years[4].
Next, the investigator may need to consult with a forensic pediatrician, for the purpose of age identification, so another copy is made. The prosecution will review the evidence and a submission made to the National Center for Missing and Exploited Children’s (NCEMC) Child Victim Identification Program (CVIP), meaning more copies are necessary.
Today’s process has already resulted in five copies, which begs the following questions:
- Are they being effectively managed?
- Are they secure?
- Is the external media durable enough to ensure the evidence survives until trial?
- How do you know who has viewed these copies, when, and from where?
- When the time comes to destroy the evidence, how do you comply when uncertain about how many copies there are and where they exist?
- What do you tell a victim who has been revictimized, due to the unavailability of evidence at trial or a lost copy outside the control of law enforcement?
Cloud tackles the root problem: connectivity. People in various roles at multiple agencies and organizations must work together for justice to be served. Imagine eliminating all the unreliable, insecure copies and adopting a central repository for evidence review. Each login is recorded, as is detailed information on who shared with whom and when, or if, it was accessed.
Compliance frameworks encapsulate the best practices and requirements to ensure cloud security and data durability. The Zero Trust principle, for example, assumes every interaction between systems or users must be verified. Basic security principles dictate two-factor authentication for logins, and that data must be encrypted both in transit and at rest to prevent unauthorized access.
The technology, principles, and frameworks of a well-architected cloud solution combine to create an environment every bit as secure as the evidence room. No such principles and frameworks exist for endless copies of USB drives sitting on shelves, in folders, and desk drawers.
Fortunately, the imagination is not required as this solution exists today. A secure, cloud-based investigative management solution, such as Cellebrite Guardian, bridges the network gaps between stakeholders, empowering investigators, examiners, prosecutors, and other case stakeholders to work together in the cloud more efficiently than was ever possible with copies of copies and physical transport.
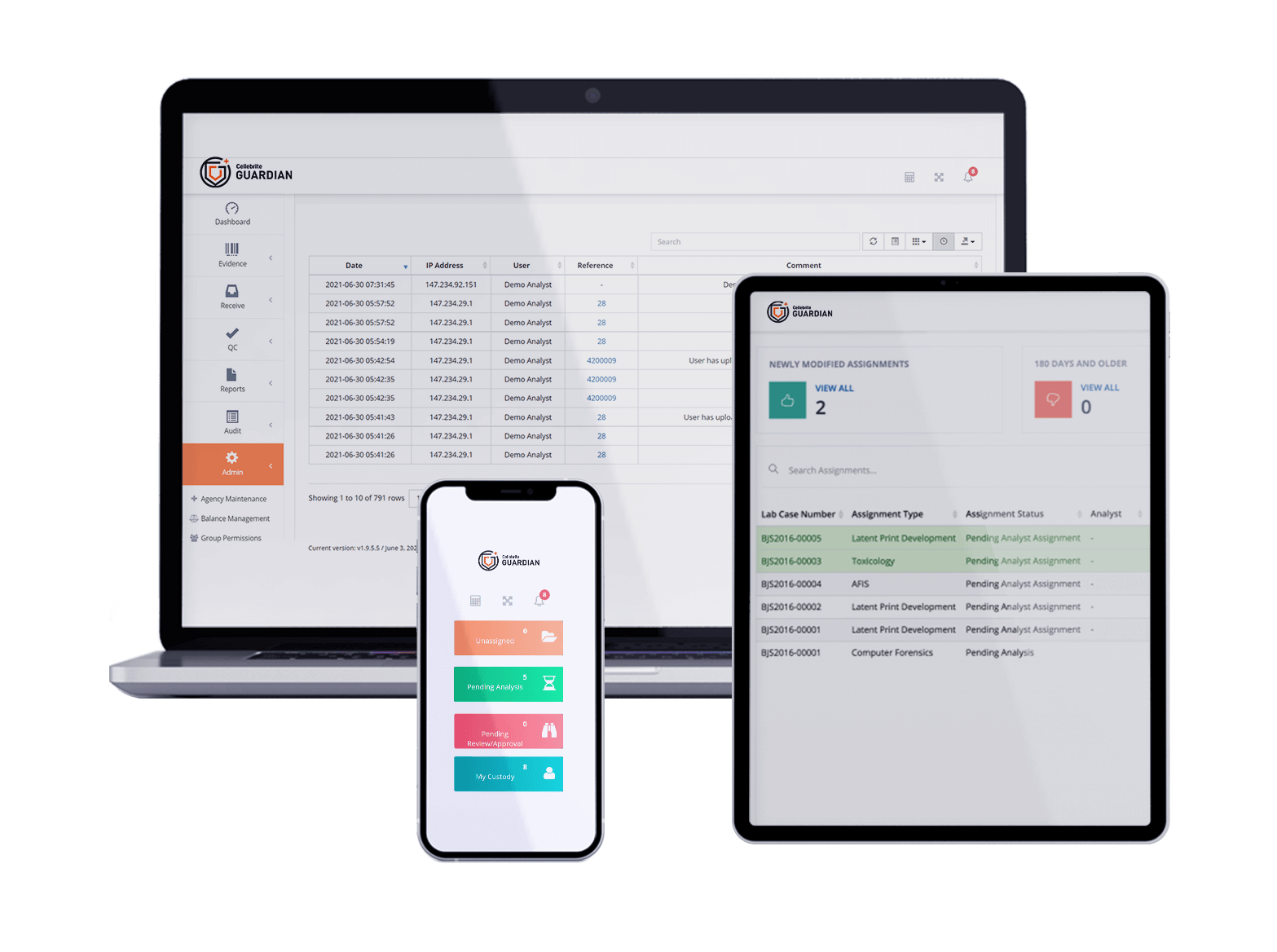
Cellebrite Guardian – Source: Cellebrite
And it’s not only about being more efficient. Additional features within Cellebrite Guardian address the challenges around the ethical treatment of digital evidence – with a specific focus on Child Sexual Abuse material – to aid law enforcement in handling sensitive digital evidence. “Suspected CSAM” tagging functionality for each upload ensures users are aware of a file’s sensitive status, triggering special handling procedures so as to prevent unintentional sharing and mitigate the risk of CSAM falling outside law enforcement control.
