
Part 2: CTF 2022 Write Up – Heisenberg’s Android
We would like to say thank you to everyone who participated in the Capture the Flag event. Also, a special thanks to Sahil Dudani for the data creation and to Ian Whiffin for helping solve the questions. There were many late evenings and lots of hard work by many people involved. Ronen Engler was the fearless leader of this effort and, on his behalf, I want to say thank you for playing this game. This is Cellebrite’s way of giving back to the community and providing resources to keep learning!
We wanted to provide a bit of a walkthrough on how we came to the answers. There will be times in the blog that we mention, and reference, blogs written by various community members who provided their own write-up about the CTF and, interestingly enough, some paths to get to the answers aren’t the same way we got there, which is the beauty in forensics. The paths we take may differ, but the results are the same.
The backstory:
Beth Dutton was invited to the Vienna Inn in Vienna, VA on July 21st at 5:00 PM and was arrested while there. She was invited by Heisenberg. Police arrested her for grand theft. Upon questioning Beth, she revealed that her sister, Marsha Mellos introduced her to Heisenberg and that he was responsible for stealing cars and she and her sister were innocent. They are in the cattle business in Montana and got mixed up with the wrong guy. Marsha has both a PC and an iPhone. Beth had an iPhone and Heisenberg had an Android. The interest here is auto theft and selling. Cash transfers matter.
Heisenberg Android Questions:
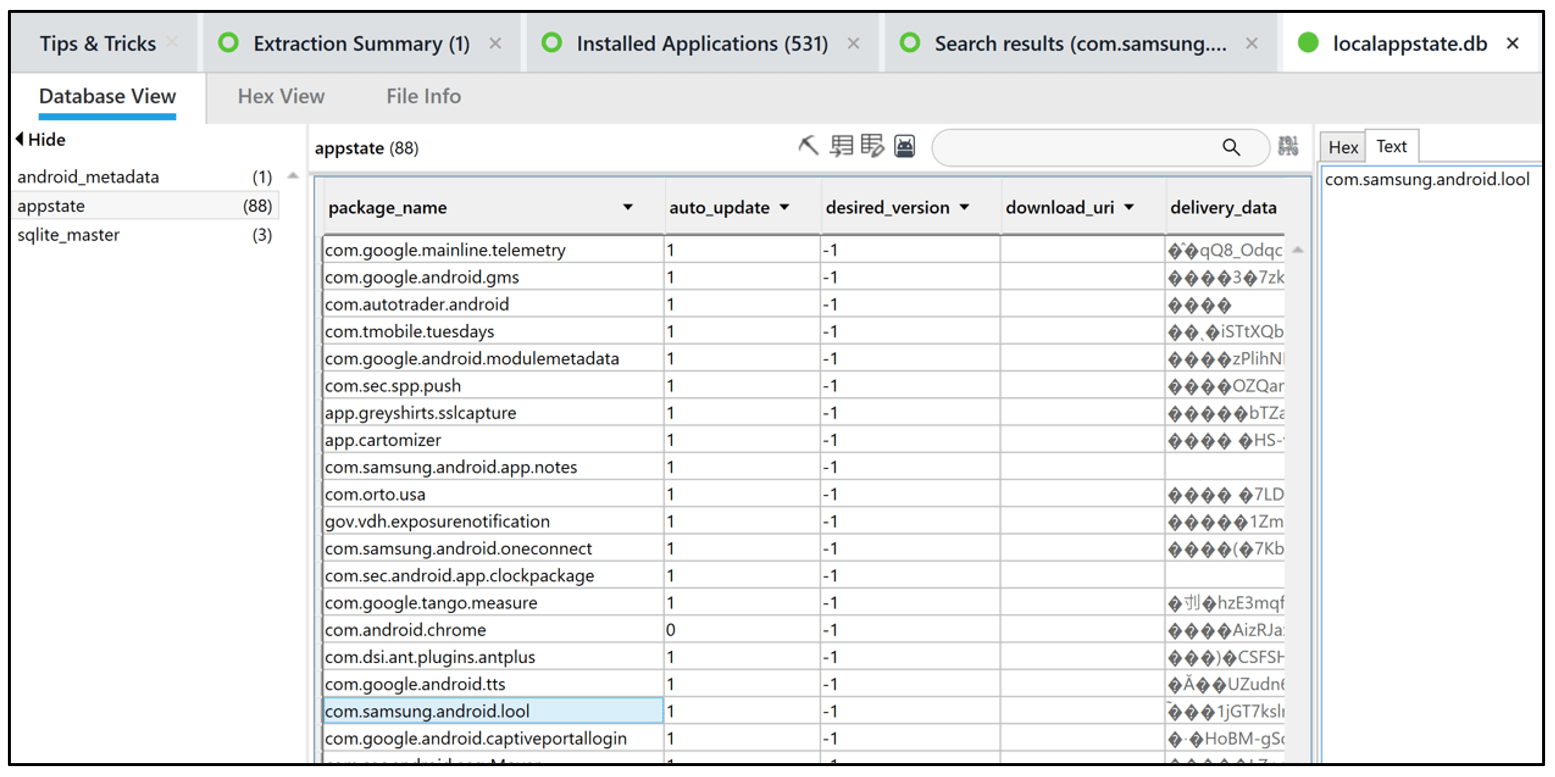
Question 13: Optimize (10 points) – What package was used by the Mobile App used by Heisenberg to scan/optimize his device? (Package name)
Hint 1: Samsung App
Hint 2: Care
Flag: com.samsung.android.lool
There are various ways to approach this question. Some went to Installed Apps and looked for anything that seemed to fit this description. Another clue was Device Care, which will lead you to the correct package. This is a great example of where a tool like ALEAPP may be of value to quickly answer the question. Below, we see the result in localappstate.db in Physcial Analyzer.
