Part 1: CTF 2022 Write Up – Marsha’s PC
We would like to say thank you to everyone who participated in the Capture the Flag. Also, a special thanks to Evandrix for his assistance in writing the tough questions and for Ian Whiffin for helping solve them. There were many late evenings and lots of hard work by many people involved. Ronen Engler was the fearless leader of this effort and on his behalf, I want to say thank you for playing this game. This is Cellebrite’s way of giving back to the community and providing resources to keep learning!
We wanted to provide a bit of a walk-through on how we came to the answers. There will be times in the blog that we mention, and reference blogs written by various community members who provided their own write-up about the CTF, and interesting enough, some paths to get to the answers aren’t the same way we got there, which is the beauty in forensics. The paths we take may differ, but the results are the same. Note: This blog will take about 25 mins to read.
The backstory:
Beth Dutton was invited to the Vienna Inn in Vienna, VA on July 21st at 5:00 PM and was arrested while there. She was invited by Heisenberg. Police arrested her for grand theft. Upon questioning Beth, she revealed that her sister, Marsha Mellos introduced her to Heisenberg and that he was responsible for stealing cars and she and her sister were innocent. They are in the cattle business in Montana and got mixed up with the wrong guy. Marsha has both a PC and an iPhone. Beth had an iPhone and Heisenberg had an Android. The interest here is auto theft and selling. Cash transfers matter.
Marsha’s PC Questions:
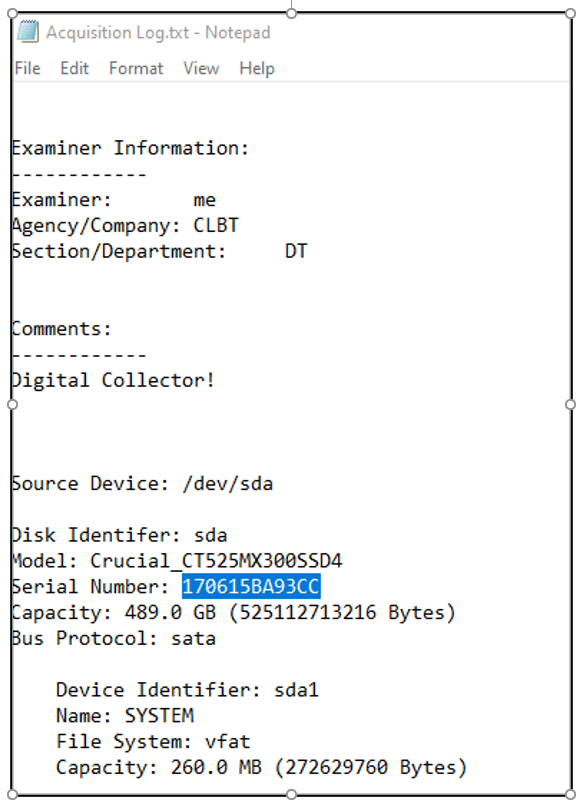
Question 1: Device ID (10 points) – What is the Serial Number of the disk acquired?
Flag: 170615BA93CC
The Acquisition Log.txt contains the answer to this and you may find that tools do not parse this information. We simply opened this file with Notepad.
Question 2: Keys (10 points) – How did the user most recently sign into Windows?
Flag: fingerprint
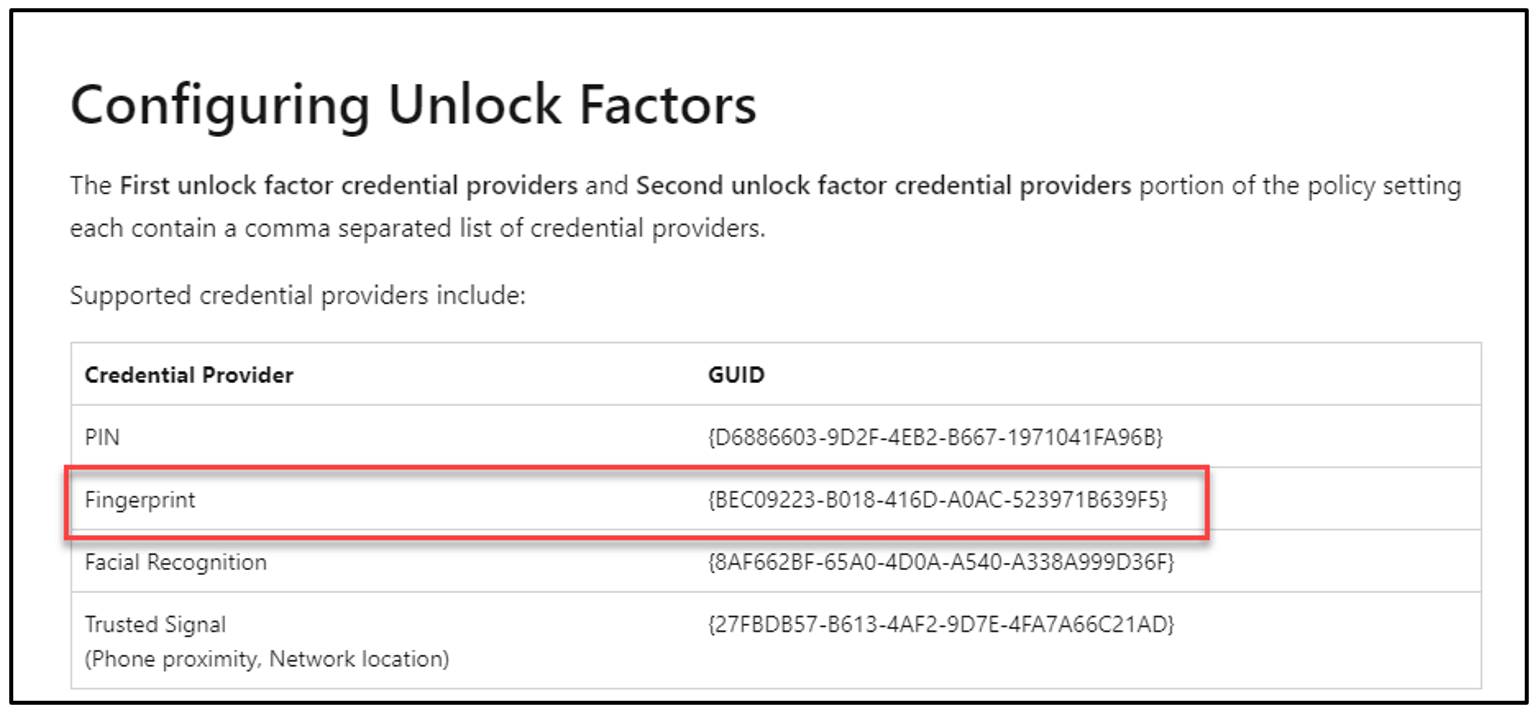
The Windows Registry is needed to answer this question. The Software Hive stores the answer and can be found at: HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\LogonUI – LastLoggedOnProvider {BEC09223-B018-416D-A0AC-523971B639F5}. Below, the top screenshot shows PA Ultra, and the second screenshot shows Cellebrite Inspector.
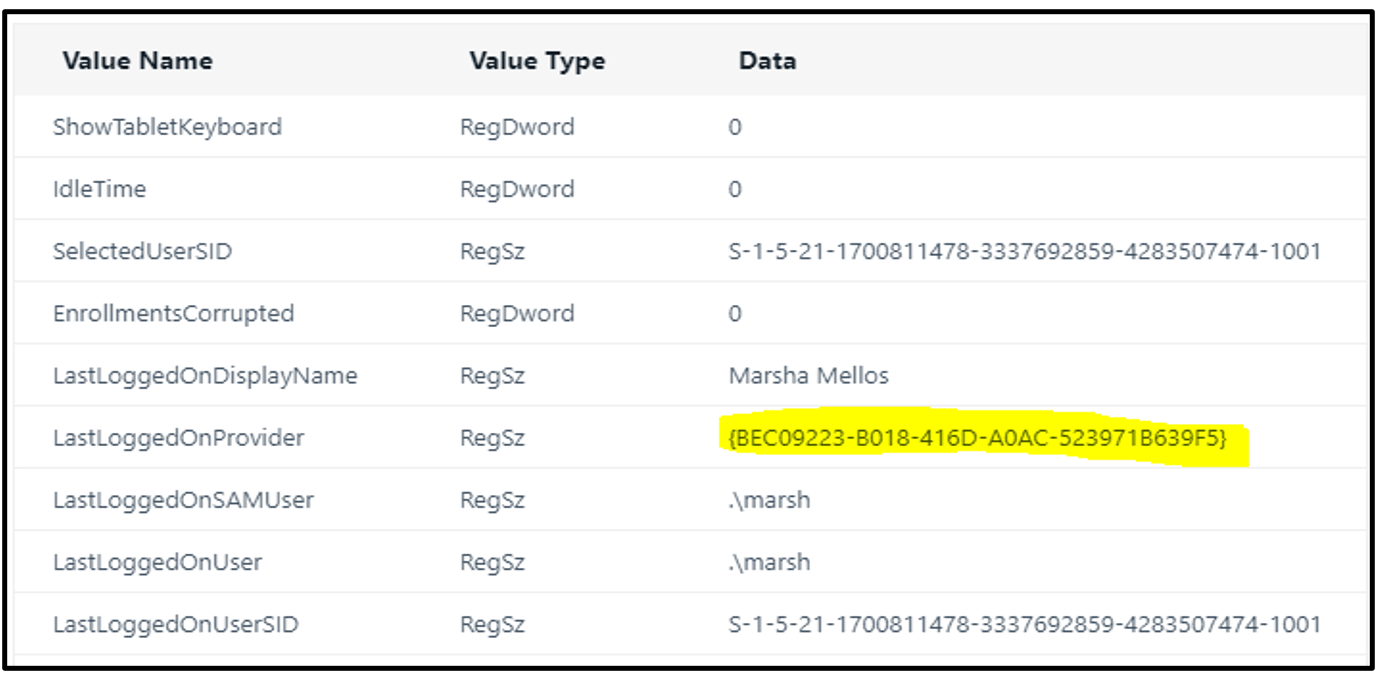
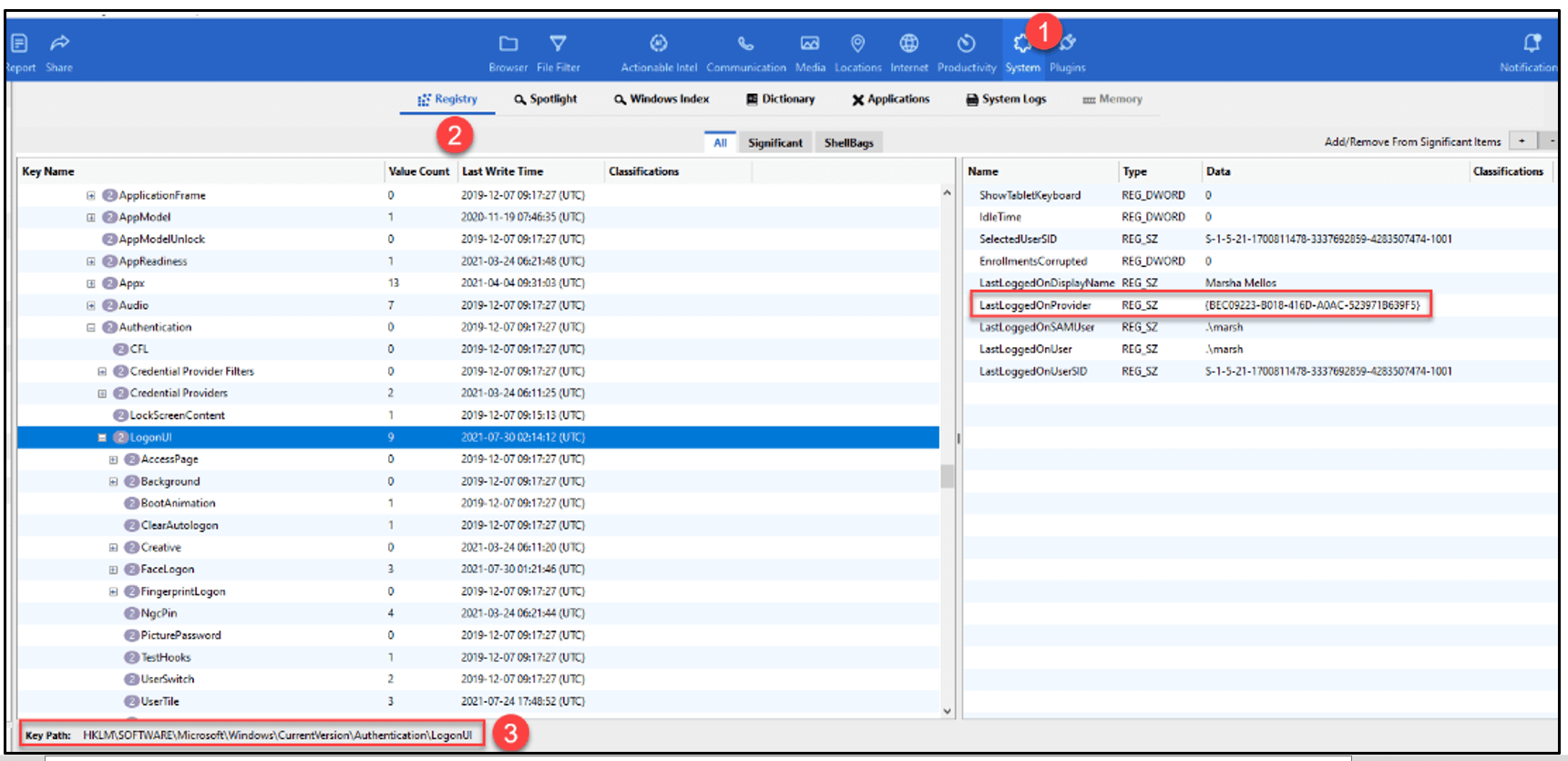