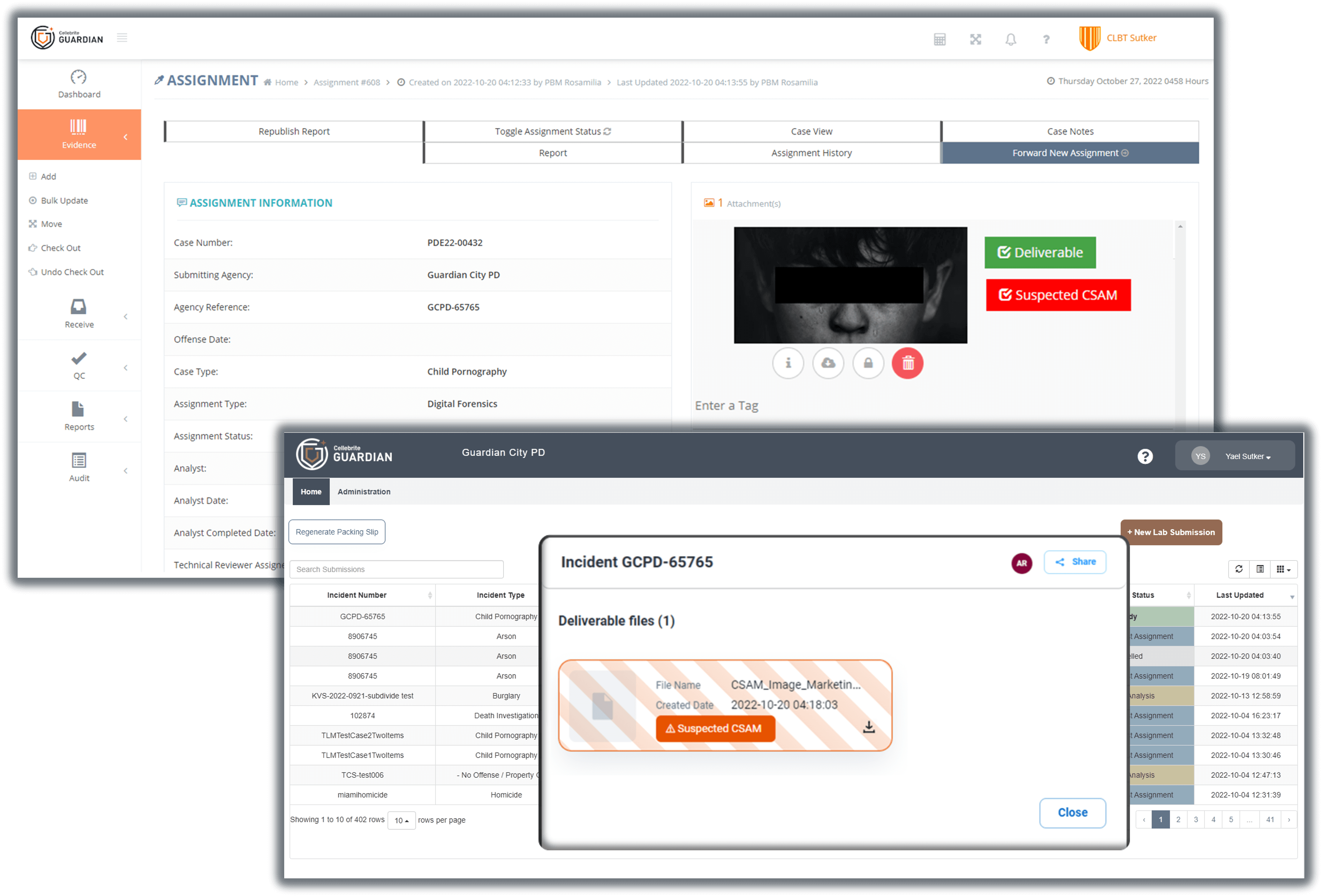
The enhanced Investigator Activity Report shows all user activity details creating checks and balances for full transparency. And ultimately in place of endless uncontrolled copies, Cellebrite Guardian provides a secure repository serving as the single truth of an investigation’s digital evidence.
Criminal use of technology to further the sexual abuse of children is not slowing. It’s time to modernize the investigative workflow by leveraging the cloud as a force multiplier.
Learn more about how Cellebrite Guardian can help your team, here.

Ryan Parthemore – Source: Cellebrite
About the Author: Ryan Parthemore joined Cellebrite as a SaaS evangelist following his extended tenure within law enforcement. A veteran in the industry, Ryan has over 20 years of experience as a patrol officer, detective, and technical lead in a government digital forensics laboratory.
During his time in law enforcement, Ryan has completed hundreds of hours of training in digital forensics, performed thousands of digital forensics examinations, represented his unit through ANAB ISO 17025 accreditation, and testified as an expert witness in state and federal court. Ryan moved to Cellebrite to utilize his expertise to help others in law enforcement find more effective ways to resolve cases.
[1] European Commission, May 2022
[2] Internet Watch foundation, 2022
[3] UK-based Internet Watch Foundation, Apr 2022
[4] https://kb.sandisk.com/app/warranty/a_id/22478