Device Type

So Many Logs, So Little Time: Efficient Windows Event Log Analysis

Exploring the Windows Activity Timeline, Part 3: The Value of Clipboard Content
Exploring the Windows Activity Timeline, Part 2: Syncing Across Devices

Analyzing Program Execution Windows Artifacts

Collecting and Analyzing E-mail from a MacBook
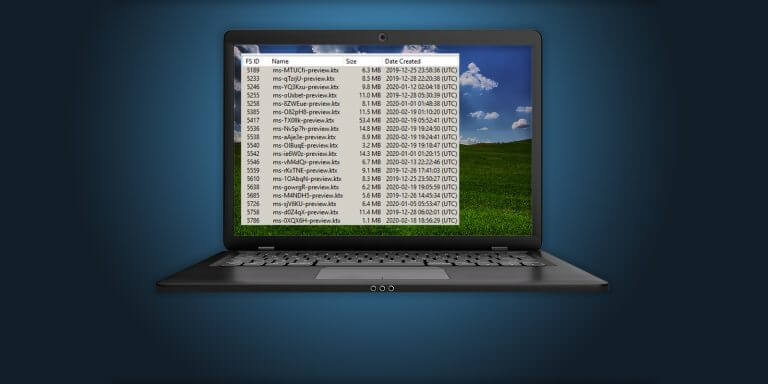
Exploring the Windows Activity Timeline, Part 1: The High Points

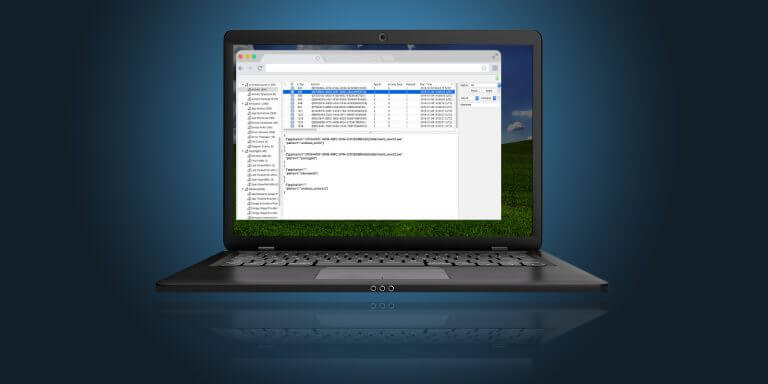
Boost eDiscovery and Corporate Investigations with Cellebrite’s Computer Access Solutions
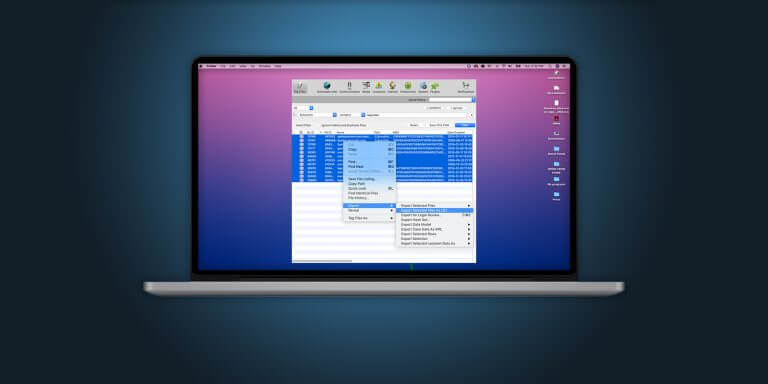
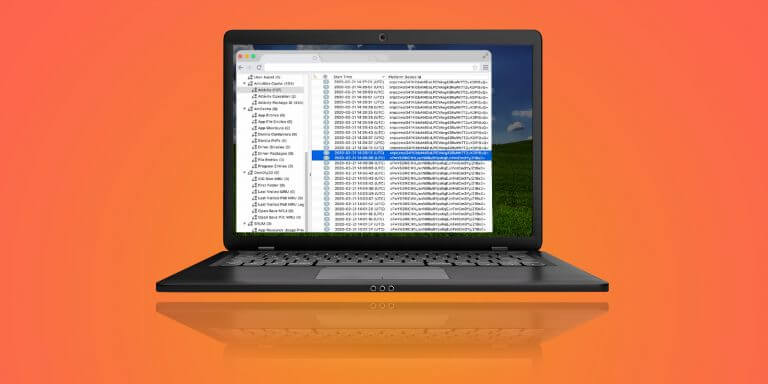
Apple Keychain Parsing in Cellebrite Inspector
An Easy Way To Detect Time Manipulation on iOS Devices – Cellebrite Physical Analyzer

