How to Safely Collect Digital Evidence with Advanced Emergency Download (EDL) Methods – Part 2
Qualcomm is the leader in the mobile chipset market with a 45% revenue share. This means that investigators or examiners will come across mobile devices using Qualcomm chipsets somewhere along the line during their digital forensics investigations.
Digital forensics officers must equip themselves with the tools and techniques that reliably overcome Android access challenges. Cellebrite has created the webinar, “Safely Collect Digital Evidence with Advanced EDL Methods,” because of the challenges associated with putting devices to enter into the useful emergency download mode (EDL mode).
In this webinar, you will learn how to apply advanced EDL methods to collect data from popular Qualcomm-based devices by lawfully accessing the device to provide a fast physical extraction.
This webinar is an in-depth demonstration follow-up to, “Access Mobile Device Evidence Faster Using EDL (Emergency Download) Part 1”.
We start the webinar by addressing the why and the how behind the theory of EDL mode. You will also get a brief review of how the Cellebrite UFED solution attempts to decrypt user data with EDL, and how this feature developed over the past 2 years.
The webinar will also provide a practical walk-through guide to best practices for detecting and triggering EDL. Finally, we will wrap up with an informative Q&A session.
Webinar Overview
Revisiting EDL Theory
EDL mode is Qualcomm’s rescue mode which is exposed when lab technicians introduce various triggers or when a device can’t boot. This mode is designed to allow low-level access to the chipset for device analysis, repair or re-flashing.
Some vendors also enable a way of forcing the device into this mode (most likely to help technicians) though this is not a recommended best practice. Understand what devices can be supported for EDL data collection and if the mobile devices will suffer any harm during this procedure.
Programmers (aka “Firehose”)
To start working with a specific device in EDL, you need a programmer. Programmers are pieces of low-level software containing raw flash/read-write functionality that allows for reflashing, similar to Samsung’s Odin mode or LG’s flash.
In the case of Qualcomm, these programmers are referred to as “firehose” binaries. The webinar will demonstrate how to match both the hardware and digital signatures required for communicating to a device through EDL mode.
EDL Data Collection in Cellebrite UFED
Cellebrite UFED already includes a wide set of over 200 programmers and growing, which automatically attempt to match a valid specific programmer for the connected device. The webinar will explain Cellebrite UFED’s lawful access methodology for several widely accepted chipsets to deploy its unique method to decrypt user data partitions.
Practical Review of EDL Data Collection Techniques
The webinar will talk about the different techniques to place devices into EDL mode, and then actually perform some data collections. You will learn the techniques of placing devices into EDL mode including Key combinations, ADB, fastboot, test points, and eMMC fault injection.
Checking a Device for EDL Mode in Device Manager
This webinar will explain how you tell if a device is in EDL mode, DFU mode (Handset Diagnostics Interface) or FTM (Factory Test Mode).
Decrypting or Non-decrypting EDL Data Collection
The webinar will discuss the difference between decrypting and non-decrypting data collections, when a battery is needed to proceed, and how to retain forensically sound evidence.
