Using Pathfinder to Avoid Ethical Dilemmas in Digital Forensics
Technology has improved nearly every facet of law enforcement. Officers may have, for example, body cameras strapped to their vests, automatic license plate readers in their cars, or even fingerprint scanners readily available. These devices undoubtedly help law enforcement catch and prosecute more criminals.
However, advancements in police technology are also scrutinized when they raise concerns about ethics. With so much information at ones fingertips, is it possible to view too much, or to share more information than is necessary or legal? No matter how advanced the technology is, it is ultimately a human choice of how to use it. And this is where Cellebrite Pathfinder can help.
Inadequate training, limited resources, and outdated equipment have all been documented as issues leading to ethical problems within digital forensics. In a recent interview with Sigal Caspi, Subject Matter Expert at Cellebrite, she identified two fundamental ethical issues related to digital forensics: privacy and the ability to redact privileged or irrelevant information.
The question of what to do with private, privileged, or irrelevant information before investigators release it in discovery is a concern for law enforcement. That’s because handling this type of information improperly can lead to case dismissals or unwanted civil lawsuits.
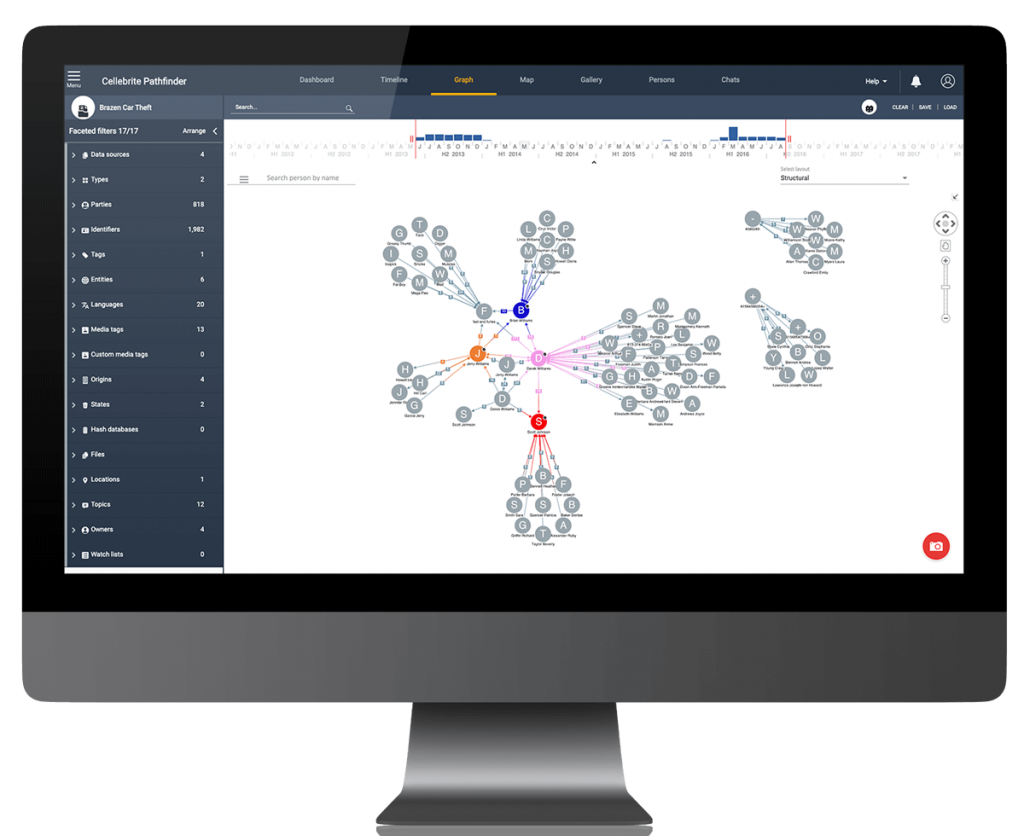
Pathfinder provides investigative agencies with various tools to ensure proper use of digital data in accordance with warrants and legal guidance. Using Pathfinder, managers can review and redact privileged data and only then assign it to the relevant investigators.
Potential Privileged Information Lists
Searching names and phone numbers can easily surface privileged material from doctors, psychologists, and attorneys. Investigators can use Cellebrite Pathfinder to create their own lists of potential privileged information. These watchlists can be stored and added to the redaction report before submitting the data into evidence.
Hash Databases to Filter Video and Images
Investigators can use hash databases to compare sets of images, videos, and blacklisted files, often related to child exploitation. As Sigal explains, the hash database can be used to blur out known child sexual abuse material (CSAM) or other sensitive images. “You cannot see anything. You know it’s an image, but it has been redacted.” Advanced hash filtering allows investigators to gather evidence without physically viewing the video or image, reducing the potential for mental trauma.
Fight Crime, Not Time

People, Location, and Business Search
Cellebrite Pathfinder’s text analytics engine analyzes unstructured text and summarizes topics of conversation and other textual content. It automatically identifies entities in text, including specific locations, names of people and businesses, mentions of religion, and more. If investigators determine the text to be private or privileged, they can tag that information before it is extracted.
Advanced Word Search
In addition to advanced entity search, investigators can use the Cellebrite Pathfinder search bar to find generalized sensitive textual content. Investigators can search for general terms, such as ‘psych,’ “Dr.” “Pastor,” “lawyer,” etc. then go through that data to determine what is private and what they can release in discovery.
Advanced Gallery Search
Investigators can use Cellebrite Pathfinder’s gallery view to find additional items that may lead to more sensitive or confidential data.
For example, if investigators have logo images of a law firm, this can help them find attorney/client-privileged material. Once identified, investigators use Pathfinder’s advanced categories feature to filter out images into specific groups, such as “Suspected CSAM,” “Nudity,” or “Attorney/Client.”
Preparing Digital Evidence: Redacting and Exporting Data
After investigators identify, tag, or group private, privileged, or irrelevant information, they can use Cellebrite Pathfinder’s advanced exporting features to filter that information before submitting it into evidence. They can then create a customizable report with the details of the extraction and redaction.
Digital forensic systems collect, filter, process, store, and distribute data. “Everything is extractable, but we have to think about innocent people,” Sigal continues. “To avoid the release of private, privileged, or irrelevant content, Cellebrite Pathfinder supports organizational processes to ensure that the use of data complies with local, state, and federal rules. It also tracks the use of the product so that a full audit trail is available if questions arise about what was searched for, and by whom. Humans will ultimately decide how to use the product, but Pathfinder will allow them to make ethical decisions and if necessary, show that they did.
Contact Cellebrite for a Pathfinder demo.
About the Author

Alan Flora – Subject Matter Expert, Cellebrite.
Alan Flora is a Subject Matter Expert at Cellebrite. During his three decades of law enforcement in the United States, Alan witnessed firsthand the dramatic rise in the role technology has played in both crime and crime fighting. Midway through his career, in 2007, Alan transitioned from general investigations to a specialized role in the Computer Crimes Unit of the North Carolina State Bureau of Investigation where he eventually rose to Special Agent in Charge.
From 2015 until 2021 he served as the Commander of the North Carolina Internet Crimes Against Children (ICAC) Task Force. As a Cellebrite SME, he works with the Investigative Analytics team developing tools that reduce workload and increase efficiency.
Alan holds a Master of Criminal Justice degree from Saint Leo University, and a Bachelor of Social Science from Gardner-Webb University. He is passionate about mental wellness issues for law enforcement and frequently volunteers his time and expertise as an advocate for ICAC personnel.
Contact us to learn more about how Cellebrite Pathfinder can assist you to accelerate investigations.