If I Could Turn Back Time—A Closer Look at iOS Time Modifications

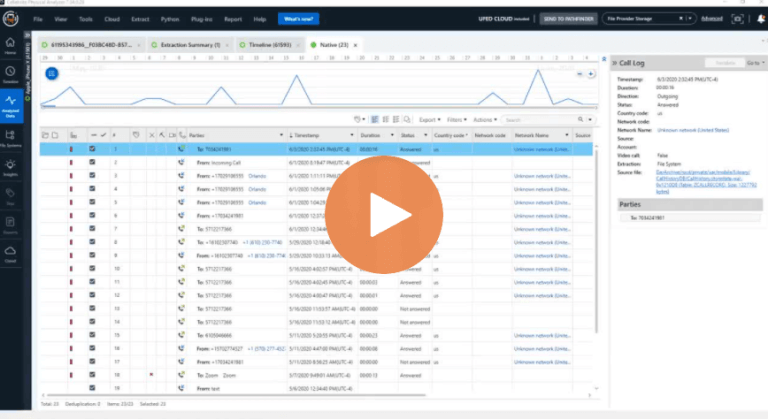
Find The Who, What, and Where With Chat View in Cellebrite Physical Analyzer
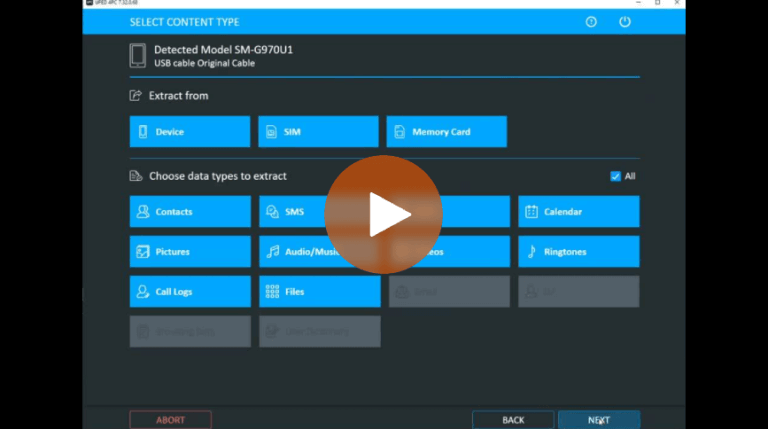
Autodetect: Special Feature Built Into UFED for Android 8 & 9 Samsung Devices
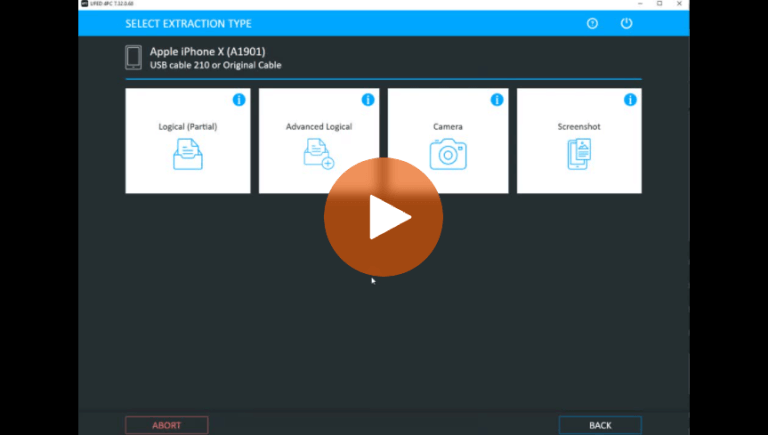
Different Data Collection Options for an iPhone Explained – Cellebrite UFED
What Can Be Recovered From BFU Data Collection

Computer Access Use Case: Cellebrite Inspector Helps Convict Child Pornography Criminal

Data Quality and Quantity – How to Get the Best of Both Worlds, Part 3 – Results Should Not Confuse You
