Exploring the Windows Activity Timeline, Part 2: Syncing Across Devices
In Part 1 of this series on “Exploring the Windows Activity Timeline,” we explored Timeline’s basics: where it is, what it looks like on disk, and how using Cellebrite Inspector can help you find low-hanging investigatory nuggets. Timeline can provide much more, so let’s dig a little deeper. We’ll also show you how to apply the same search techniques to Mac-based devices.
To briefly recap, Timeline is a Windows 10 facility for tracking many types of user activities. It can remind the user what they’ve been up to, and let them simply click a UI tile to resume one of those previous activities, eg, open a browser up to a web page the user previously visited.
Windows Sync
In Part 1 of this series, we focused solely on a single machine. As you might have gathered from the ConnectedDevicesPlatform part of the path where the main database (db) resides, it can sync a user’s activities across multiple machines.
In the simplest case, this only requires that the user log in to multiple Windows 10 machines with the same Microsoft ID. When the user logs into a second Windows 10 machine with the same Microsoft ID they used on the first machine, activities stored in the db will sync between them. The same happens when using more than two machines.
To illustrate how this works, I performed the following test:
-
- I spun up one of several Windows 10 VMs (version 1903) I use for testing by logging in with one of my Microsoft ID test accounts.
- I then did some “normal user stuff” – I web surfed in a few browsers, created and edited some documents, and viewed some photos.
- Later, I created a new VM (version 1909). I then logged in with the same test Microsoft ID test account I used on the 1903 VM.
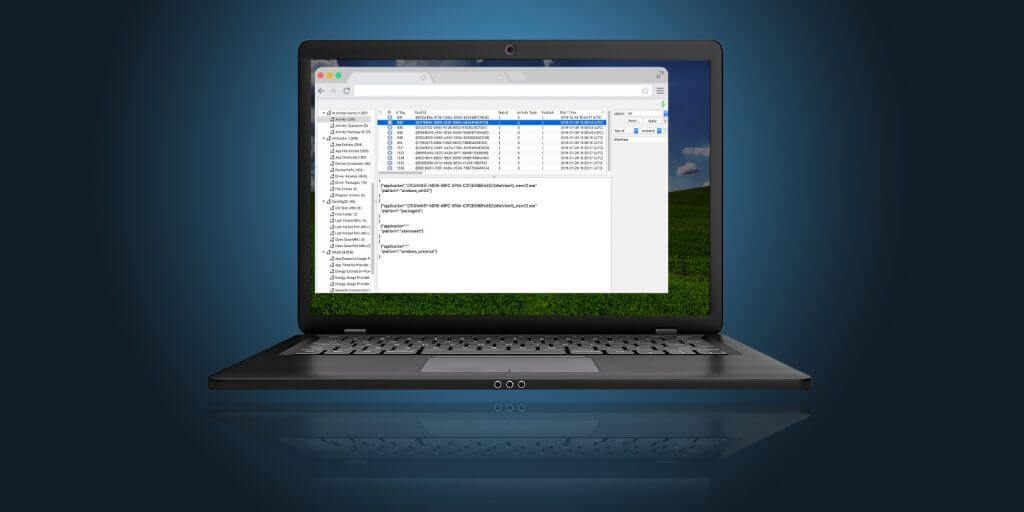
By examining the ActivitiesCache.db on the new 1909 VM, this is what I saw:
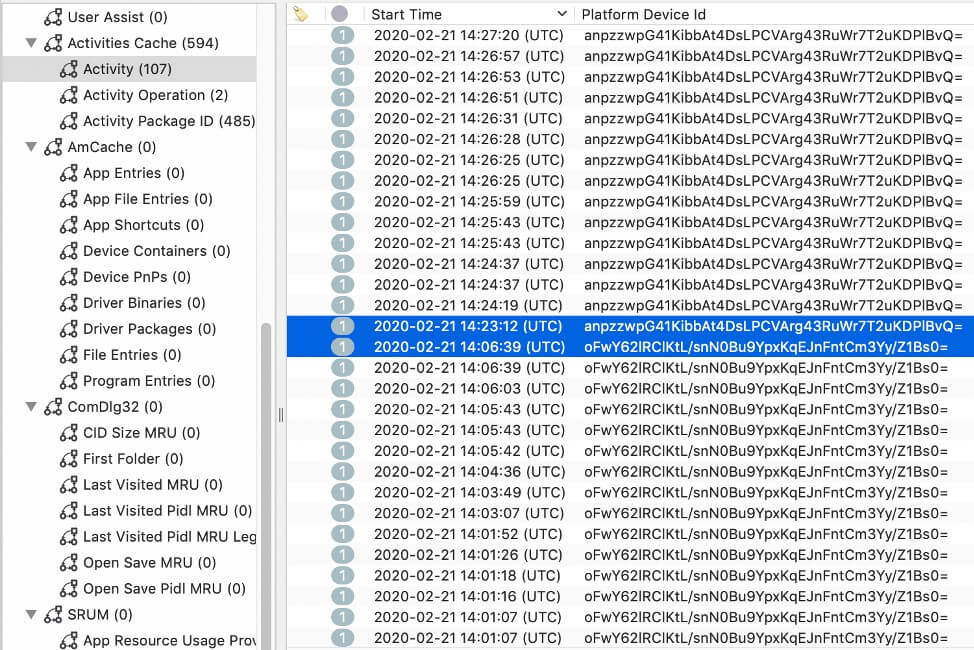
Figure 1: ActivityCache.db on 1903 VM
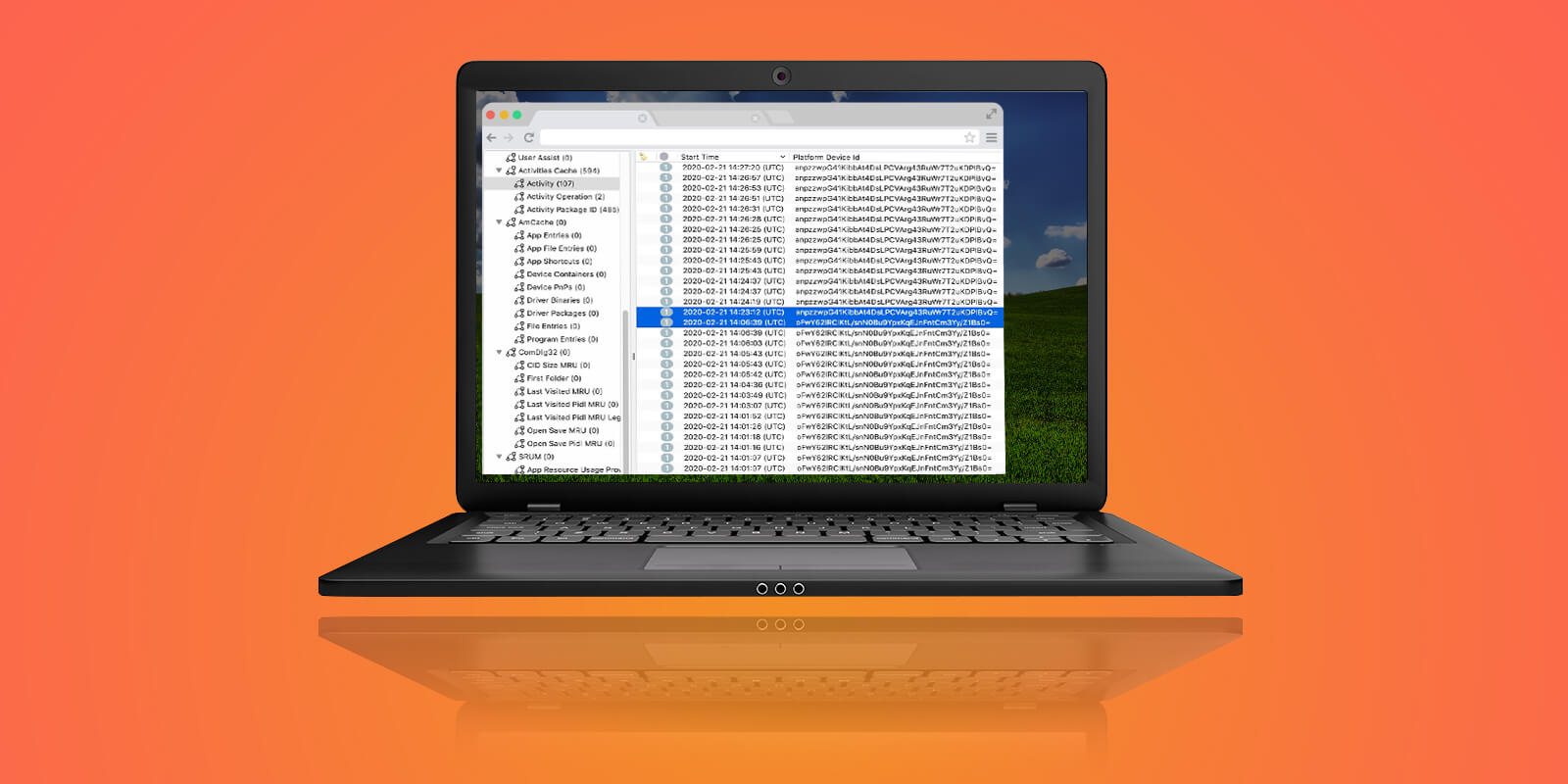
We can see two different values highlighted in the Platform Device ID column. This field holds a base64 encoded binary blob that doesn’t seem particularly useful at first glance. But when we