
How iOS Properties Files Can Confirm a Suspect’s Contacts Even If Deleted
Determining a complete list of contacts that a person of interest has on their phone can be challenging due to factors like deleted data, inconsistent app communication records and device migration data loss. Because of these variables, it is important to find a reliable record of communications between two parties that is both permanent and legitimate for reference during an investigation and in court.
With this in mind, I was recently researching the Apple iOS Properties Files, and discovered that the file com.apple.identityservices.idstatuscache.plist located under var/mobile/Library/Preferences, contained caching records of Apple user ID authentication data.
See the file structure below as displayed in Cellebrite Physical Analyzer:
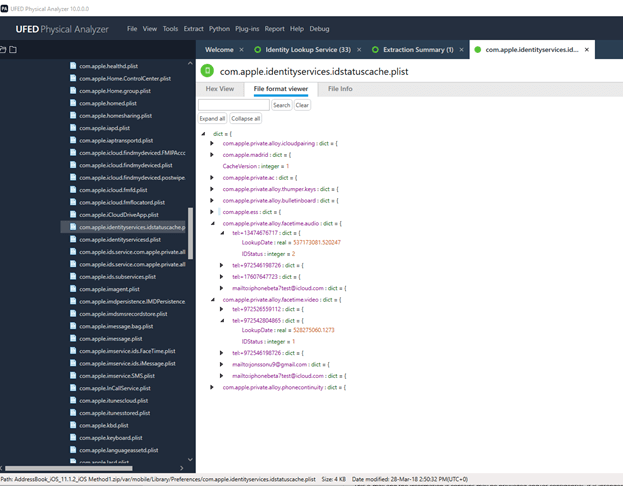

These records are significant as Apple device users of Facetime or iMessage input the Apple ID of another user the first time they attempt to contact them. When this occurs, the iOS references its Apple servers to validate the Apple User ID.
As a result of this process, a new file record is created with the Apple User ID in a phone-number or email format including a timestamp. This user authentication record in the file cannot be deleted from a phone.
How the DFIR Community can benefit
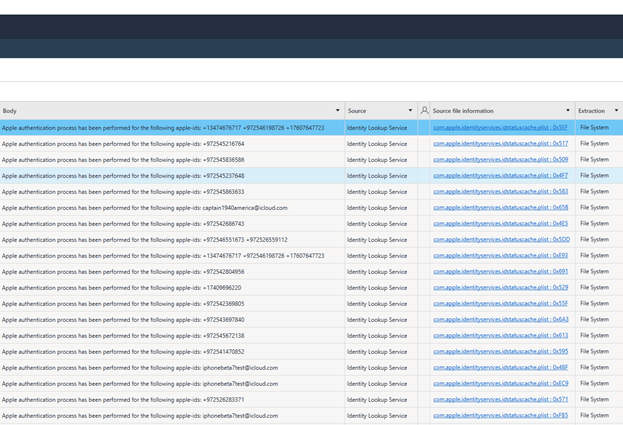
For digital investigators, this can be a vital source of digital evidence as the apple-id, communication type and timestamp can help confirm that two people have communicated with each other, and when their first communication occurred.
The authentication ping only happens once during the first instance that a user made an effort to contact another Apple user. Additionally, separate authentication records are recorded for each type of Apple communication service per device. This means that Facetime or iMessage communications are recorded separately at different times according to their first usage between users.
Even if data has been deleted from a phone’s directories or database, the authentication file remains intact, containing contact and communication records that can be parsed. It is important to note that this data only confirms that an authentication occurred but does not mean that a conversation happened or that a message was actually sent.
For example, when a person starts writing a message they could enter a recipients name and the authentication could occur so the record would appear in the database. If the person decides not to send the message, there would still be a record of an unsent message.
For members of the DFIR community, this capability was released on Cellebrite Physical Analyzer 7.19. This feature is especially useful when attempting to establish the first contact between two or more persons of interest who also have Apple User Id’s. In Cellebrite Physical Analyzer, this data is displayed as a log-entry with the relevant data: application, apple-id and timestamp.
View more details regarding the release of Cellebrite Physical Analyzer 7.19 which also brought support of new data sources that can help investigators surface key evidence related to case subjects, especially when an iOS device is involved.