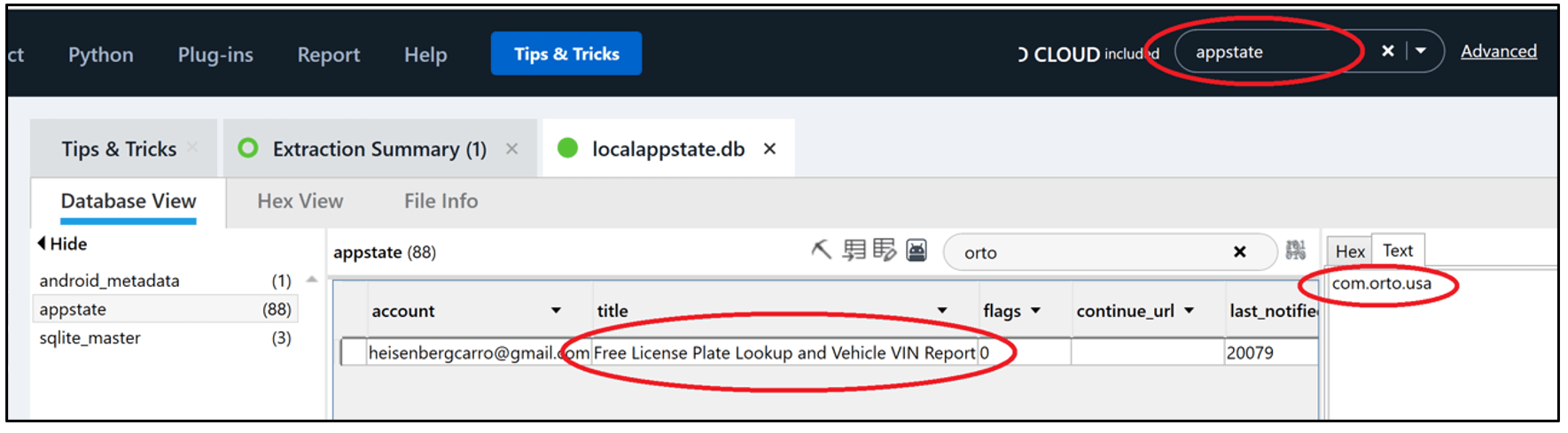
Question 14: Lookup (10 points) – What is the package name used by the Mobile App that Heisenberg used to look up license plates/VIN of target vehicles?
Hint 1: Appstate
Flag: com.orto.usa
Again, starting with Installed applications and looking at the type of application may help. One should stand out and that is com.orto.usa. Another way is to filter or search for “license” which will lead you to the application. Localappstate.db will also provide this answer, as will ALEAPP.
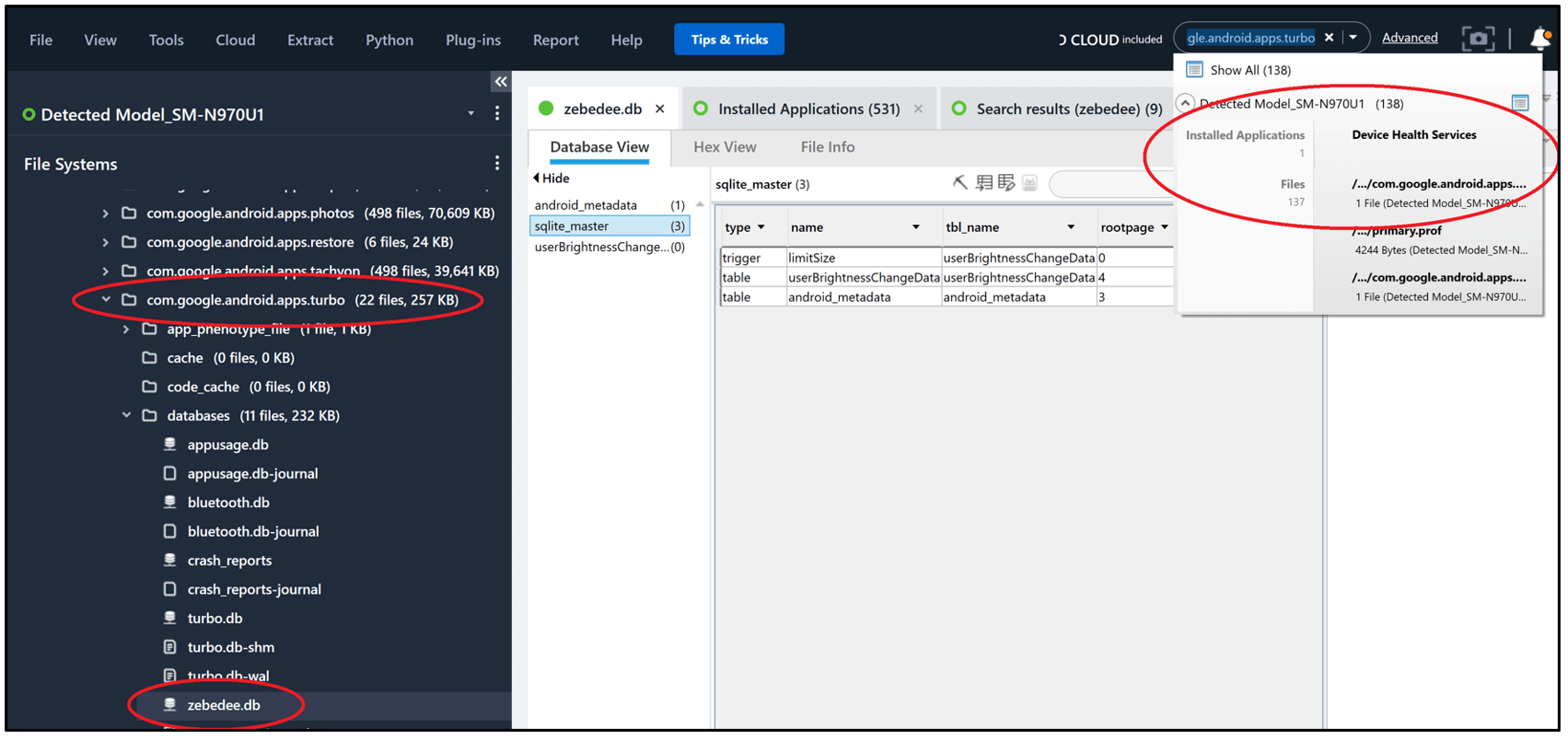
Question 15: ZBDDB (10 points) – What app does “zebedee.db” correspond to?