Once this is found, you can take the LastLoggedOnProvider and compare it to https://docs.microsoft.com/en-us/windows/security/identity-protection/hello-for-business/feature-multifactor-unlock or https://ronnydejong.com/2018/01/17/enable-windows-10-multifactor-authentication-with-windows-hello-multifactor-device-unlock-microsoft-intune Fingerprint {BEC09223-B018-416D-A0AC-523971B639F5}
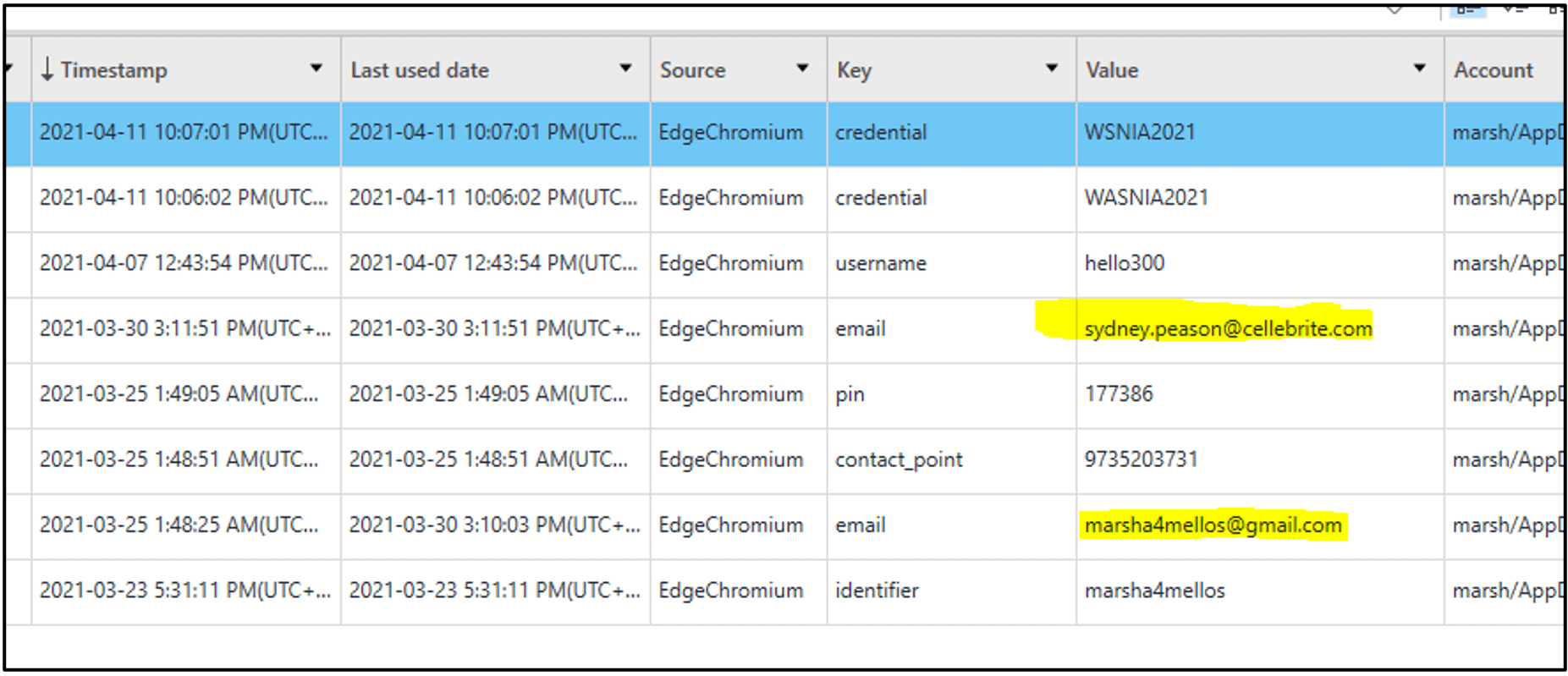
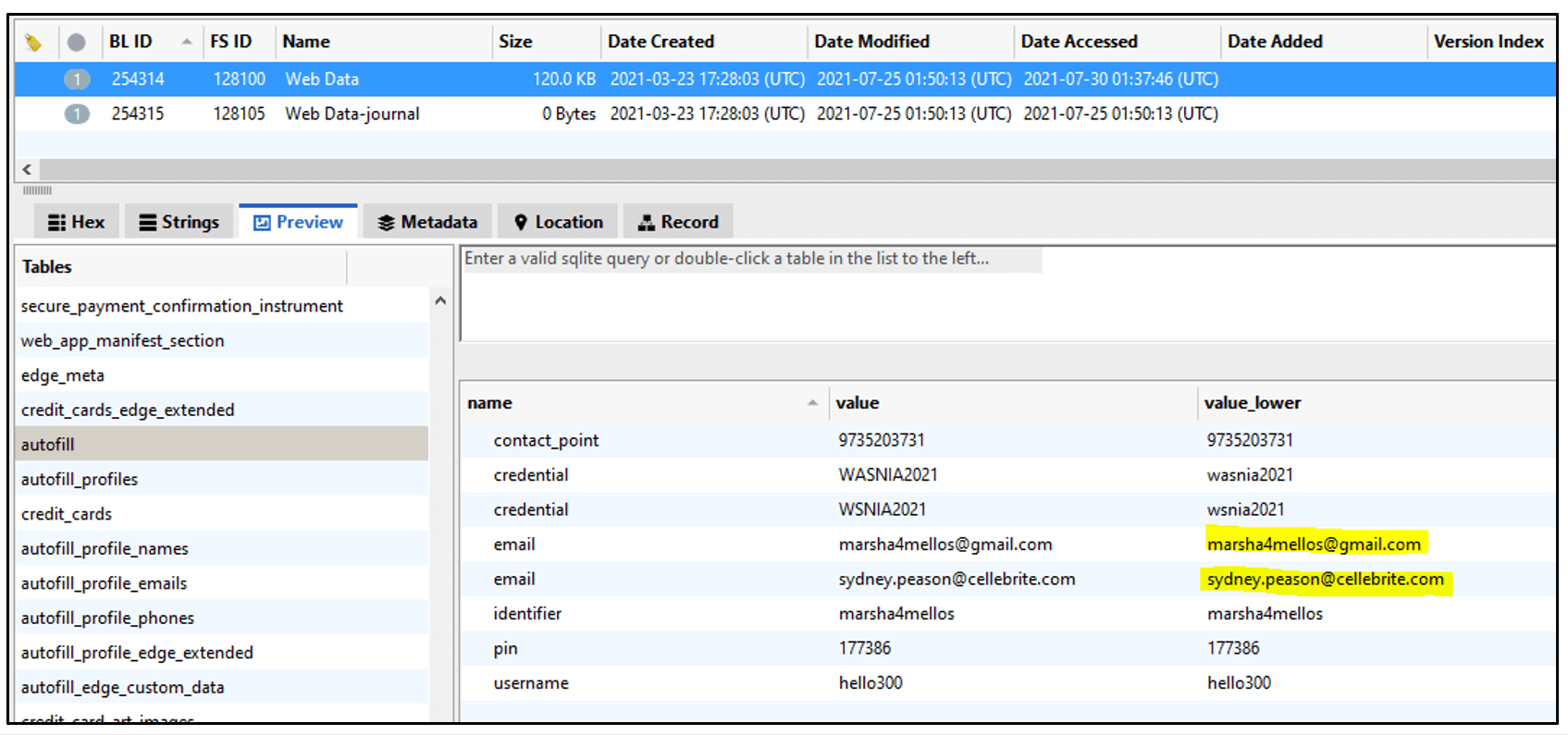
Question 6: WebForm (10 points) – What two email addresses were found in web forms?Format: [email address] [email address] e.g. john@gmail.com ryan@gmail.com
Flag(s): marsha4mellos@gmail.com sydney.peason@cellebrite.com
Cellebrite Physical Analyzer Ultra (PA Ultra) and Cellebrite Inspector parses this nicely, as seen below.
PA Ultra Results:
Inspector: /Users/marsh/AppData/Local/Microsoft/Edge/User Data/Default/Web Data
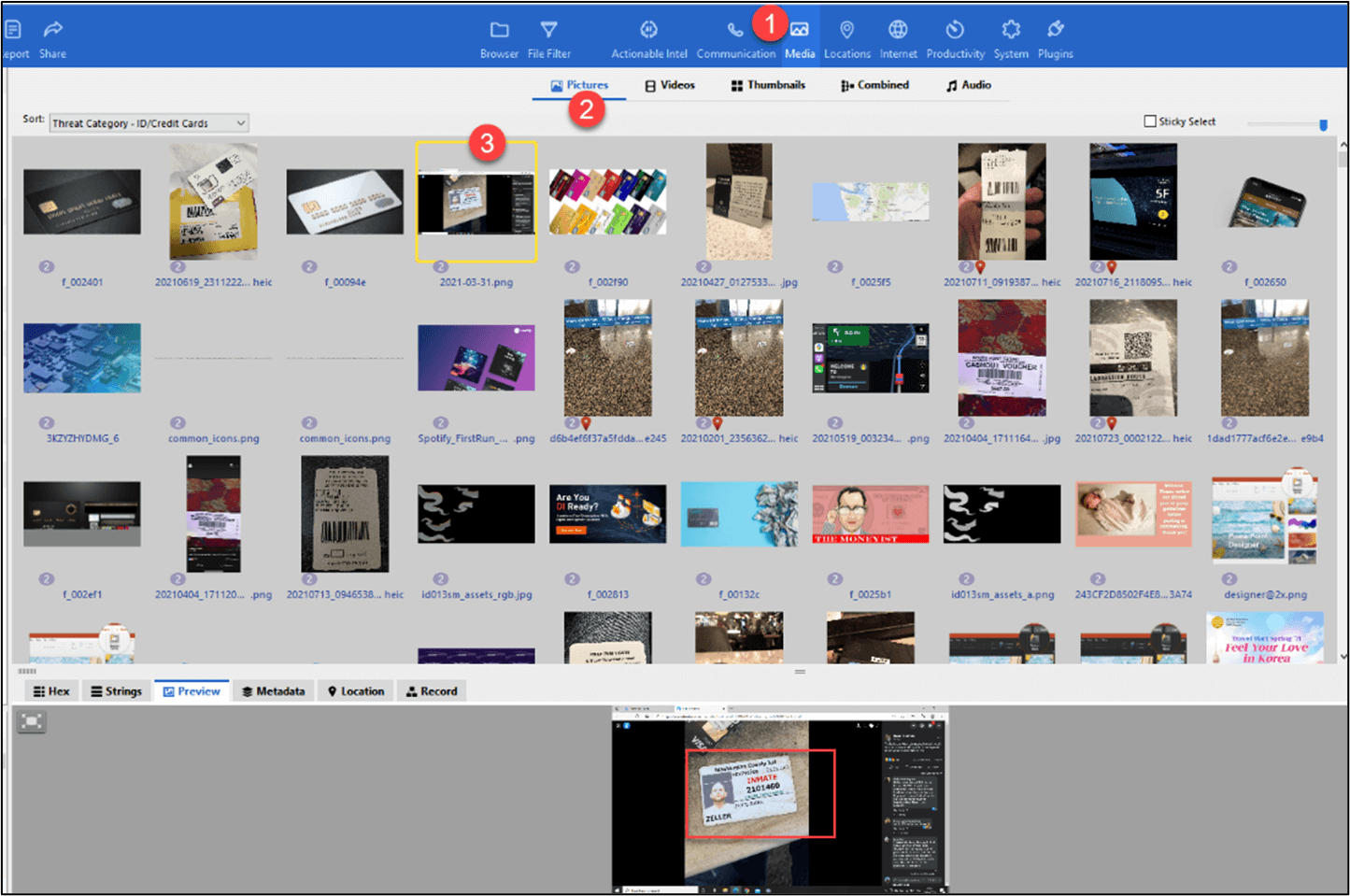
 Question 3: PII (10 points) – Someone stole a truck and left his inmate card behind. What is his inmate number? Hint: Check pictures.
Question 3: PII (10 points) – Someone stole a truck and left his inmate card behind. What is his inmate number? Hint: Check pictures.
Flag: 2101460
Cellebrite Inspector worked like a charm for this question. You can either use the Threat Category of ID/Credit Cards or filter for larger pictures as a starting point. Manual viewing of images found the inmate card for ZELLER. In Inspector, we quickly found this by going to Media>Pictures> and then sorted on Threat Category – ID/Credit Cards. We found the picture of interest in seconds. Keep in mind you must run media categorization during processing or after for this to work.
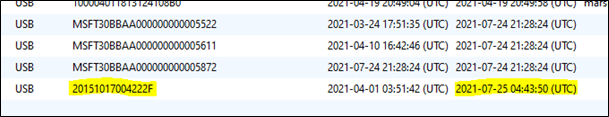
Question 4: Connected Devices (10 points) – What is the serial number of the last USB drive connected to the device, excluding acquisition tools?
Hint: Use timeline (may be an obvious hint – but it is the only user data that shows up for 2014)
Flag(s): MSFT30BBAA000000000005872 or 20151017004222F
Cellebrite Inspector was used to finding the connected devices. This can easily be done in the Actionable Intel data model within the toolbar.
Device Connections > Sort by Last Connected Date. Two answers were acceptable as one was a USB hard drive and the other was a USB thumb drive.
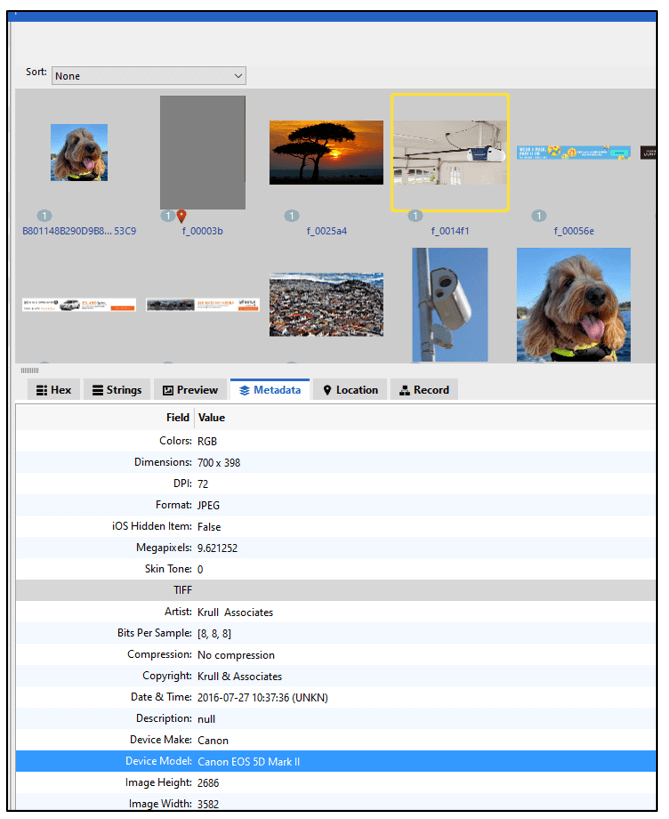
Question 5: Camera (10 points) – What is the only camera model that was found within a picture created by the user browsing the Internet? e.g. 1 3 01-22-2019 19:46
Hint: Check cache directories.