look at the registry for the vico user account on the 1909 machine at NTUSER.DAT / Software / Microsoft / Windows / CurrentVersion / TaskFlow / DeviceCache, we see that these values can be mapped to specific, distinct machines.
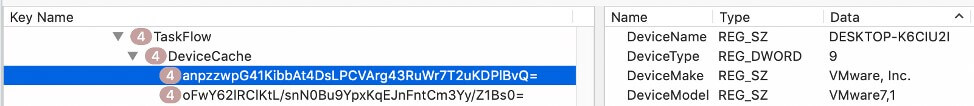
Figure 2: First DeviceCache Entry
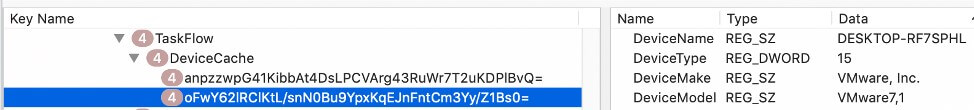
Figure 3: Second DeviceCache Entry
Note that the two highlighted base64-string Key Names in Figures 2 and 3 match the two Platform Device IDs in Figure 1.
While the DeviceMake and DeviceModel match, their DeviceName values differ. Looking at the actual computer names on the two VMs in their respective registries at SYSTEM / CurrentControlSet / Control / ComputerName / ComputerName, we see the following for the 1909 machine:
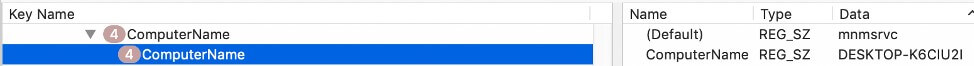
Figure 4: 1909 Computer Name
The 1903 machine shows:
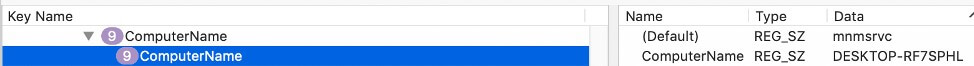
Figure 5: 1903 Computer Name
We can see that the DeviceName values match the names of the respective VMs. Using this mapping we can easily determine which machine a particular activity took place on.