Hint 1: Turbo
Hint 2: Device Brightness
Flag: DEVICE HEALTH SERVICES or device health
In Physical Analyzer, you can simply keyword search for “zebedee.db” or you can go to Databases in Analyzed Data and filter on Zebedee. Both options will lead you to com.google.android.apps.turbo. Kevin Pagano released an informative blog on the importance of this file, and we recommend you read it! (https://www.stark4n6.com/2020/12/charging-battery-with-turbo-db.html) Once you have the package name, return to the Installed Applications and you will find the app is associated with device health.
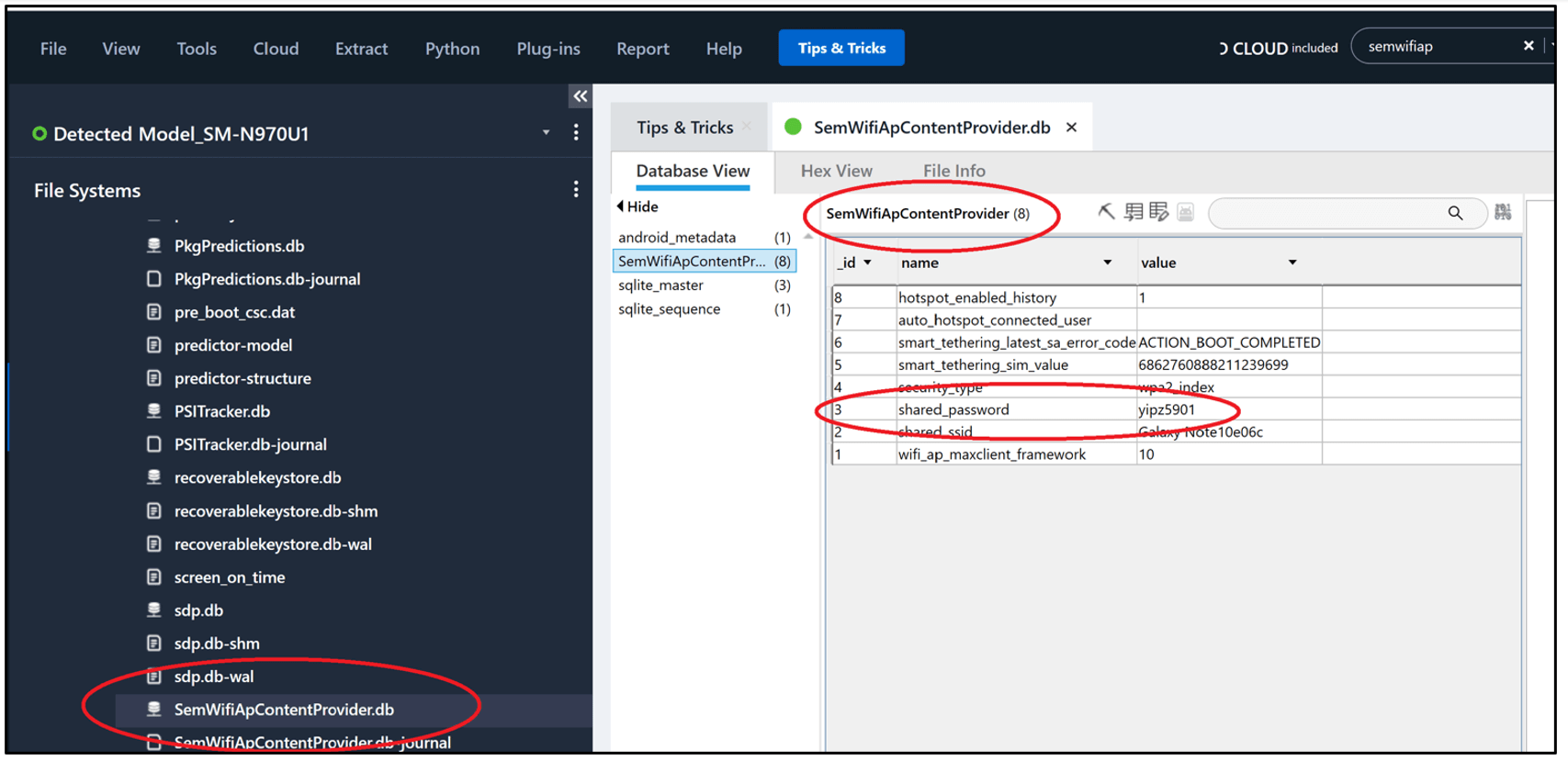
Question 16: Key (10 points) – What is the password for the mobile data hotspot on Heisenberg’s device that was shared with Beth? (Case Sensitive)
Flag: yipz5901
Keyword searching is helpful for this question. If you search for “wifi” you will find SemWifiApContentProvider.db. The table SemWifiApContentProvider has a field with “shared_password” which is shown below.