Flag(s): Canon EOS 5D Mark II or EOS 5D Mark II
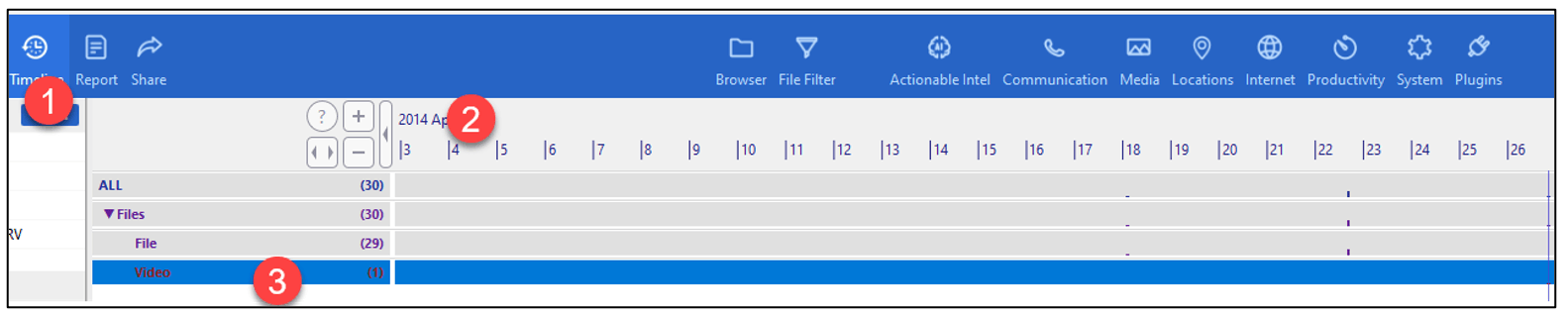
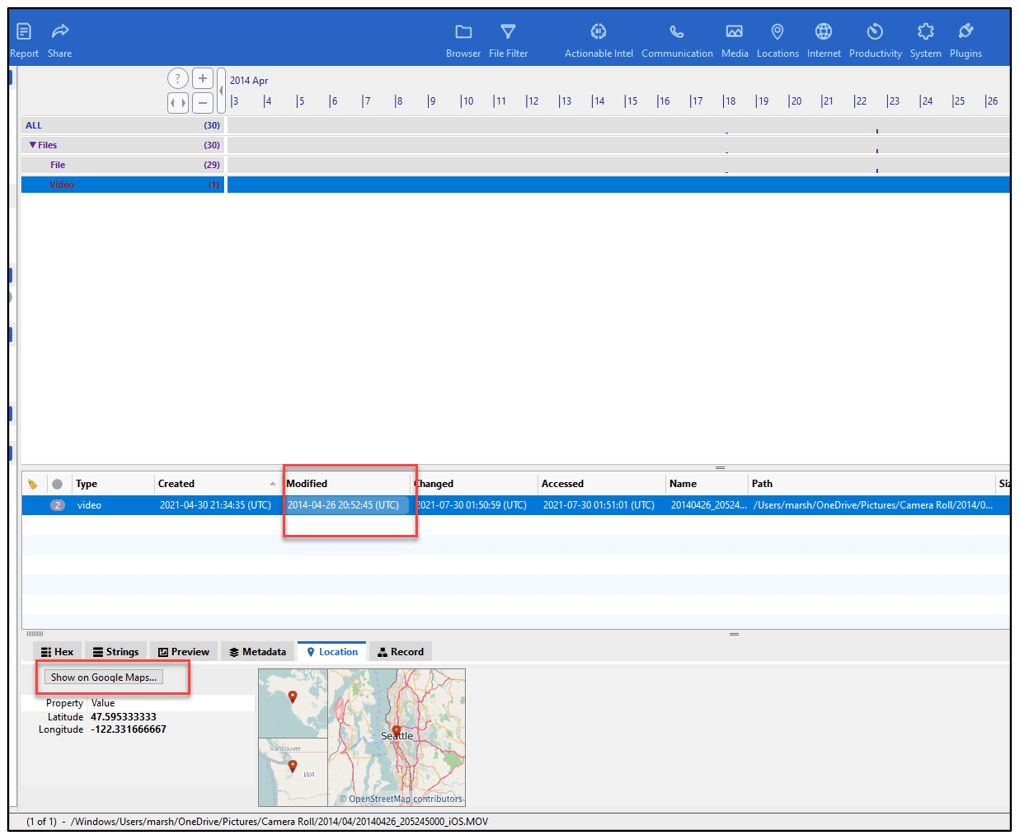
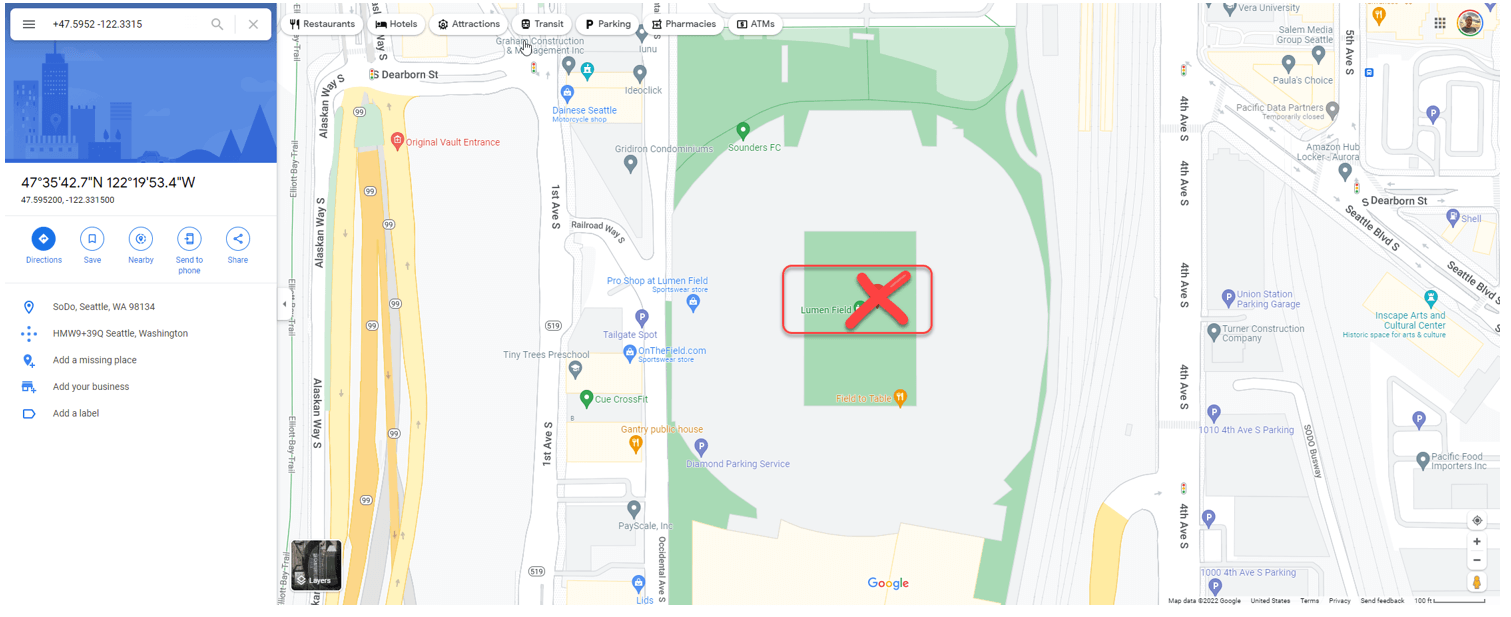
Question 8: Events (20 points) – The target captured a sports game that took place in April 2014. What was the name of the venue (**at that time**) and the name of the guest team? Format: [Name of stadium] [guest team] eg: Mercedes Benz Stadium Atlanta Falcons.
Hint 1: Use timeline (may be an obvious hint – but it is the only user data that shows up for 2014)
Hint 2: Check videos
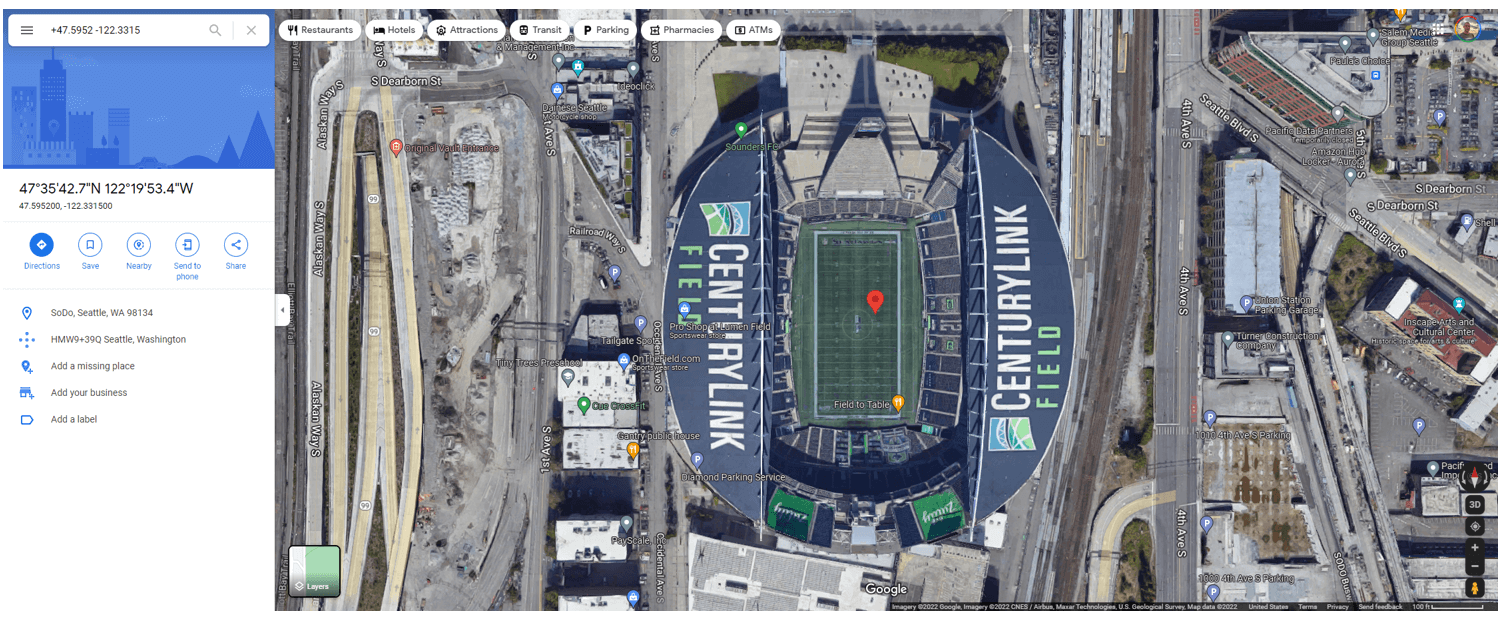
Flag: CenturyLink Field Colorado Rapids (accepted in many formats of word spacing) There are many ways to get this answer. For this, we simply checked media for 2014 and found a video 20140426_205245000_iOS.MOV of a soccer match. This was completed in PA Ultra. GPS given as +47.5952-122.3315+005.436. We trimmed it to +47.5952, -122.3315 which is “CenturyLink field” in Seattle. Google was used to search for the game played at Centurylink on 26th April 2014 and found the answer Colorado Rapids.
In Inspector the timeline can be used to help find the answer. Follow the steps defined above to map the coordinates based on the date of interest.
Please note that if you use google maps – the new name (Lumen Field) is shown, which is not the correct answer:
Switching to an older satellite view may show the correct answer:
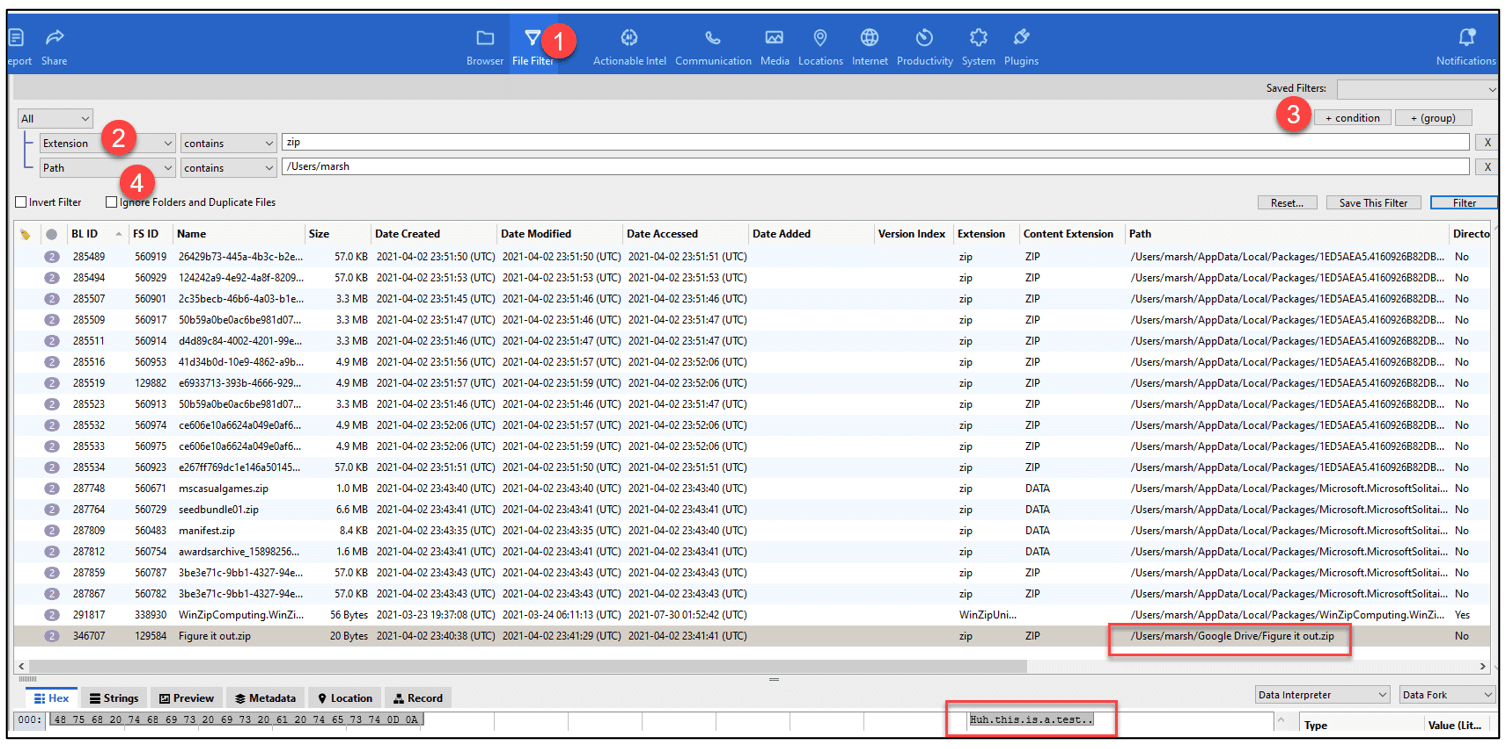
Question 7: File (20 points) – What is the content of a user-made file where the file extension is a mismatch?