Even more interesting, if we look for the oldest activity start times in the 1909 VM’s ActivitiesCache.db in Figure 6 below, we see that activities go back to 2020-01-03.
I created that VM on 2020-02-21. We not only have synced activities, but we have history from before this machine was even created. Now isn’t that fun?
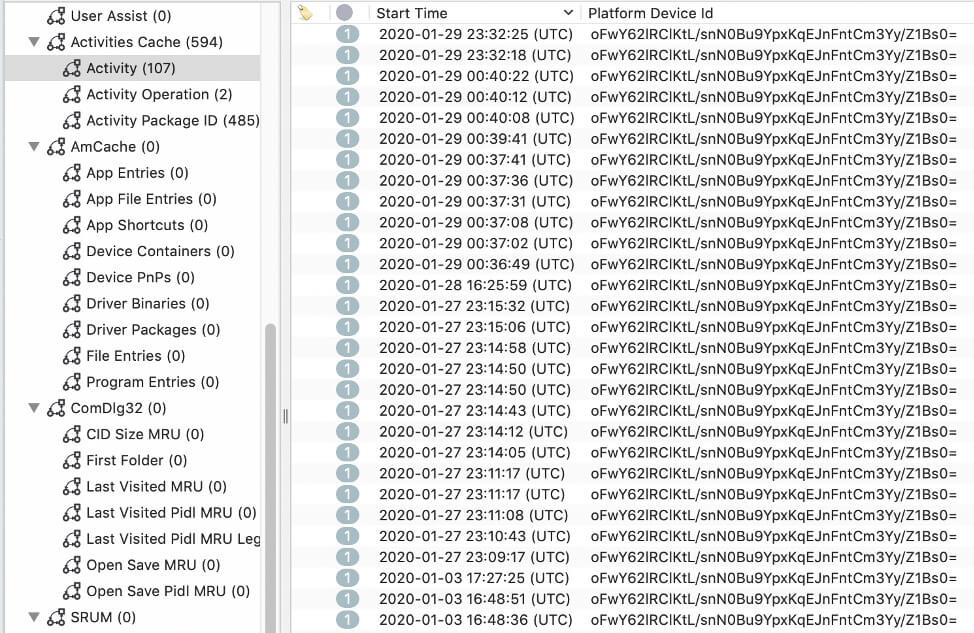
Figure 6: Activity Start Times
This has significant investigative ramifications. For example, if a suspect “loses” a machine that may have contained data relevant to an investigation, any other machine the user logged into with the same Microsoft ID may hold traces.
Even if the suspect purchases a brand new machine and tries to pass it off as an older machine, as long as they use the same Microsoft ID it can potentially hold traces of activity from before the new machine was in use.
But wait – there’s more!
Mac sync
In addition to syncing activities across Windows-based devices, the Timeline can also sync certain kinds of activities from Android, macOS, and iOS devices.
Cellebrite Digital Collector was developed to help gather this information from Mac devices. In my testing so far, if a user installs Microsoft Office 365 and selects the default options (which will also install OneDrive), then activities, like accessing office documents, are synced to any Windows 10 machine a user logs into with the same Microsoft account.
There are several limitations in addition to only syncing office-related activities, however. First, the sync occurs from other operating systems to Windows, but not in reverse. There is no evidence of activity that takes place on a Windows machine that is stored on non-Windows systems. This makes sense since because as far as I know, there is no ActivitesCache.db on the other operating systems. (If anyone has evidence to the contrary, I’d love to hear about it). Other limitations are discussed below in examples from macOS and Android.
Here you can see activities performed on a macOS machine, by looking at the ActivitiesCache.db on a Windows system.