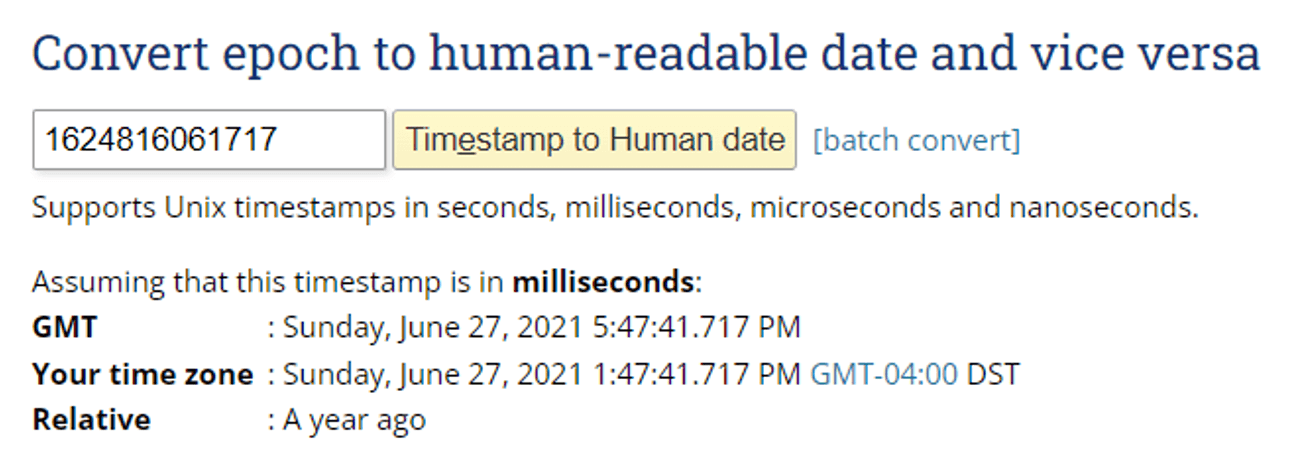
Question 17: MAC (10 points) – What is the Bluetooth MAC address, date, and time for the last connection to Bose Sound Touch/CE2D10 (MAC YYYY-MM-DD HH:MM:SS) (). Example: aa:bb:cc:dd:ee:ff 2020-04-28 18:29:33
Hint 1: Bluetooth
Flag: 2C:6B:7D:1D:21:A7 2021-06-27 17:47:41
Bluetooth Timestamps are tricky. You need to make sure you understand the meaning of them. As always, I want to dig deeper and validate so I searched in Hex for “CE2D10” and ultimately found QcDb.db where a record shows the timestamp. This timestamp is in UNIX Milliseconds.
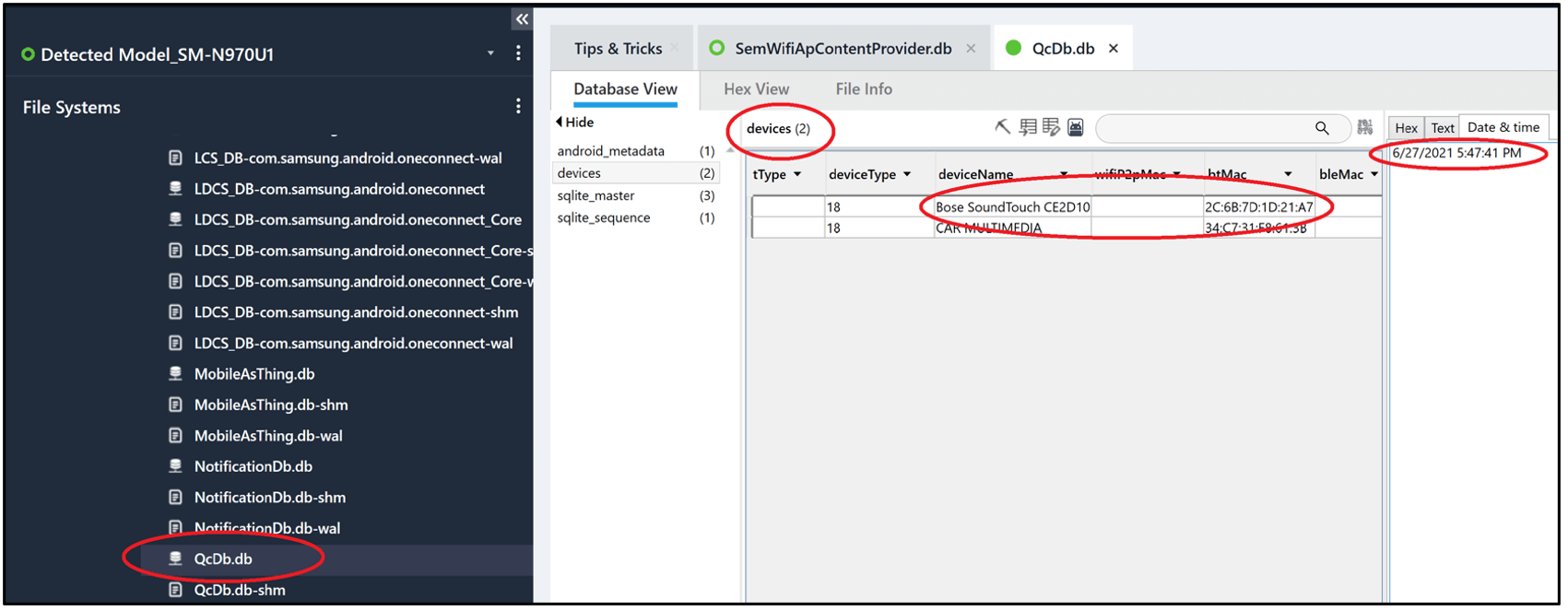
I used an online converter to convert this, as well as Physical Analyzer, as shown above.