Hint 1: located within the User(i.e. marsh’s) folder on C:\ drive
Hint 2: ZIP archive file extension
Flag: Huh this is a test or Huh this is a test.
Start by taking the hints if this didn’t come easy to you. In Inspector we created a Filter for Extension contains zip. Next, create Filter for Path contains ‘’/Users/marsh’’. Only one file exists in a common path where users could store files. Figure it out.zip is the file of interest.
Question 9: Collector (20 points) – How many unique acquisition tools were recognized by Marsha’s PC, how many times did the acquisition tools connect, and when was the last time an acquisition tool was connected? Format: [unique #] [total #] MM-DD-YYYY HH:MM e.g. 1 3 01-22-2019 19:46
Flag(s): 3 6 07-24-2021 21:28How many unique acquisition tools were recognized?This question caused a lot of confusion, and we apologize for that. Different tools provided different answers, which is why testing and validation matter! The terminology tripped things up a bit as well because last connected and last inserted have different dates. In PA Ultra: USB Device Parser > Filter by “macq” shows 3 results.
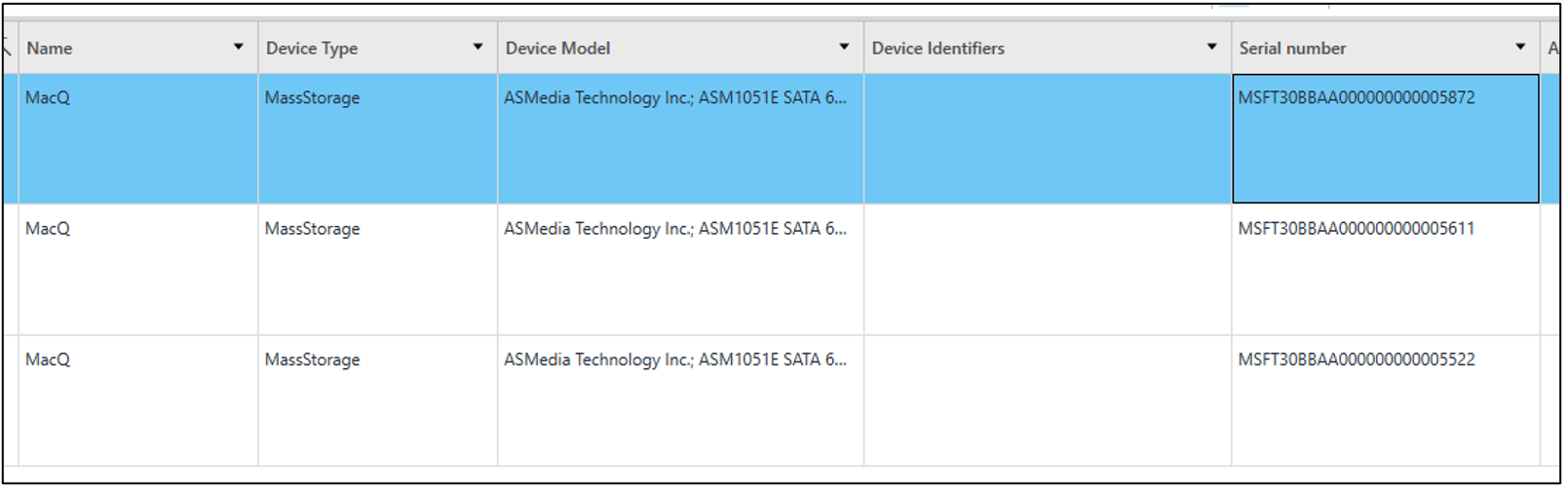
Inspector shows the same 3, although it’s not as obvious as it doesn’t pull the “macq” label.
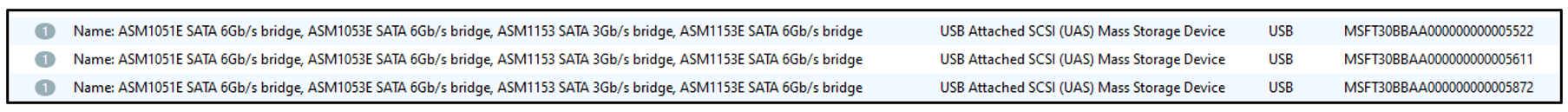
Other tools were used as well and all seemed to agree that “3” is the first answer.
How many times did they connect? / Last Connection?
In PA Ultra > Device Connectivity > filter by “macq”. Shows 6 results and the last one is 30th July 2021 at 01:21:55.
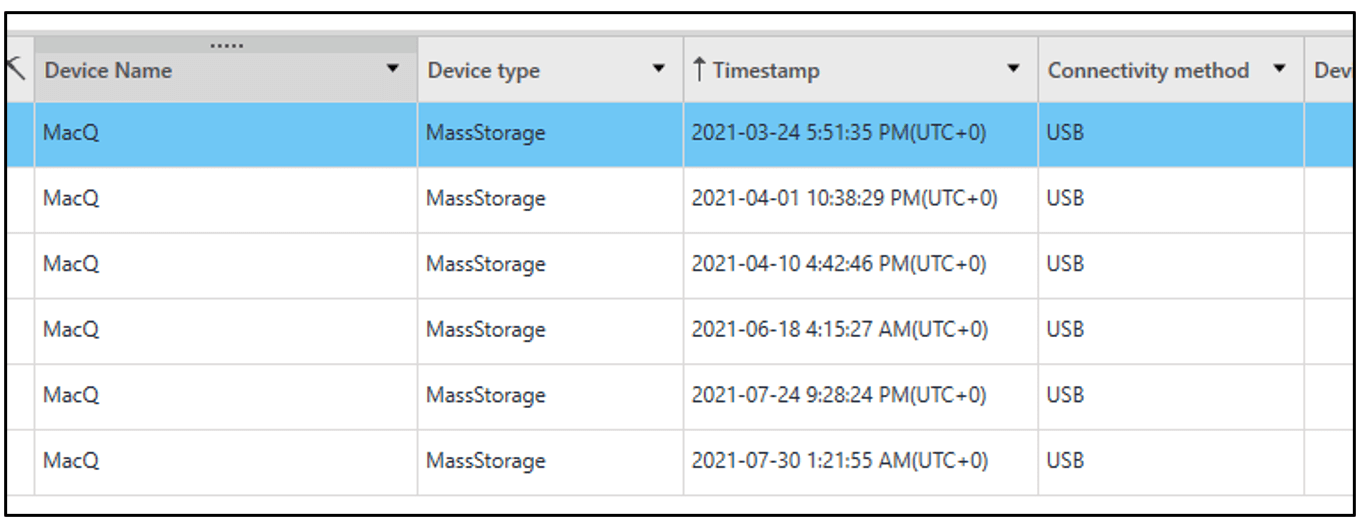
In Inspector > Actionable Intel > Correlation > Filter by Event Type = “inserted” & Description = “MSFT30BBAA”. Only shows 5 results, the last of which is 24th July.
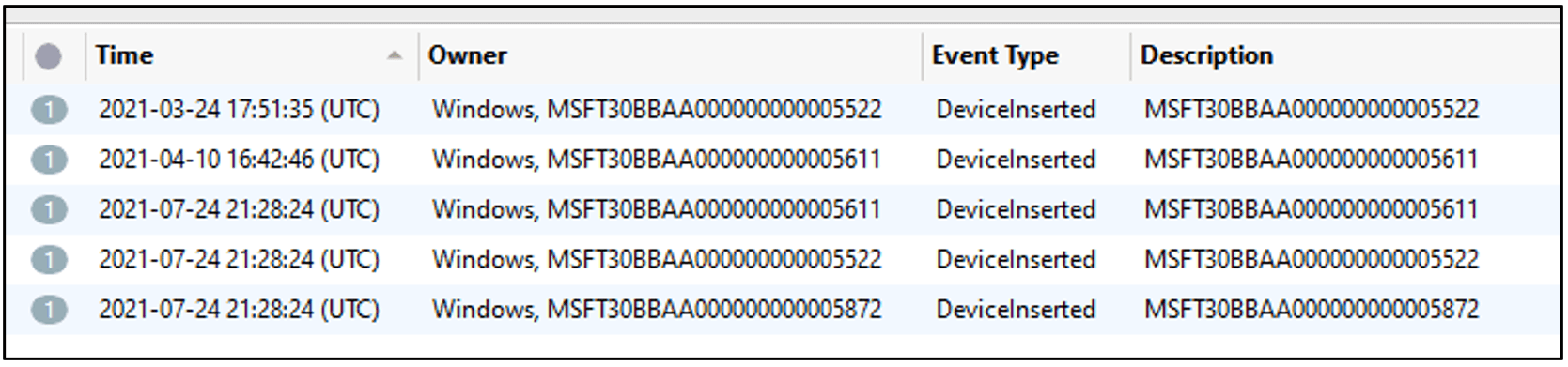
But, altering the filter a little to Filter by Event Type = “inserted” & Description = “AA” we see LOTS more results, including
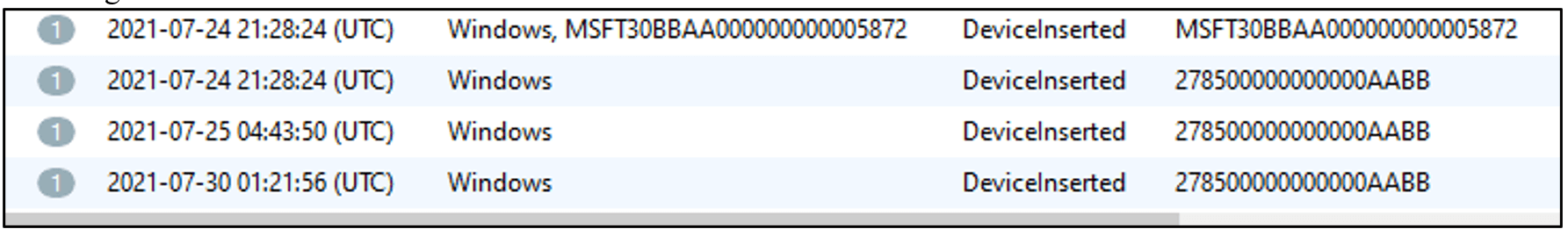
Note the descriptions are the reversed serials and shows the same last timestamp as PA Ultra (1-second difference). Other tools can be used as well to examine the Windows Events Logs > Storage Device Events and filter Model = “macq” there are 24 Connection events. USB Connections shows the latest LAST CONNECTION time as 24th July 2021 21:28:24 which matches Inspectors initial answer.
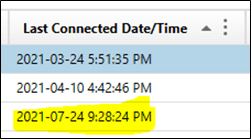
But scrolling across a little shows the LAST INSERTED time that matches PA’s answer and Inspectors secondary answer:
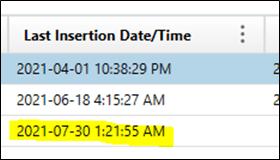
The answer to when it was last connected, is either 24th July 2021 21:28:24 or 30th July 2021 at 01:21:55 depending on which tool you use, or your definition of Connected vs Inserted.
Question 10: Code (50 points) – What is the Windows Hello PIN code of the user signed into the Windows PC with a Microsoft account?
Flag: 134679There is a quick and dirty way of getting this answer if you look at PhoneInfor.txt where it’s blatantly listed.
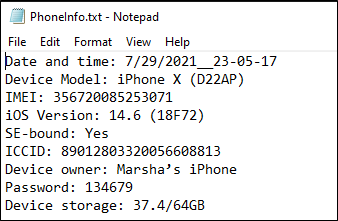
Two links that will help you find this the tough way are shown below. These steps are complex and you may wish you found the cheat-code as we showed above.
https://github.com/Banaanhangwagen/WINHELLO2hashcat
Installation of both WINHELLO2Hashcat (which requires Python) and Hashcat is outside of the scope of this answer but can easily be found online. We will be using the WINHELLO2 Hashcat tool to extract the PIN hashes so that HashCat can advanced access the hash for us to get the answer.
There are 2 ways to go about obtaining the hashes.
- Via a VM
Use a tool such as FTK Imager to mount the e01 as Logical WRITABLE drives. It must be writable because we are about to change some permissions on the drive. Bear in mind, the E01 is NOT being altered here, just the cache file that FTK creates, so there is no danger to the evidence.
