Linux IR: Tips and Tricks for Rapid Triage

Special Guest: Hal Pomeranz, Deer Run Associates
In this episode, we are joined by Hal Pomeranz, an expert in the realm of Linux, who will be providing us with tips and tricks for Linux-type forensics and IR. Hal started out his career as a Unix System Admin in the 1980s and has been an independent consultant since 1997. Throughout the years, he has worked in digital forensics, incident response, expert witness, and multiple Linux/Unix investigations.
Hal has also created a two-day Linux Forensics class and will be using an excerpt from that class to talk about what to look for and how to find the needed information once your Linux image system mounts up. All the course materials, exercises, and sample forensic images are available for free here.
Identifying the Goal of the Attacker
Hal stresses the importance of “thinking like an attacker” in Linux forensics. It is extremely important to identify the goal of the attacker. Why do they want to successfully exploit the system? Mainly, they are looking to access the machine in order to run their malware.
They need to make modifications to the system in order to accomplish that mission and so we need to find recognizable signs of an intrusion. The attackers usually accomplish these goals using custom malware, web shells, and account modification.
Where to Begin
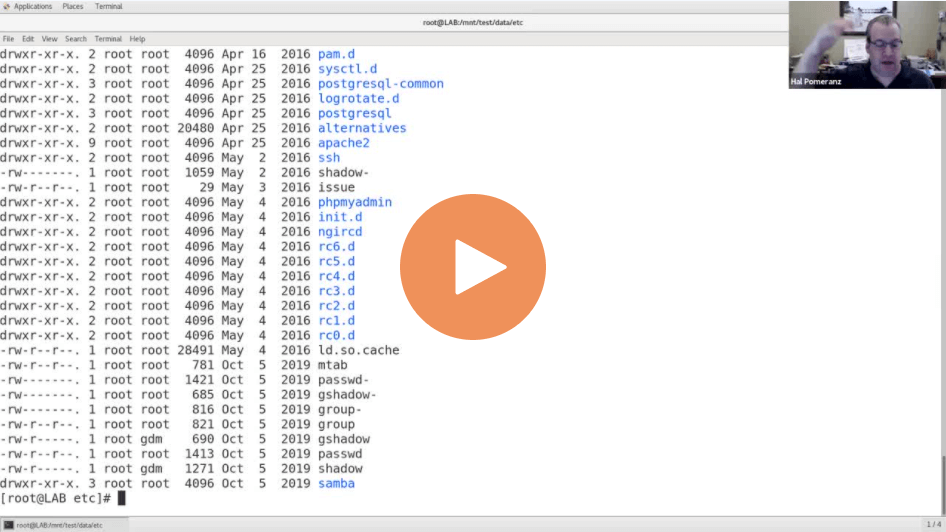
There are multiple places to start the forensic hitting. Some people like looking at the User Command History while others prefer diving directly into the log files. Hal suggests starting with the ETC directory of the system as that is where a large concentration of the configuration data in Linux is generally captured. In this directory, it is possible to find files that have recently been modified, which is a great starting point for the investigation.
Listen to the full episode to learn more about Linux-type forensics and to hear tips and tricks from an expert in the field.