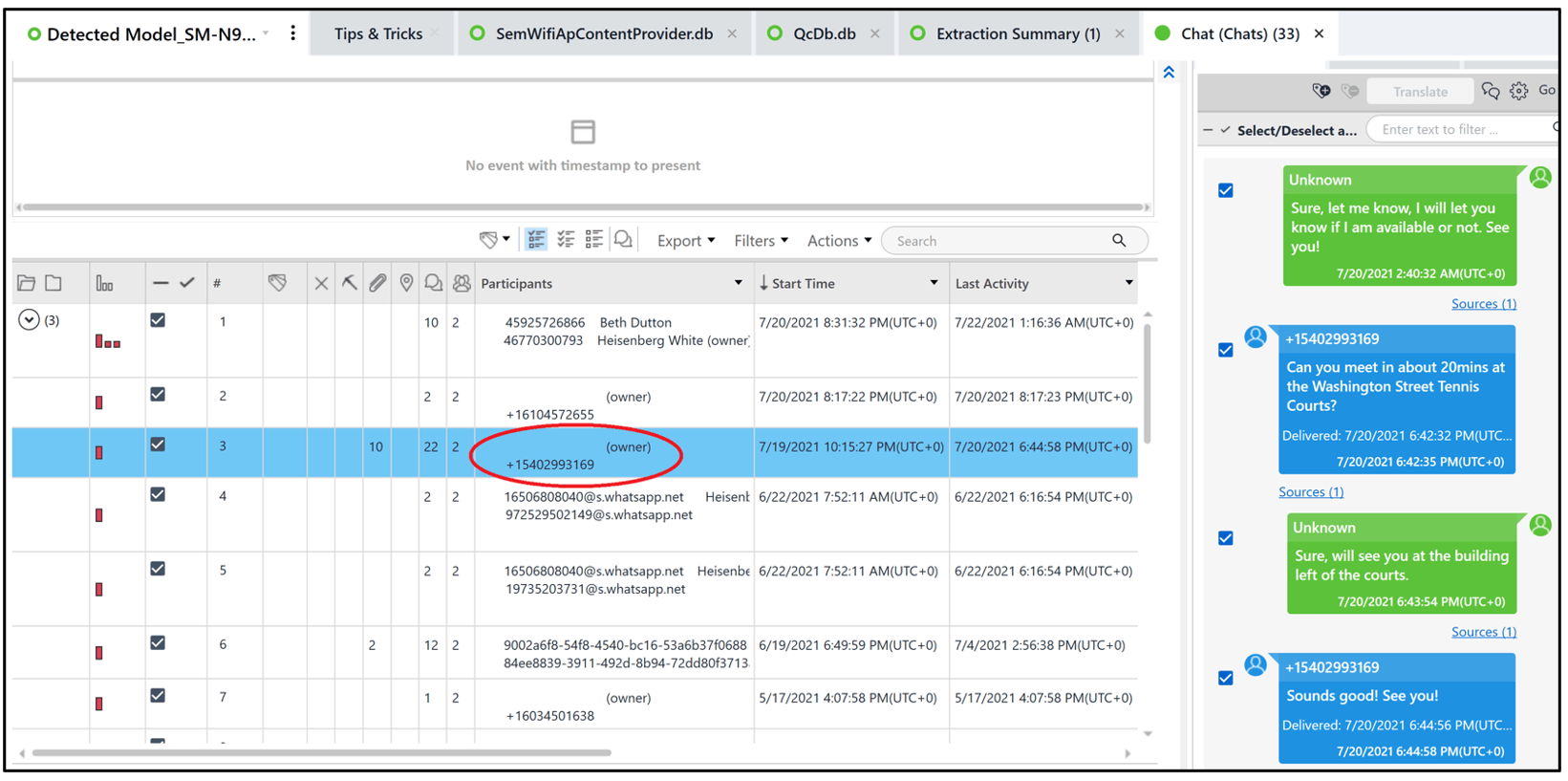
Question 18: Number (10 points) – What is the phone number of the undercover cop who approached Heisenberg? (Format: +1-212-555-1234)
Hint 1: Hyundai
Hint 2: Call
Flag: +1-540-299-3169
There are many ways to answer this question. In Physical Analyzer, I went to messages and searched for Hyundai and found the phone number. Others may search for Hyundai. Some may take the phone number from another question and associate it back with this one. Again, there are many ways to get to the correct answer.
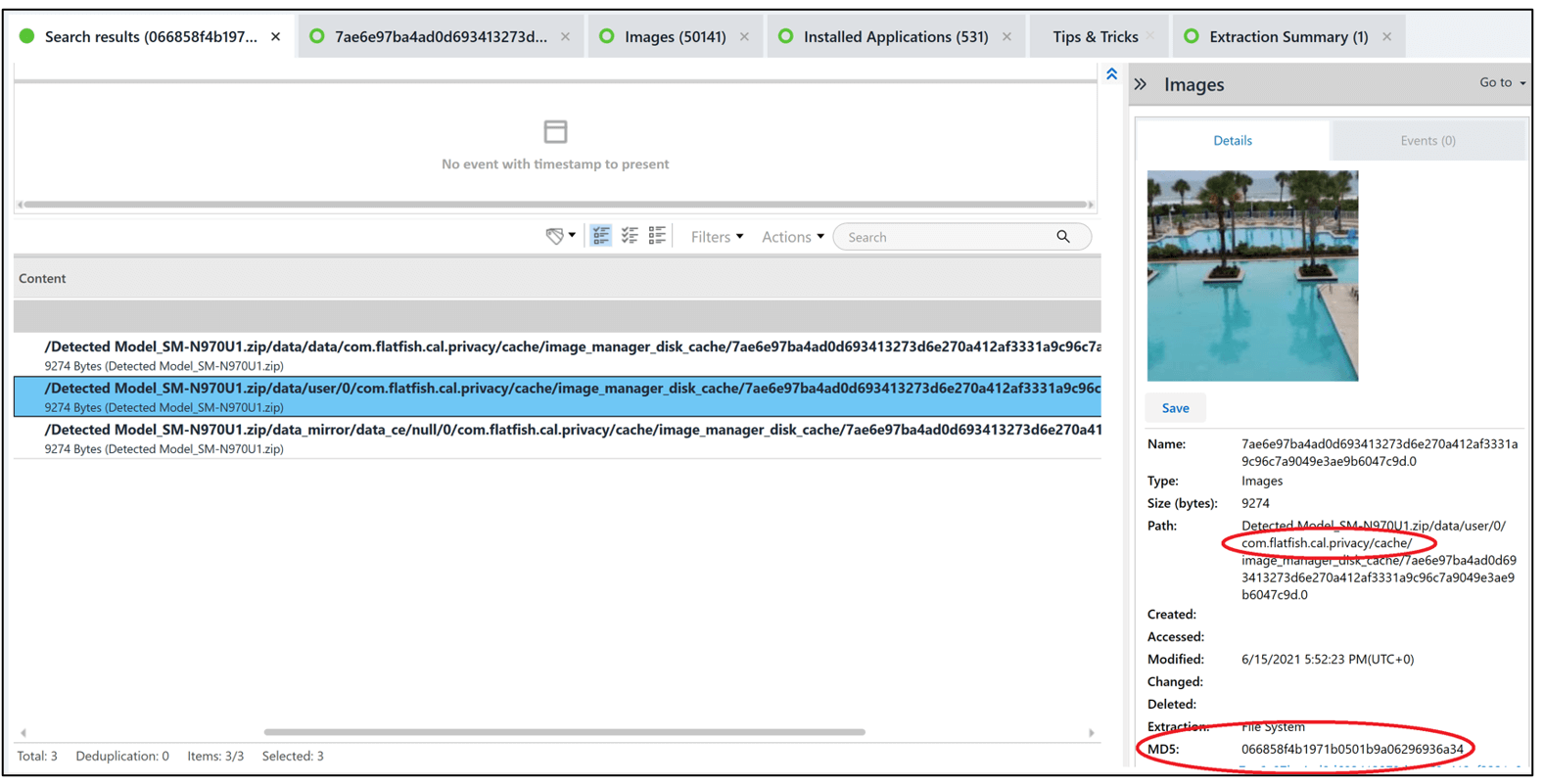
Question 24: App (20 points) – Was the image with the MD5 hash “066858f4b1971b0501b9a06296936a34” hidden by Heisenberg? If yes, what is the name of the package of the app used to hide the image, otherwise answer No.(Example: yes+com.apple.wallet)
Hint 1: Swimming Pool and Pine Trees
Hint 2: flatfish
Flag: yes com.flatfish.cal.privacy or yes+com.flatfish.cal.privacy
One approach is to search for the hash value in Physical Analyzer. Another is to go into Analyzed Data>Images and filter on hash value. Either way, you will be led to the package name (com.flatfish.cal.privacy ) within the file path.