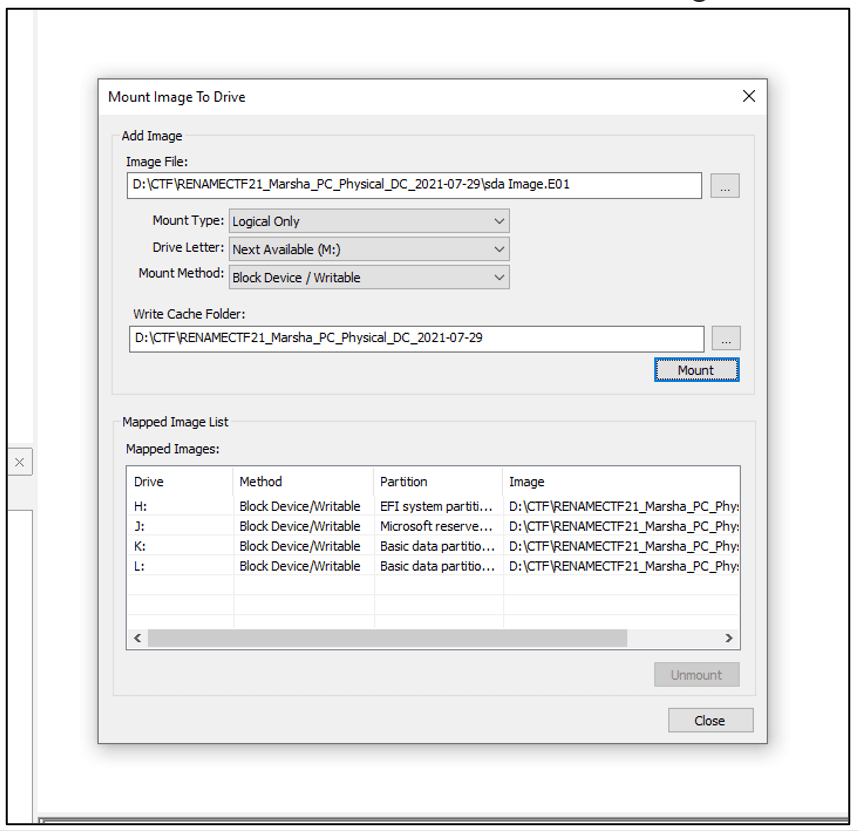
All drives will mount, but we only care about the Windows drive, which is mounted for me as drive K:
The github https://github.com/Banaanhangwagen/WINHELLO2hashcat details what to do if you are running from a mounted image because you need permissions to the secure folders. It gives you the two commands required:
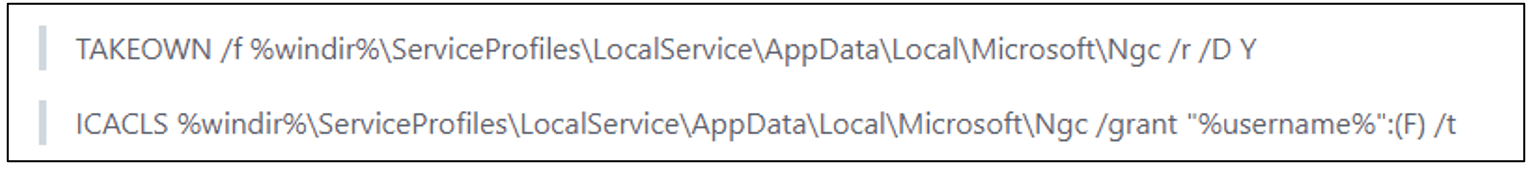
This needs to be modified to work on the mounted drive. This is as simple as removing %windir% and replacing it with k:\windows. Now we take ownership of the files/folders (and their children) by running:
TAKEOWN /f k:\windows\ServiceProfiles\LocalService\AppData\Local\Microsoft\Ngc /r /D Y
And then we give ourselves permissions to the same using:
ICACLS k:\windows\ServiceProfiles\LocalService\AppData\Local\Microsoft\Ngc /grant “%username%”:(F) /t
Now we can run the WINHELLO2hashcat script downloaded from the same github. The command argument listed is:
WINHELLO2hashcat.py [–verbose] –cryptokeys <crypo keys directory> –masterkey <user masterkey directory> –system <system hive> –security <security hive> [–pinguid <pinguid>|–ngc <ngc directory>] [–software <software hive>]
Many of these options are if you have the files rather than the mounted drive. Since we have it mounted, we can just run it and point it to our mounted drive.
py WINHELLO2hashcat.py –windows k:\windows
The script runs and extracts the hashes of the PIN and puts it in a format ready for Hashcat to take over.
2. Without a VM
Alternately, as mentioned above, you can do this same process without mounting the image. As per the instructions from the github, we need to extract a bunch of files & folders, namely:
- \Windows\ServiceProfiles\LocalService\AppData\Roaming\Microsoft\Crypto\Keys·
- \Windows\System32\Microsoft\Protect\S-1-5-18\User·
- \Windows\System32\config\SYSTEM·
- \Windows\System32\config\SECURITY·
- \Windows\ServiceProfiles\LocalService\AppData\Local\Microsoft\Ngc·
- \Windows\System32\config\SOFTWARE
We created a dedicated folder to dump all these items into:
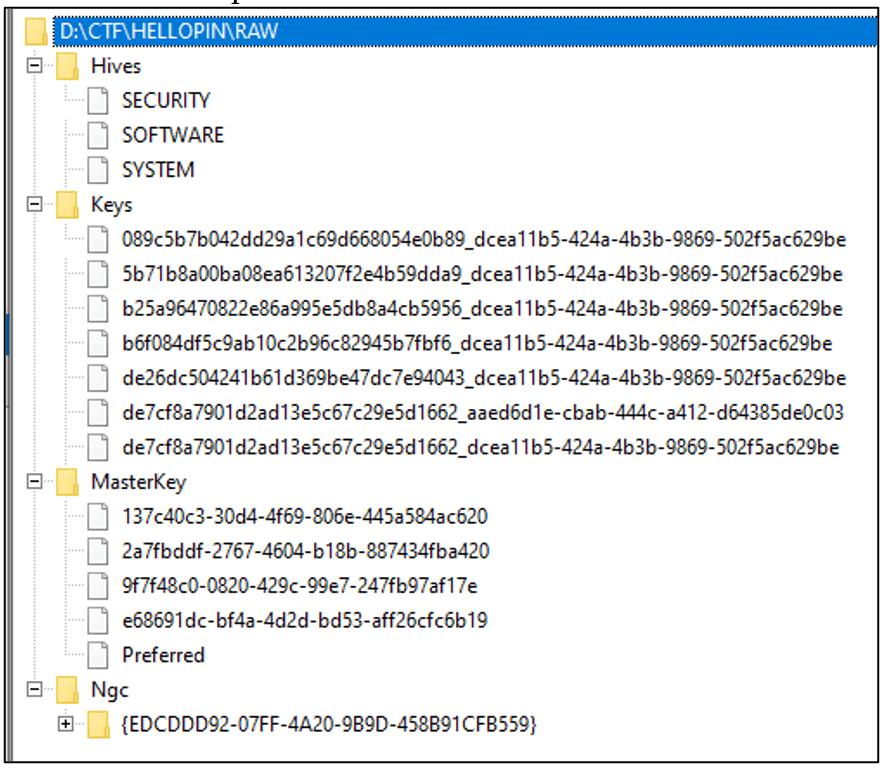
Next, alter the arguments to point now to the individual files/folders: py WINHELLO2hashcat.py –cryptokeys “D:\CTF\HELLOPIN\RAW\Keys” –masterkey “D:\CTF\HELLOPIN\RAW\MasterKey” –system “D:\CTF\HELLOPIN\RAW\Hives\SYSTEM” –security “D:\CTF\HELLOPIN\RAW\Hives\SECURITY” –ngc “D:\CTF\HELLOPIN\RAW\Ngc” –software “D:\CTF\HELLOPIN\RAW\Hives\SOFTWARE”
Again, the tool will pull out the hashes into a format ready for Hashcat.
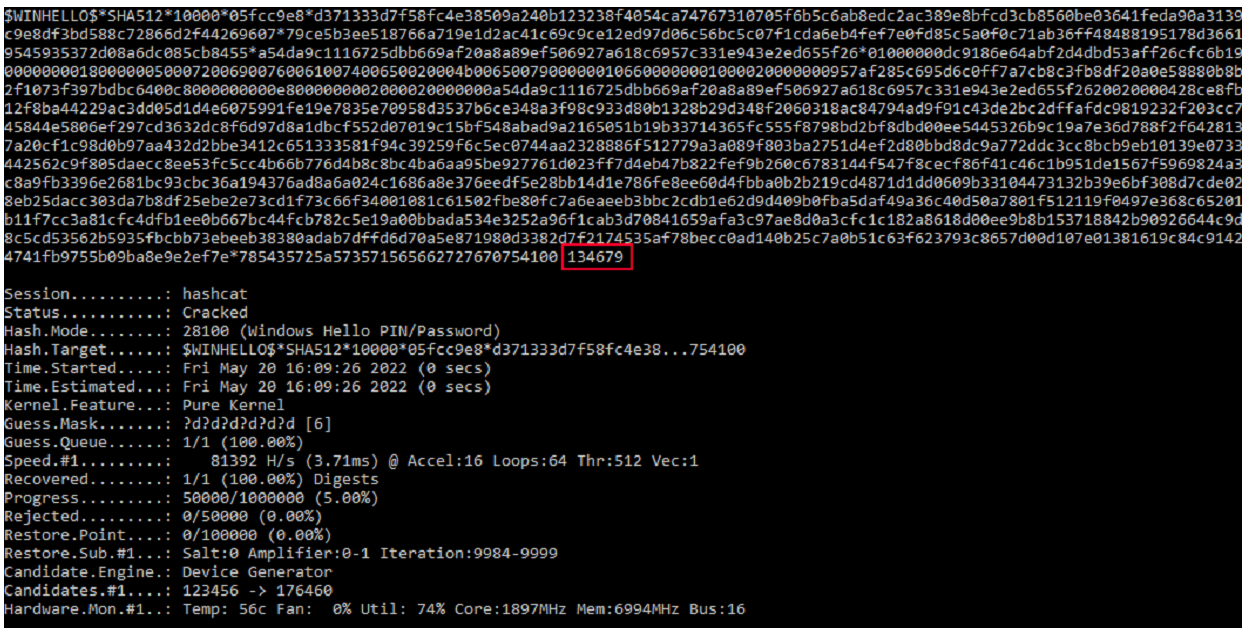
Either way, it’s approached, the result is the same which can be copied/pasted to a new text file which we called hash.txt. Now we need to move over to HashCat. We already have the hash file and know from the github above that we need to use -3 28100 plugin. So, we already have the executable, the plugin and the hashfile:
hashcat.exe -m 28100 “D:\CTF\HELLOPIN\hash.txt”
This would likely work, but will take a long, long time. We want to provide some more parameters to make this quicker and since we know we are looking for PIN code, we know it’s numeric only. We can also assume it is either 4 or 6 digits (although if you really want to investigate it, load the VM again and see how many digits it takes on the logon screen before it automatically submits). We will use Mask attack (ATTACK MODE 3) which is specified with the argument -a 3 and we will also specify a mask of only numeric values by using ?d for each digit. So to test a 4 digit PIN the mask would be ?d?d?d?d and a 6 digit pin would be ?d?d?d?d?d?d
So the complete command is either
hashcat.exe -m 28100 “D:\CTF\HELLOPIN\hash.txt” -a 3 ?d?d?d?d
for a 4 digit pin or
hashcat.exe -m 28100 “D:\CTF\HELLOPIN\hash.txt” -a 3 ?d?d?d?d?d?d
for a 6 digit pin.
The attempt to crack a 4-digit pin exhausts all possible codes within a few seconds and fails to find the answer. We move on to try 6-digit pin and it completes just as quickly as the first time, but this time, we see the answer 134679.
Question 11: IDs (100 points) – What is the Personal Meeting ID of the Zoom user account holder?
Hints: It’s not simple nor easy Flag: 81714328207
This one was tough! The answer is in the encrypted database “zoomus.enc.db”, but to read this database, you will need Marsha’s MasterKey from a VM.