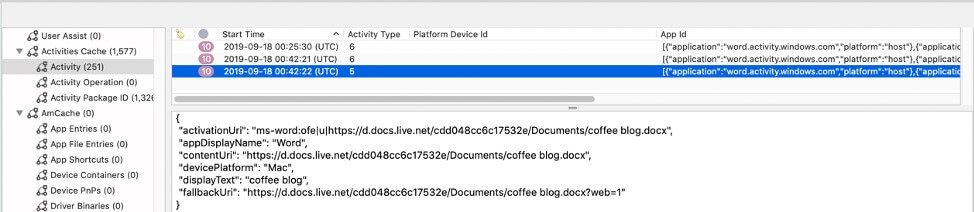
Figure 7: Mac Activity Type 5
The lower-right pane displays information from Activity 5 highlighted in the top-right pane. Remember, Activity Type 5 indicates “app opened.” There are several useful pieces of information shown here:
- Lines 1, 3, 5, and 6 all indicate that a document called “ coffee blog.docx“ was accessed and that it is stored in OneDrive.
- Line 2 indicates that the program used to access the document was Word. (This looks like any other activity that occurred locally on the Windows machine, and other fields in the db corroborate these findings.)
- Line 4 (the most interesting) shows the device Platform and indicates the machine that did the accessing was a “Mac” machine.
Unfortunately, that’s where the good news ends for the most part. In the upper-right pane, the Platform Device ID is empty – there is no way to know which Mac machine the activity took place on. All we know is that it is a machine that has Office365 installed and the known Microsoft account was used.

Figure 8: Mac Activity Type 6
Looking at the Activity Type 6 entry (which indicates “app in focus”) for the same activity (Figure 8), the lower-right pane shows that the activeDurationSeconds is zero. It appears to always be set to zero, so we have no idea how long the user was engaged with the app. Further, the userTimeZone that appears in Windows-based Activity Type 6 activities is also missing. Next, we will look at Android, and we will see the story is much the same.
Android sync
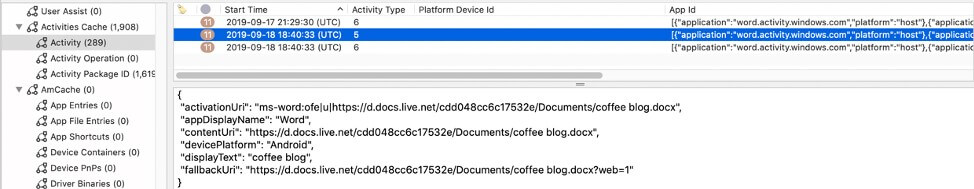
Figure 9: Android Activity Type 5
As we saw in the Mac example, if we look at the lower-right pane in Figure 9 above, we can see evidence that “ coffee blog.docx” was accessed from OneDrive using Word.
The devicePlatform here, however, is “Android,” indicating that the activity occurred on an Android system (here, a Pixel 3 phone). Again, in the upper-right pan,e we see that the Platform Device ID is blank, so we have no idea which Android system the activity originated on.

Figure 10: Android Activity Type 6
Also, as we saw in the Mac example, looking at an Activity Type 6 entry for the same activity we see that the activeDurationSeconds is zero, and the userTimezone is missing.
These caveats aside, being able to see evidence of activity that took place on Mac and Android devices from a Windows device that has been logged in using the same Microsoft ID, is still a significant win for forensics investigators. This is an artifact that even highly technical users are likely unaware of, making it potentially even more valuable.
Conclusion
To sum up, the Windows Activity Timeline sync functionality means that you may well find Windows machine evidence of activities that occurred on one machine occurring on other machines – even those that aren’t Windows-based – making it a potential game-changer in some situations.
You now have two valuable tools in Cellebrite Inspector and Cellebrite Digital Collector that can help you find evidence on either Android or Mac devices respectively. Add this technique to your arsenal, and happy hunting!
Learn more about how Cellebrite Inspector and Cellebrite Digital Collector can help advance your investigations, here .