 Question 25: Tag (20 points) – What is the name, username and account number corresponding to the media id “2623237359273252101”. Was Heisenberg following this account? (Answer Format: Name_Username_AccountNumber_Yes/No) (No Spaces)
Question 25: Tag (20 points) – What is the name, username and account number corresponding to the media id “2623237359273252101”. Was Heisenberg following this account? (Answer Format: Name_Username_AccountNumber_Yes/No) (No Spaces)
Hint 1: Instagram
Hint 2: Marsha
Flag: MARSHAMELLOS_MARSHA4MELLOS_44072330861_YES
A Hex search in Physical Analyzer is helpful for this question. We searched for “2623237359273252101” and the results are shown below. Hex searches can be tedious, so make sure you make the search as specific as possible.
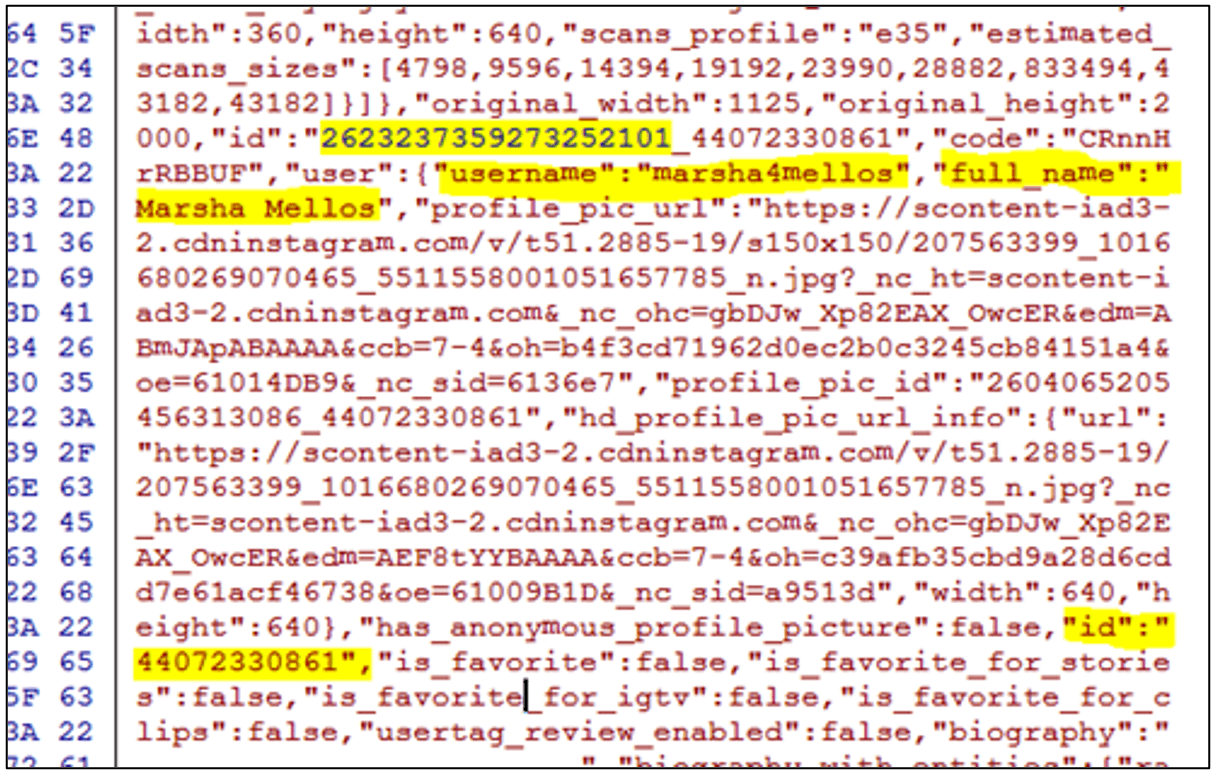
Another file that stores this information is user_reel_medias_room_db_46770300793. The user_reel_medias has a data column that can be converted to easily read the JSON contents.