The following resources may be of help:
- https://it-forensik.fiw.hs-wismar.de/images/8/8e/MT_OHoffmann.pdf
- https://www.reddit.com/r/computerforensics/comments/kch7ot/zoom_artifacts_encrypted_dbs
- https://github.com/tijldeneut/dpapilab-ng
Step 1 – Extract the Zoom Encryption Key
Extract the following files:
- Windows/Root/Users/marsh/AppData/Roaming/Zoom/data/zoomus.enc.db
- Windows/Root/Users/marsh/AppData/Roaming/Zoom/data/Zoom.us.ini
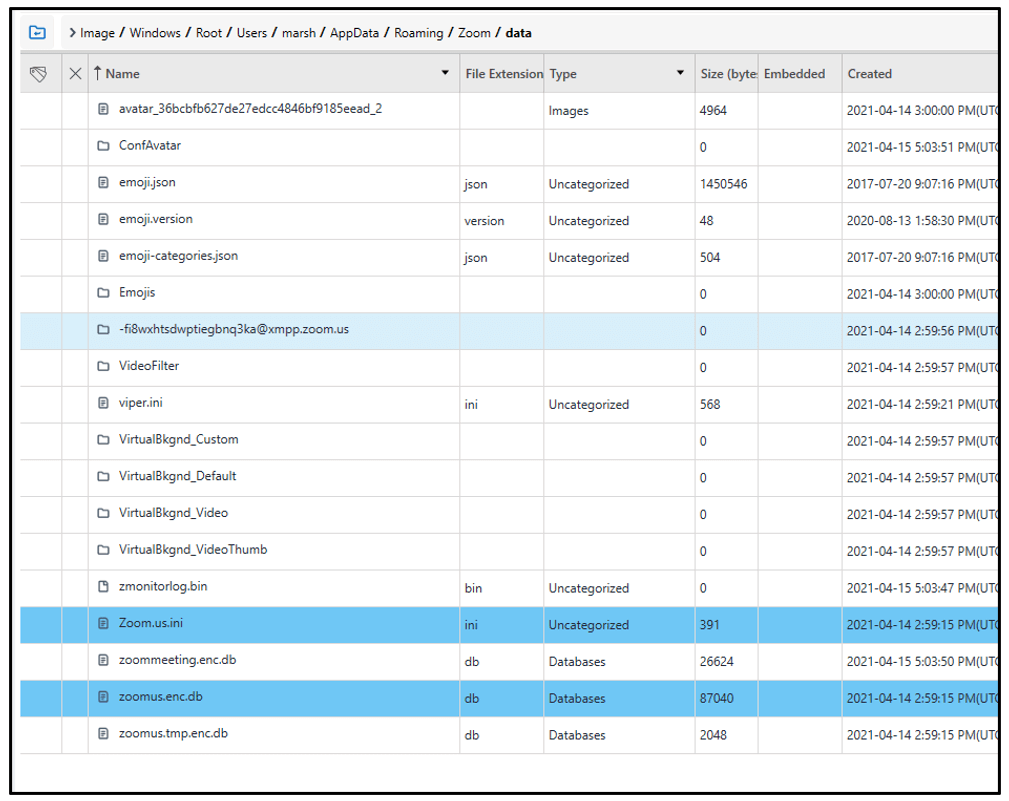
Open the Zoom.us.ini file to extract the win_osencrypt_key value:
ZWOSKEYAQAAANCMnd8BFdERjHoAwE/Cl+sBAAAAN0wJws7A4EyY/lPgmlU9NQAAAAACAAAAAAAQZgAAAAEAACAAAABpDI8XS07wR6GQwv5N2VBlNGB1DQwTcFjpScQwmFiNvgAAAAAOgAAAAAIAACAAAACfbLWwMYxJQedFumm5qQeAUg7MAuCHhd89pMkUwuEp1TAAAAC3oDDqmxxb7usbEQdURdXvuSWx3tSmBn0BZfdOYd1iFZmXu/EXJoh09/37z2YM5iJAAAAA9VIw30eaBS4olqrMlQvzDrV5rji3TNUFFd14/5NQbHwre9nmMSM6wg1+BNU2Xj5KFcjtJWWBLD+bU3qF+rDScw==
Remove the first 7 characters i.e. “ZWOSKEY” to be left with:
AQAAANCMnd8BFdERjHoAwE/Cl+sBAAAAN0wJws7A4EyY/lPgmlU9NQAAAAACAAAAAAAQZgAAAAEAACAAAABpDI8XS07wR6GQwv5N2VBlNGB1DQwTcFjpScQwmFiNvgAAAAAOgAAAAAIAACAAAACfbLWwMYxJQedFumm5qQeAUg7MAuCHhd89pMkUwuEp1TAAAAC3oDDqmxxb7usbEQdURdXvuSWx3tSmBn0BZfdOYd1iFZmXu/EXJoh09/37z2YM5iJAAAAA9VIw30eaBS4olqrMlQvzDrV5rji3TNUFFd14/5NQbHwre9nmMSM6wg1+BNU2Xj5KFcjtJWWBLD+bU3qF+rDScw==
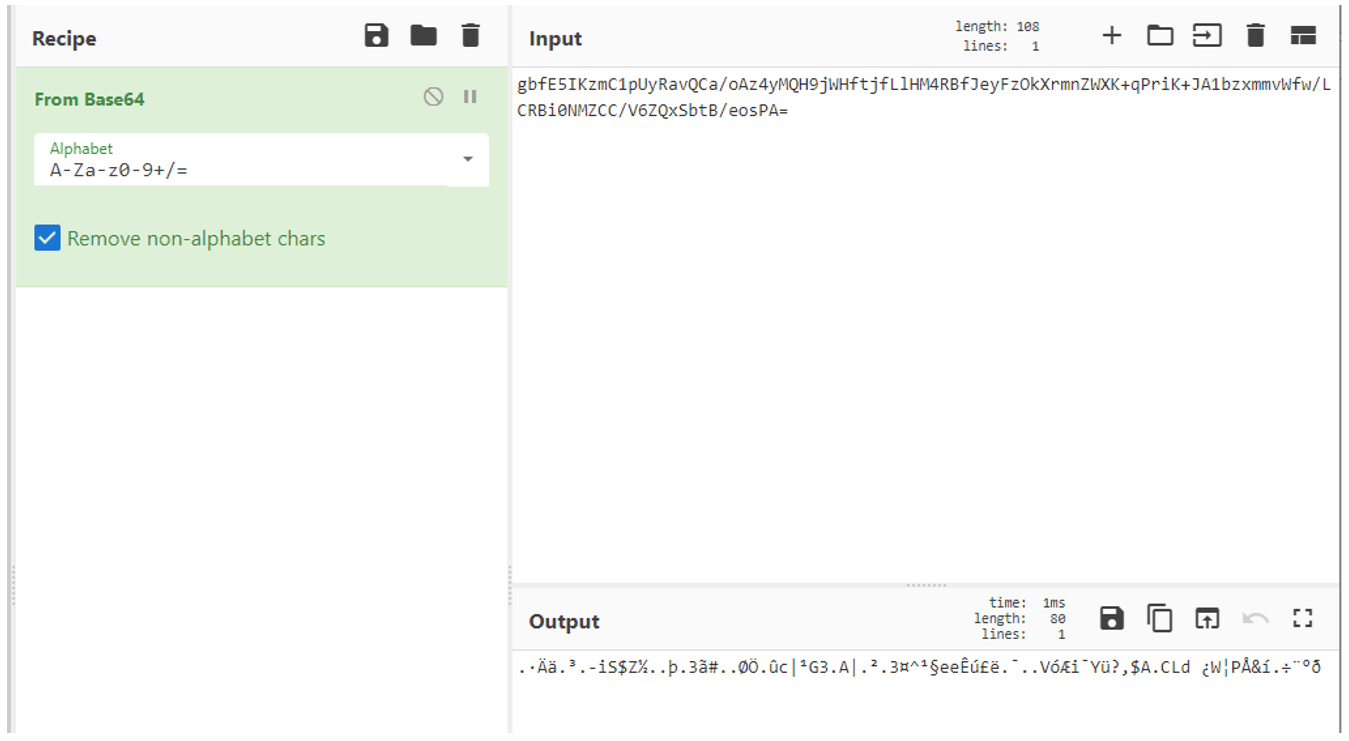
Use CyberChef (GCHQ) to decode “From Base64”:
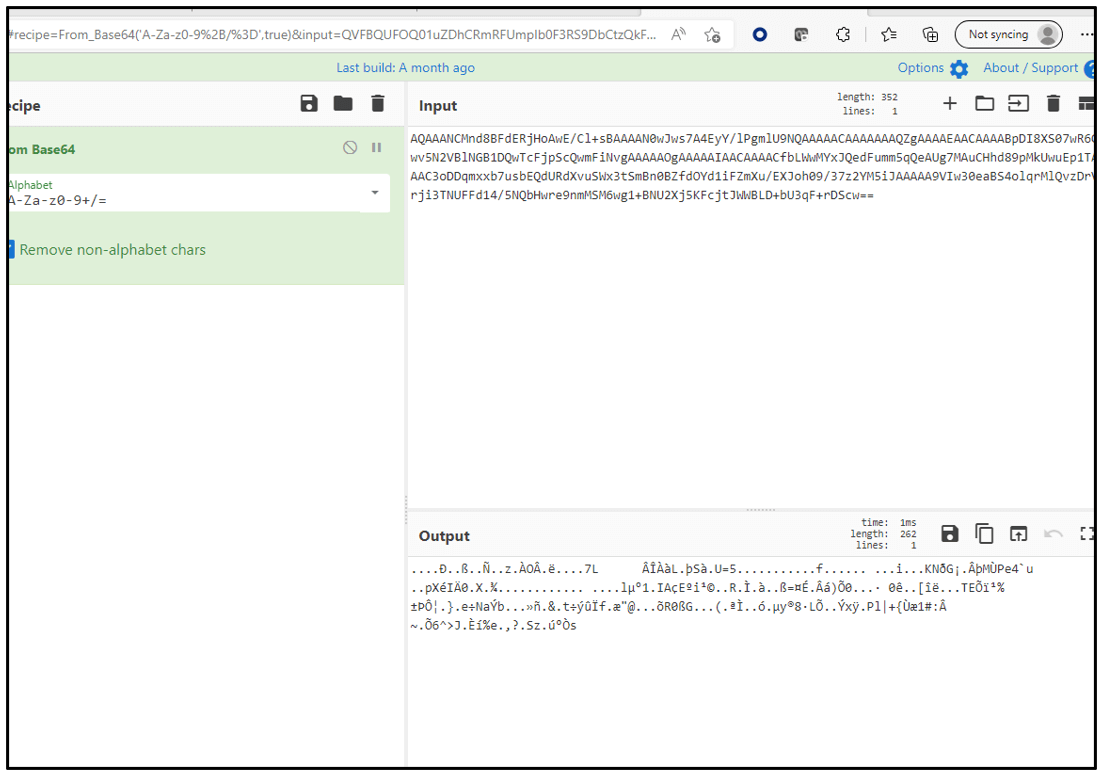
Save the result to a file. I named it “download.dat” – the filename that CyberChef automatically assigns.
Step 2 – Obtaining the Windows Masterkey for Marsha’s account
Mount the provided E01 evidence image as a VM to access the device, using the Windows Hello PIN 134679.
Copy Mimikatz https://github.com/gentilkiwi/mimikatz to the VM and run it as Administrator.
Run the command # privilege::debug
followed by # sekurlsa::dpapi
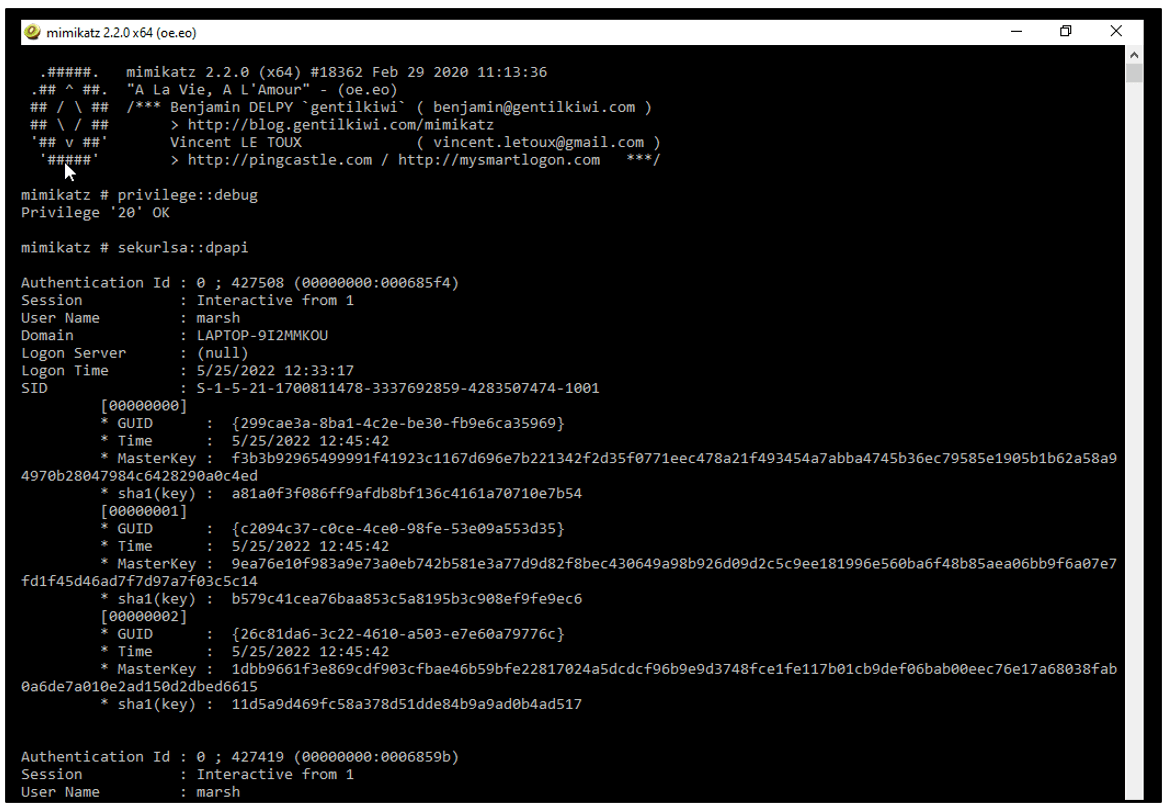
The GUID we need is for Marsha (SID S-1-5-21-1700811478-3337692859-4283507474-1001).
There are 3 GUIDs shown (Highlighted in green). We want the Masterkey associated to GUID c2094c37-c0ce-4ce0-98fe-53e09a553d35 which is highlighted in blue. Finding the right may involve trial and error.
We see the Master Key is: 9ea76e10f983a9e73a0eb742b581e3a77d9d82f8bec430649a98b926d09d2c5c9ee181996e560ba6f48b85aea06bb9f6a07e7fd1f45d46ad7f7d97a7f03c5c14
Step 3 – Unlocking the Masterkey
Leave the VM and copy the download.dat to the same folder as Mimikatz.