Precautions Required for EDL Data Collection
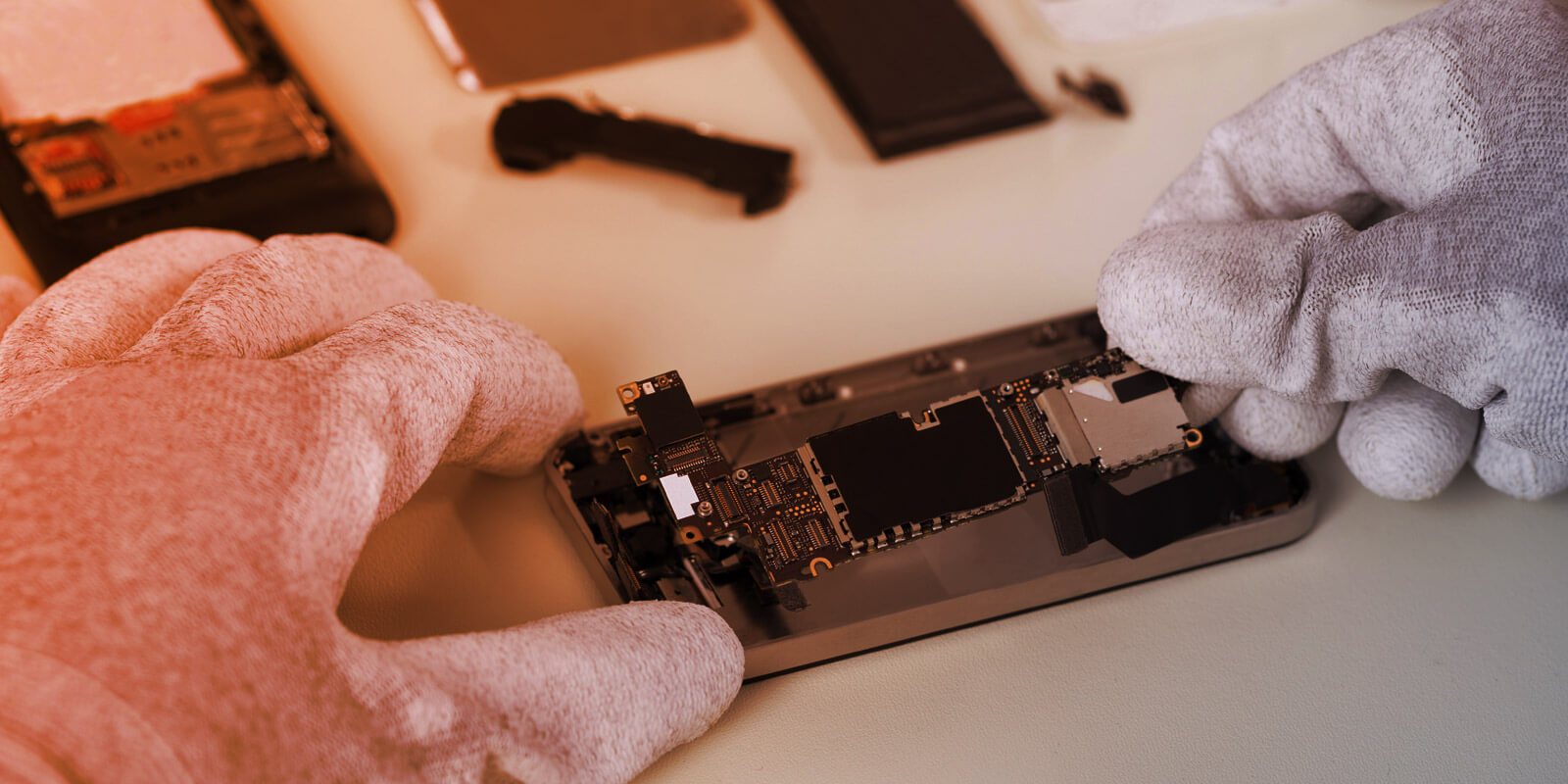
EDL mode is not harmful to devices. Devices can be placed in EDL mode many times without harming the device or affecting its normal operation. However, methods used to move devices into EDL mode can harm devices if done improperly without training, research or preparation.
The webinar will discuss common user-created damage scenarios and how to avoid them, such as incorrect device disassembly, removing heat shields and soldering practices.
To boost your practical application knowledge, Scott will perform multiple real-time data collections on ZTE and LG mobile devices using all of the recommendation scenarios mentioned above.
What’s Coming
In this section of the webinar, you will get an overview of what you can look forward to in the near future such as Secure Startup support, decrypting MTK, and new Samsung lock-bypassing decrypted physicals.
Get the Answers to Popular Question in the Q&A session
- Can EDL data collection be performed on phones without working screens or power and volume buttons?
- Are there differences between Qualcomm processors used in the US and Europe? And is the EDL method compatible with European processors?
- In what circumstances do you select non-decrypting data collection vs. decrypted data collection?
To register for this informative webinar, click here.