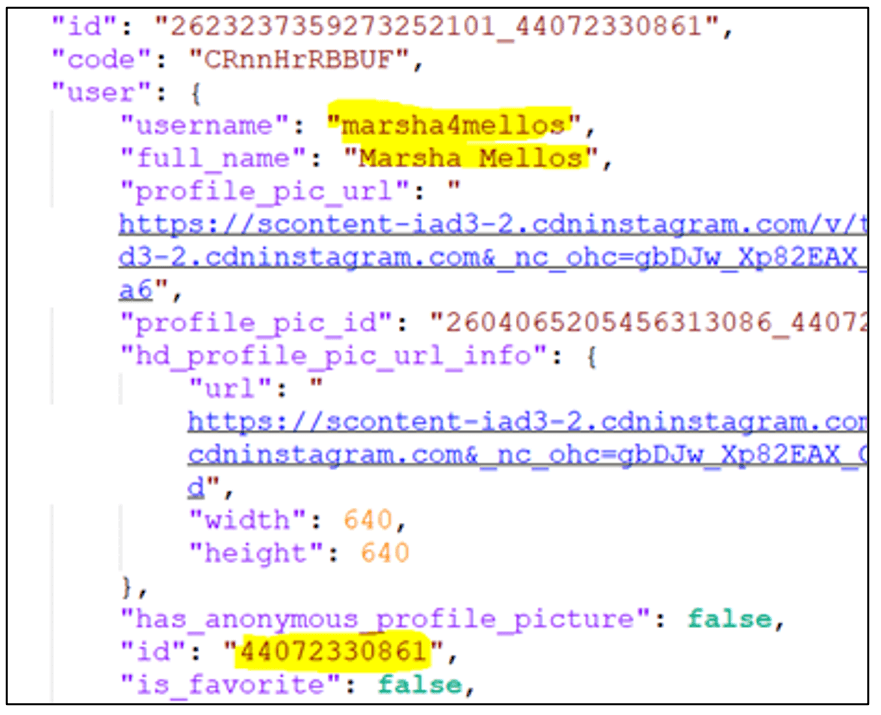
A logical keyword search in Physical Analyzer may have also led you to the correct answer.
Question 26: Stamp (20 points) – What is the Date and Time for the last use of Instagram on Heisenberg’s device? (YYYY-MM-DD HH:MM:SS) (24-hr format) example: 2019-03-22 23:45:12
Flag: 2021-07-22 19:06:37
In Analyzed Data in Physical Analyzer, go to the databases and then filter on Application for Instagram. Here, you will see an association to time_in_app_46770300793.db which will store the answer.
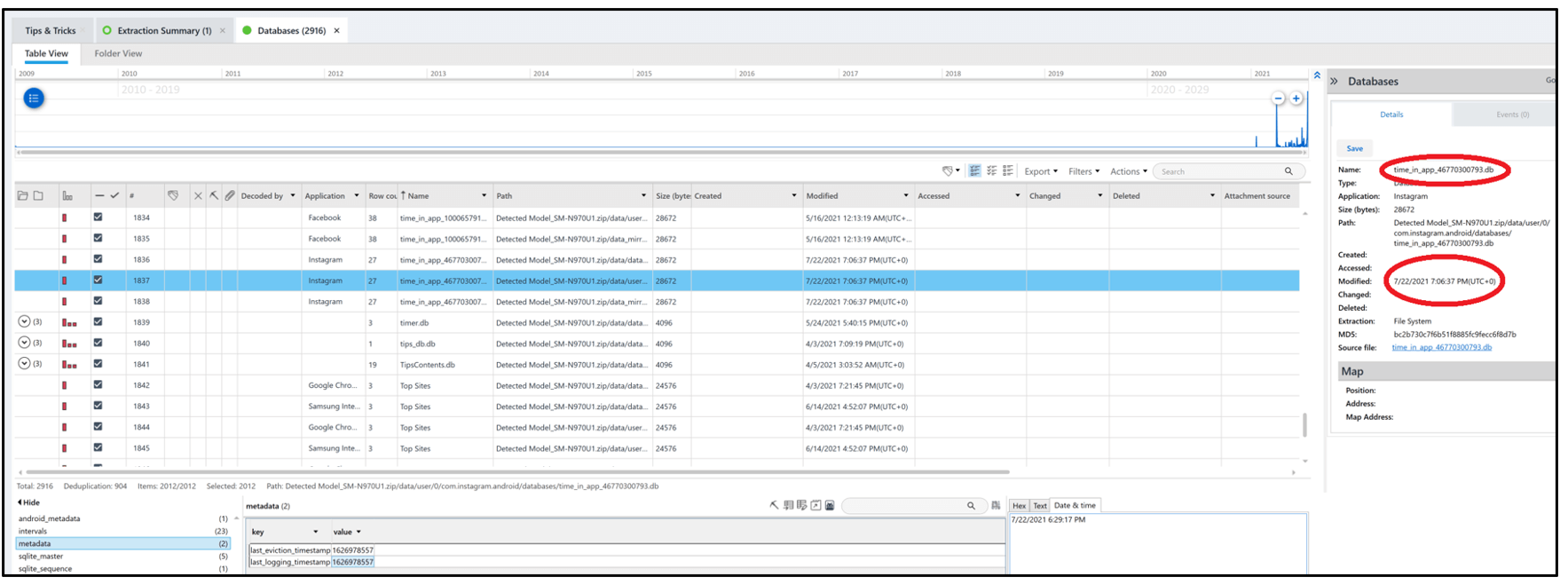
For manual validation, the table “intervals” and the column end_walltime contain the answer.