Run Mimikatz as Administrator and then run the following command:
# dpapi::blob /in:”download.dat” /unprotect / masterkey:9ea76e10f983a9e73a0eb742b581e3a77d9d82f8bec430649a98b926d09d2c5c9ee181996e560ba6f48b85aea06bb9f6a07e7fd1f45d46ad7f7d97a7f03c5c14
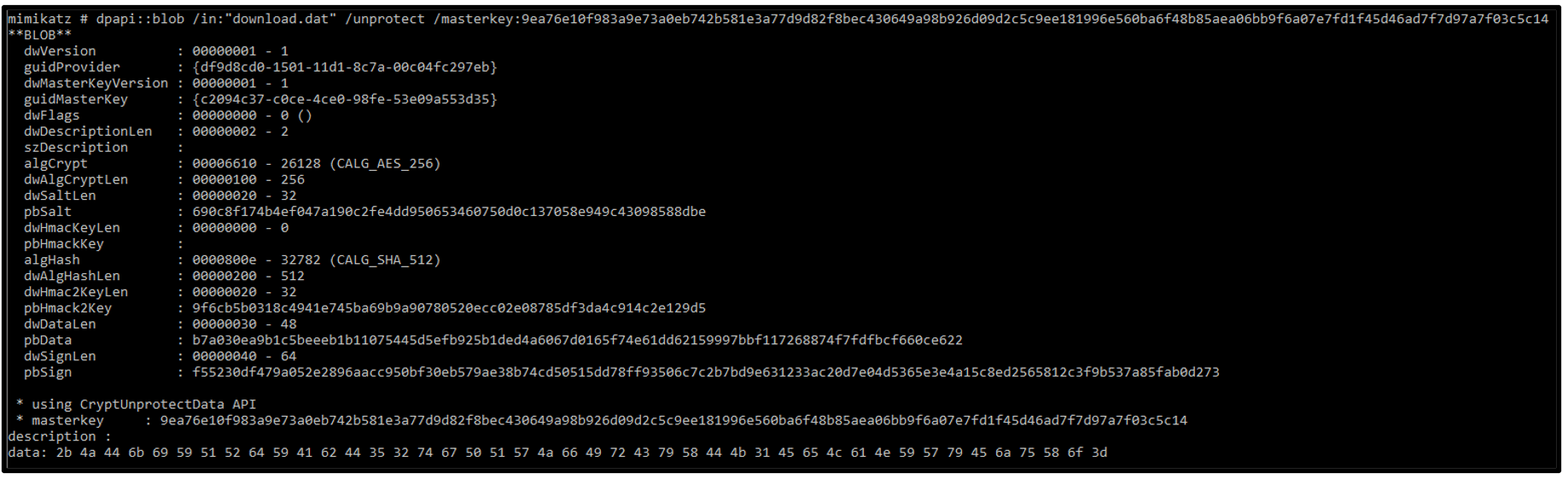
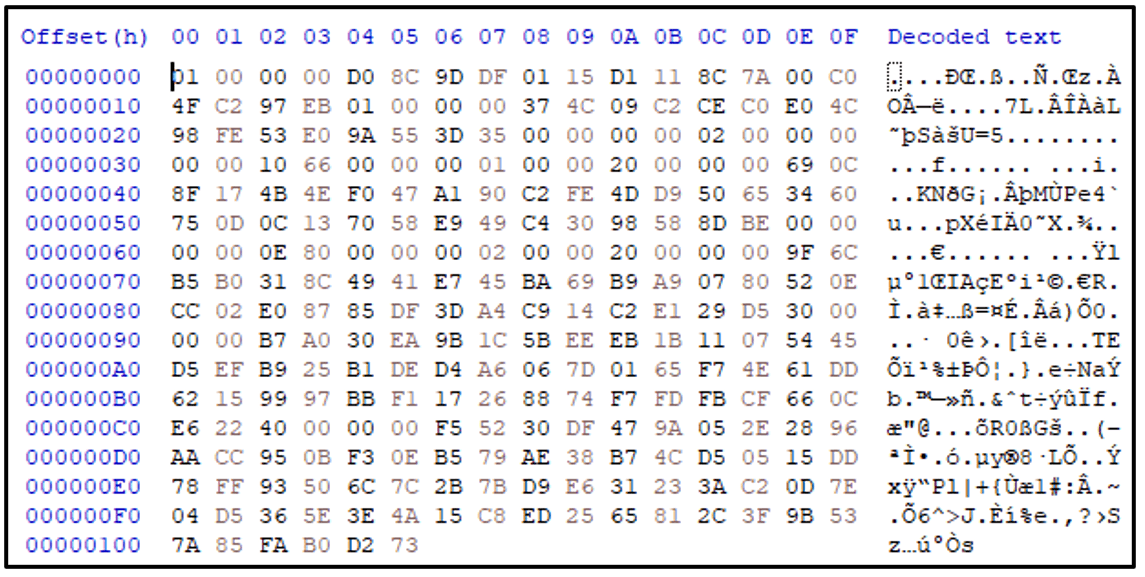
The result is the data:
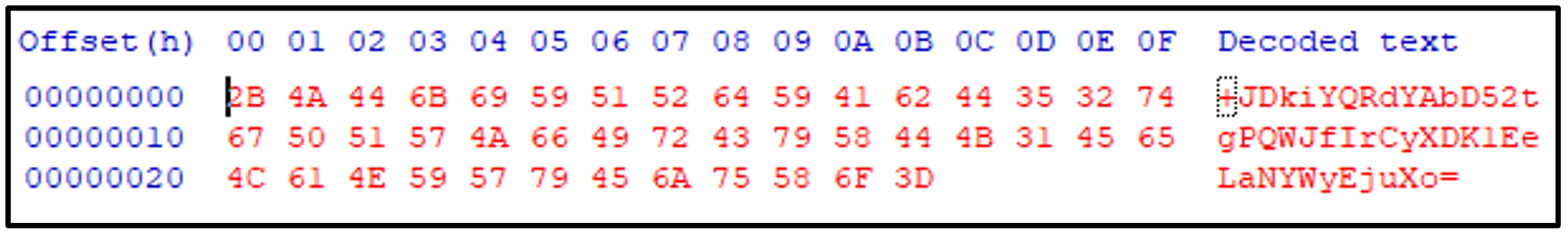
2b 4a 44 6b 69 59 51 52 64 59 41 62 44 35 32 74 67 50 51 57 4a 66 49 72 43 79 58 44 4b 31 45 65 4c 61 4e 59 57 79 45 6a 75 58 6f 3d
Which if viewed as Hex can be recognized as a Base64-encoded payload:
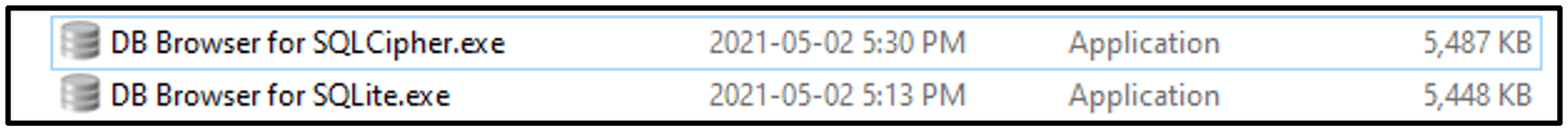
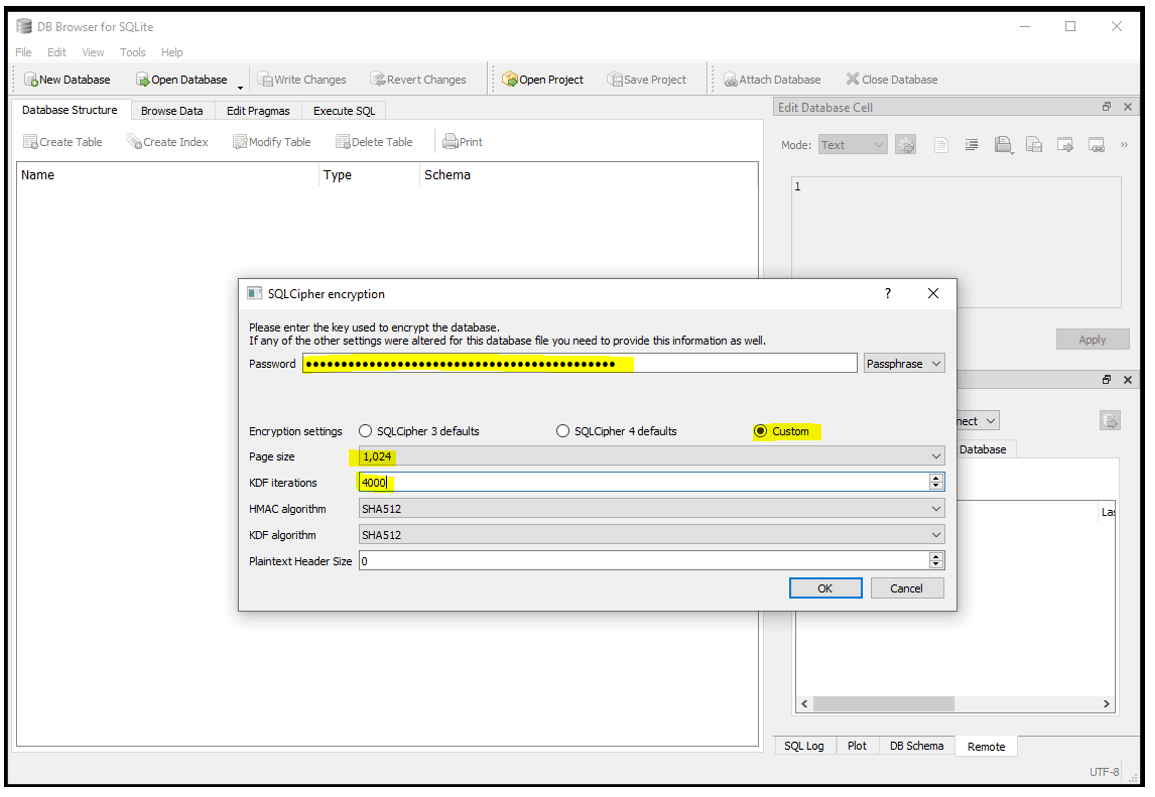
Step 4 – Opening the Database
Open the zoomus.enc.db using the “DB Browser for SQCipher.exe” (not regular DB Browser for SQLite)
You will be prompted for the decryption information which is defined within the MT_OHoffmann.pdf paper on page 58.
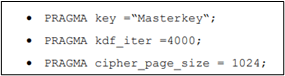
Enter the base64 string from above as the passphrase.
Change the page size to 1024 and the number of KDF iterations to 4000.
The database will be decrypted:
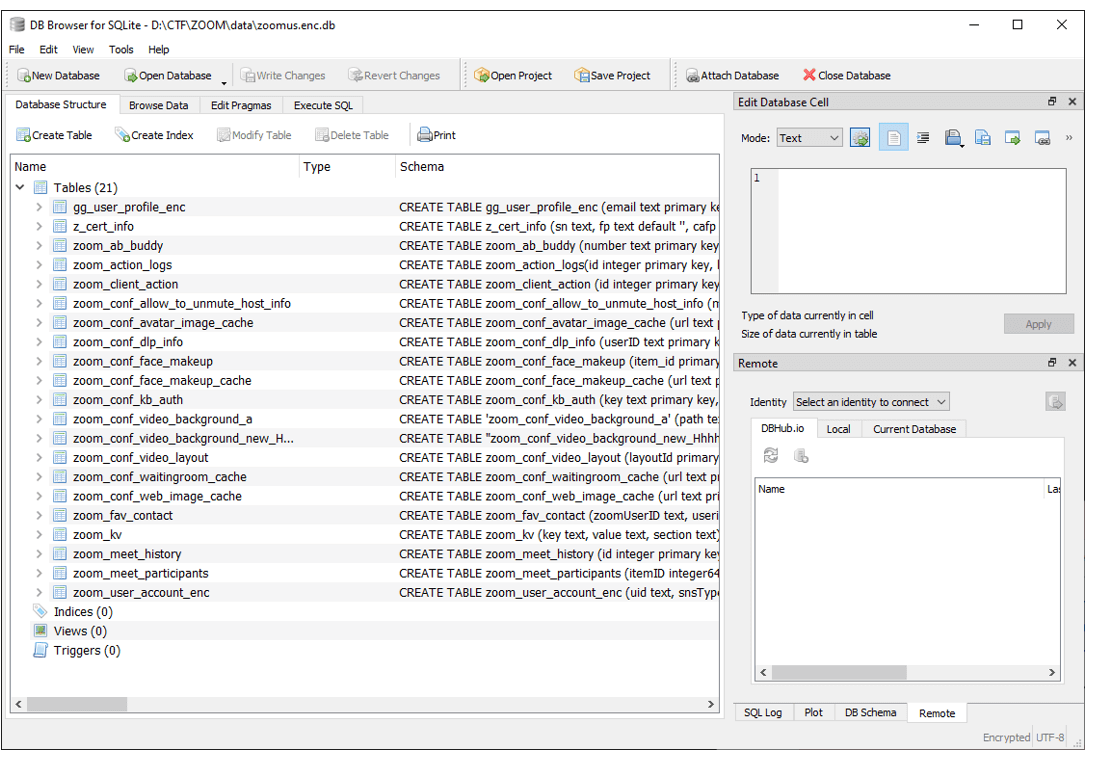
View the zoom_kv table and filter the key for “meeting” to find the com.zoom.client.saved.meetingid.enc and com.zoom.client.saved.meetingid.HhhhhN0kzycTgmq9cNya-K-tfAO-X-vn7CSTHCH7i-Y-.enc rows:
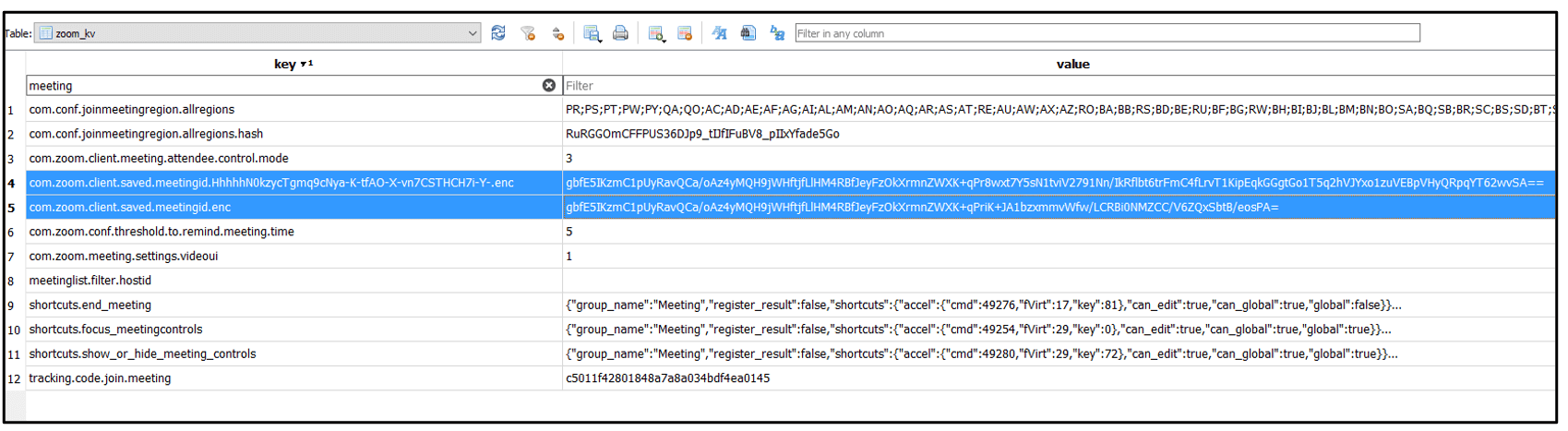
The values here are further encrypted, and as you may notice, are also base64 and have lots of prefix data that is identical (we’ve highlighted in bold)
|
gbfE5IKzmC1pUyRavQCa/oAz4yMQH9jWHftjfLlHM4RBfJeyFzOkXrmnZWXK+qPr8wxt7Y5sN1tviV2791Nn/IkRflbt6trFmC4fLrvT1KipEqkGGgtGo1T5q2hVJYxo1zuVEBpVHyQRpqYT62wvSA== |
|
gbfE5IKzmC1pUyRavQCa/oAz4yMQH9jWHftjfLlHM4RBfJeyFzOkXrmnZWXK+qPriK+JA1bzxmmvWfw/LCRBi0NMZCC/V6ZQxSbtB/eosPA= |
That’s because the second of these keys includes the same data as the first, plus more.
Simply using base64 to decode these values does not work.
Page 54 of the thesis explains that we need the user SID for the decryption of the data.
Which we can find from any forensic tool.
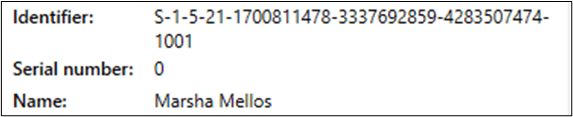
i.e. S-1-5-21-1700811478-3337692859-4283507474-1001
The encryption used on this data is AES256 in CBC Mode.
For AES Decryption we need the DATA, the KEY and the IV (Initialization Vector).
The Data is the string from the database: gbfE5IKzmC1pUyRavQCa/oAz4yMQH9jWHftjfLlHM4RBfJeyFzOkXrmnZWXK+qPr8wxt7Y5sN1tviV2791Nn/IkRflbt6trFmC4fLrvT1KipEqkGGgtGo1T5q2hVJYxo1zuVEBpVHyQRpqYT62wvSA==
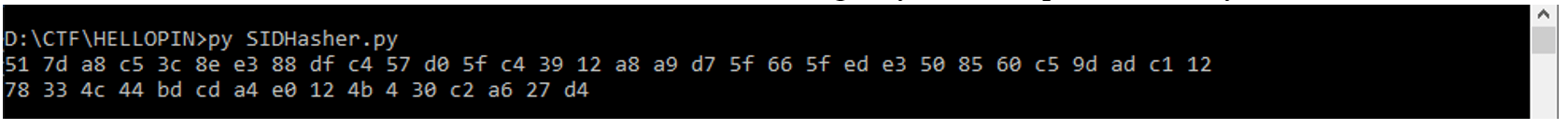
The Key is the result of running SHA256 on the users SID:
SHA256(S-1-5-21-1700811478-3337692859-4283507474-1001) = 517DA8C53C8EE388DFC457D05FC43912A8A9D75F665FEDE3508560C59DADC112
The IV is the first 16 bytes of the result of running SHA256 on the output of the last SHA256 command:
SHA256(517DA8C53C8EE388DFC457D05FC43912A8A9D75F665FEDE3508560C59DADC112) = 78334c44bdcda4e0124b0430c2a627d47da854f1fef8d819d1871f7764366eee
First 16 bytes = 78334c44bdcda4e0124b0430c2a627d4
Online tools can be utilized to perform the SHA256 hashes, or a very simple Python script can do this for you.
|
import Crypto.Hash.SHA256 import hashlib sid = b”S-1-5-21-1700811478-3337692859-4283507474-1001″ key = hashlib.sha256(sid).digest() iv = hashlib.sha256(key).digest()[:0x10] print(” “.join(format(n, ‘x’) for n in key)) print(” “.join(format(n, ‘x’) for n in iv)) |
The above code takes the SID and forms both hash functions to give you the output for the Key and IV.
We can then use CyberChef to decrypt the message:
Create a recipe that includes From Base64 and AES Decrypt.
Enter the data as it exists in the database and add the Key and IV bytes:
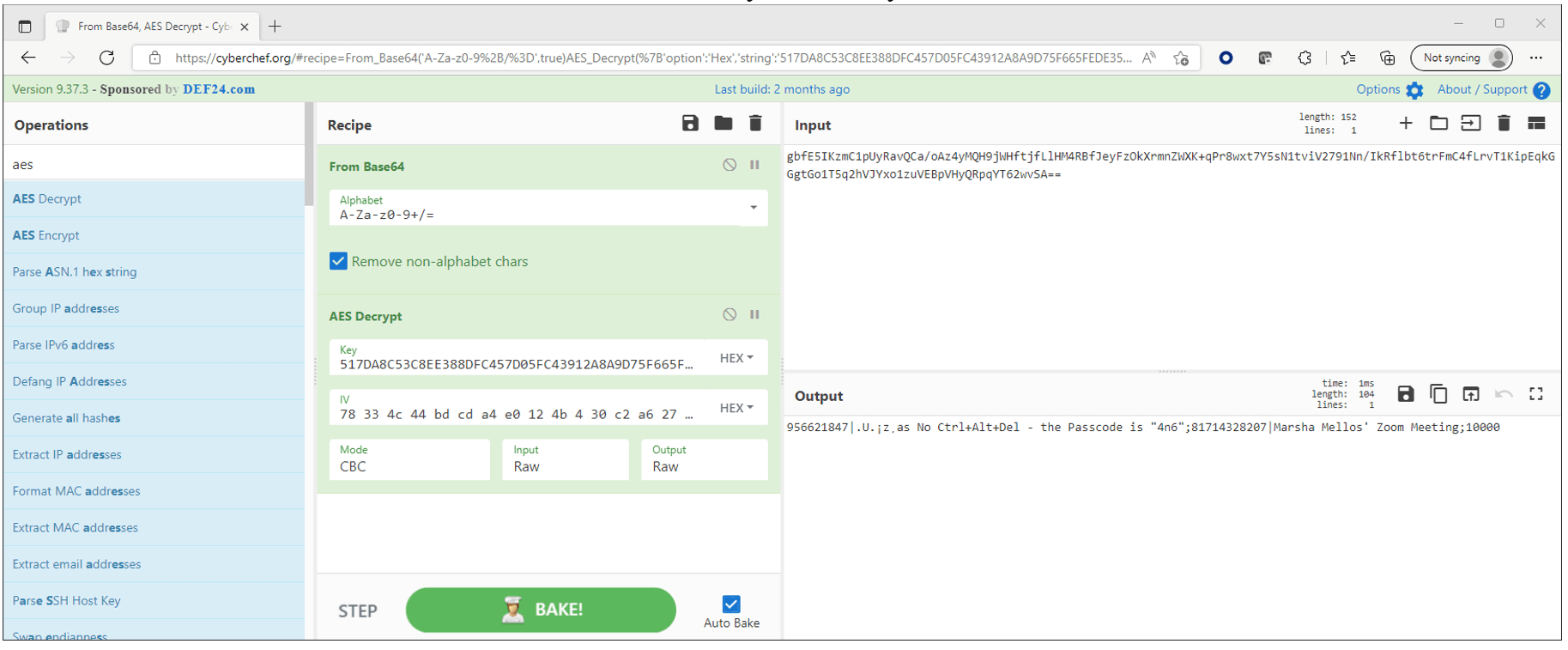
Note the Output is: 956621847|.U.¡z¸as No Ctrl+Alt+Del – the Passcode is “4n6”;81714328207|Marsha Mellos’ Zoom Meeting;10000 (Ctrl+Alt+Del is a great show you should attend. And it’s hosted by me!).
This shows two separate Zoom meetings
956621847|.U.¡z¸as No Ctrl+Alt+Del – the Passcode is “4n6”
81714328207|Marsha Mellos’ Zoom Meeting
And the one we are interested in is the Zoom Meeting ID of the second meeting
Therefore, the answer is 81714328207. If you answered this, congrats!!!
Question 12: Password (100 points) – What is the password for the URL containing a private IPv4 address in Microsoft Edge web browser’s saved logins? (Case Sensitive)
Flag: NPaacYaE
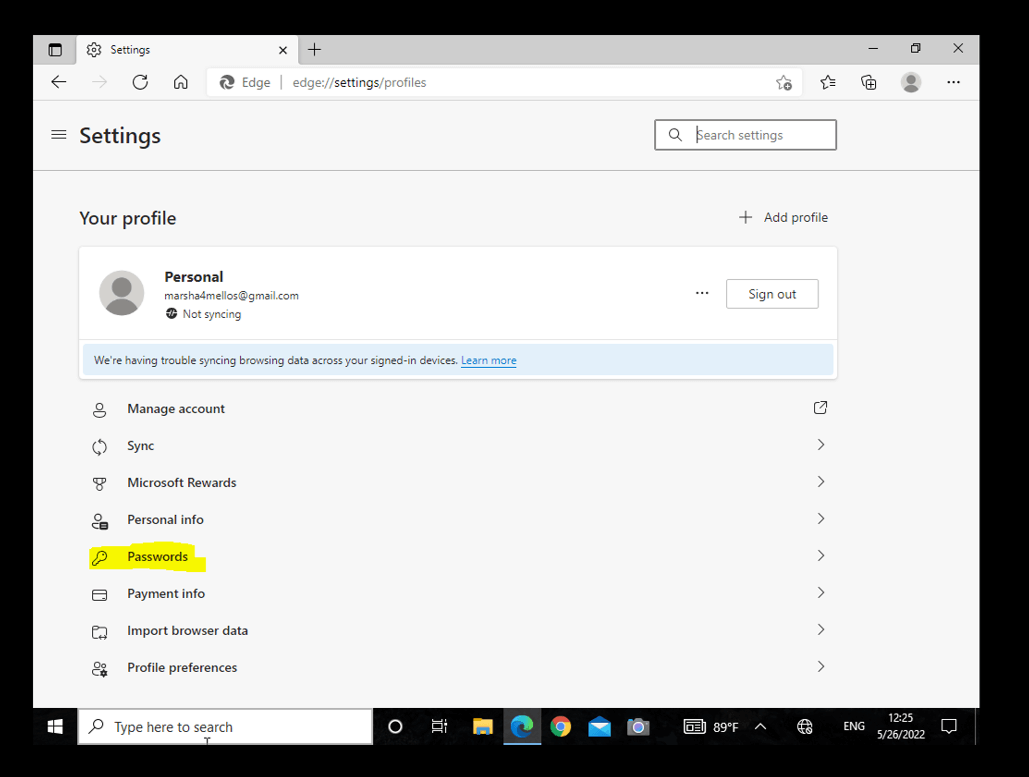
This requires you to use a tool such as FTK Imager to mount the e01 and then a tool such as VM Workstation or VirtualBox to launch the VM. There are many options available when setting up a VM and these are out of the scope of this answer. Once the VM is working, login to Marsha’s PC via VM using the Pin Code 134769 and start Edge. Go to Settings
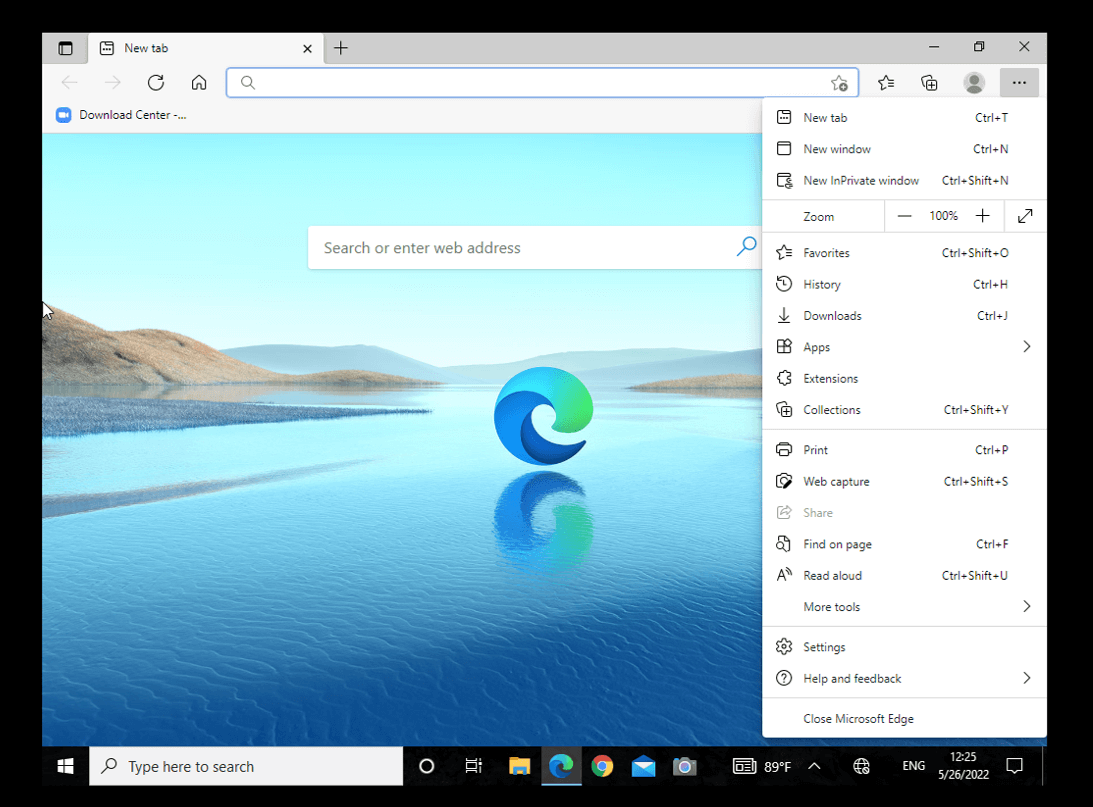
Next, expand Passwords.
You will see all of the saved passcodes, notable, 2 are Facebook and one is a private IP Address of 10.4.106.102.
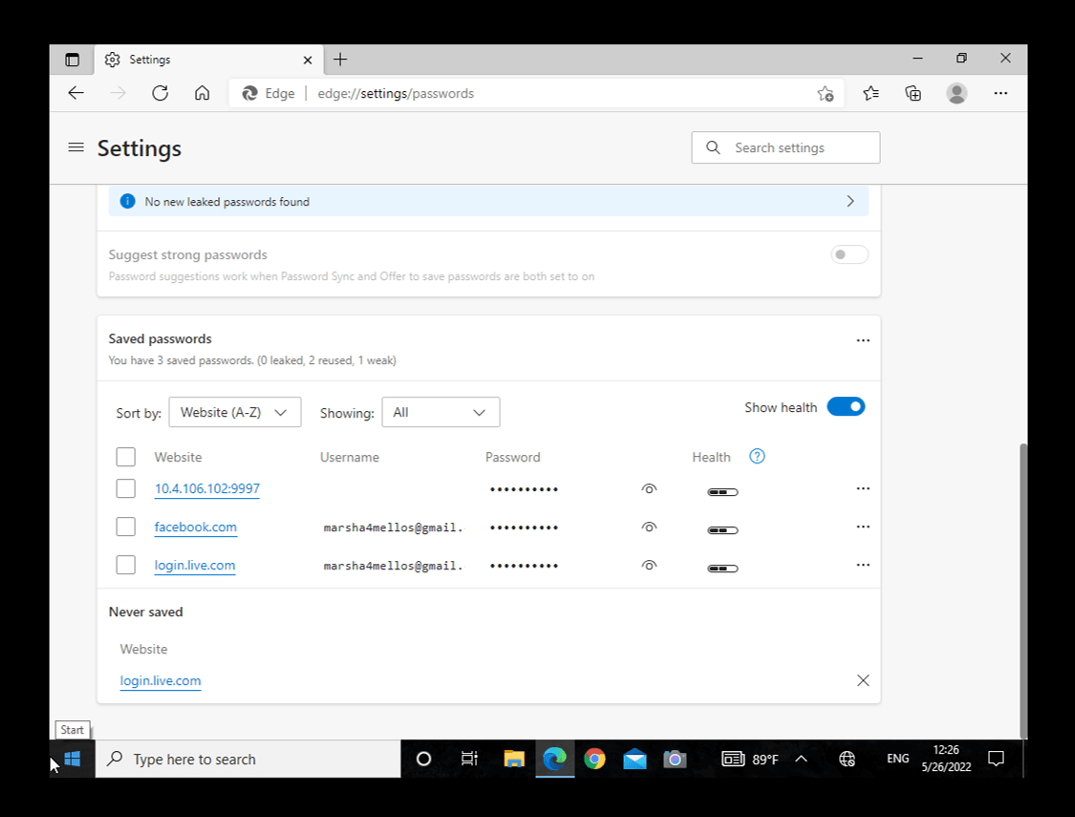
Click the small Eye icon to reveal the passcode.
We also want to give credit to others who took the time to share their walk-throughs. It’s important to read these blogs as the author may have derived the answer via a different file, artifacts, or using another tool. Thank you for taking the time to share your results!
https://www.stark4n6.com/2022/06/cellebrite-ctf-2022-marshas-pc.html
https://www.dfirblog.com/cellebrite-2022-ctf-writeup/
Read and follow the other walk-throughs at the following links:
- Part 2: https://cellebrite.com/en/part-2-ctf-2022-write-up-heisenbergs-android/
- Part 3: https://cellebrite.com/en/part-3-ctf-2022-write-up-marshas-ios-device/
- Part 4: https://cellebrite.com/en/part-4-ctf-2022-write-up-beths-ios-device/