Question 27: Card (20 points) – Find the first six and the last four digits of a burner card that was used by Heisenberg for gas. (FirstSix_LastFour)
Hint 1: Gas Deals
Hint 2: GetUpside
Flag: 414720_0834
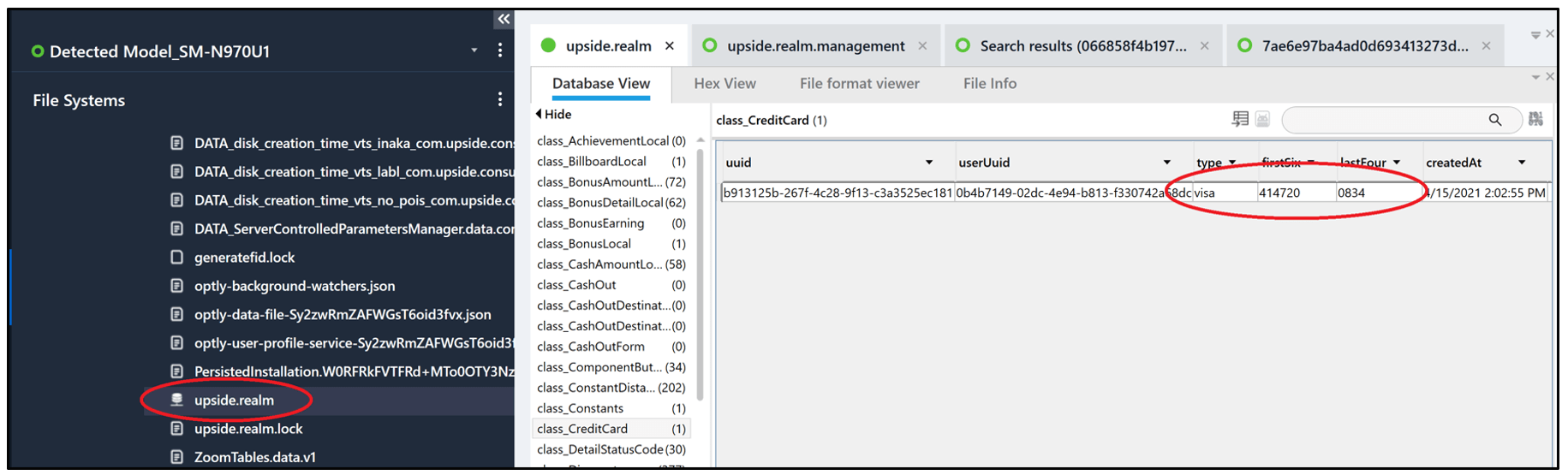
In Physical Analyzer, a great starting point is installed apps. From here, search for anything that is associated with purchasing or “gas.” This will lead you to the database upside.realm. Inside class_CreditCard was a visa card with details first 6 = 414720 last 4 = 0834.
Question 28: Android Standard (20 points) – Heisenberg intended to have a meeting with the person he was intensely communicating with. Establish the name of the street in which the meeting was about to take place and the exact time of the chat in which the requesting party confirmed the meeting. format: [street name] [time HH:MM:SS UTC] example: Main St. 19:27:21
Hint 1: Most interactive parties
Hint 2: Topics (meetings)
Flag: washington street 18:44:58 or washington st. 18:44:58 or washington 18:44:58
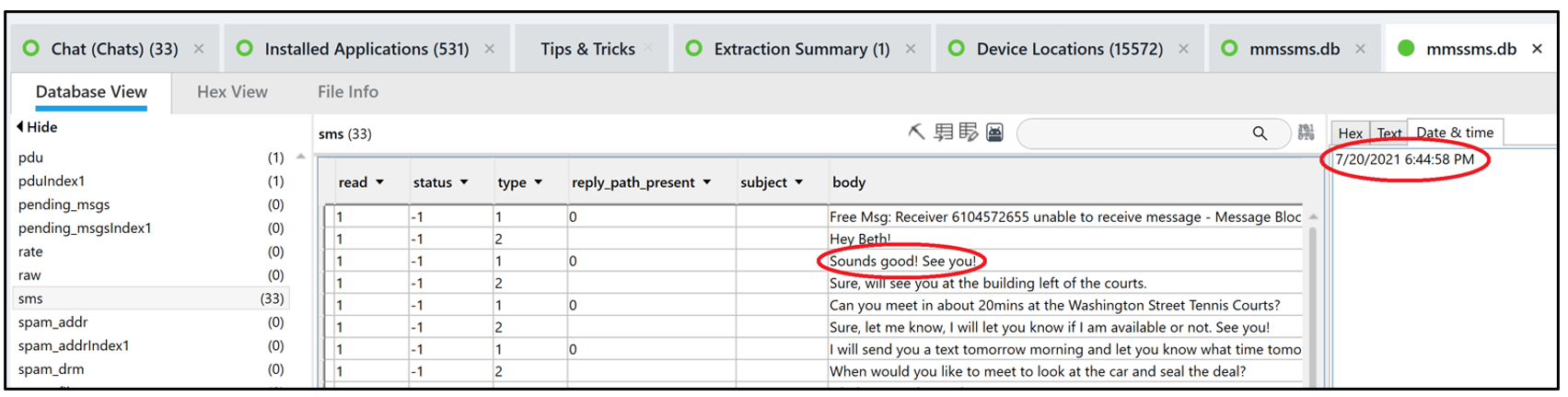
The best starting point for this one is to examine the messages on the device. Below, we can see Physical Analyzer and how the mmssms.db renders the chats. On the far right, we see the number, timestamp, and location.
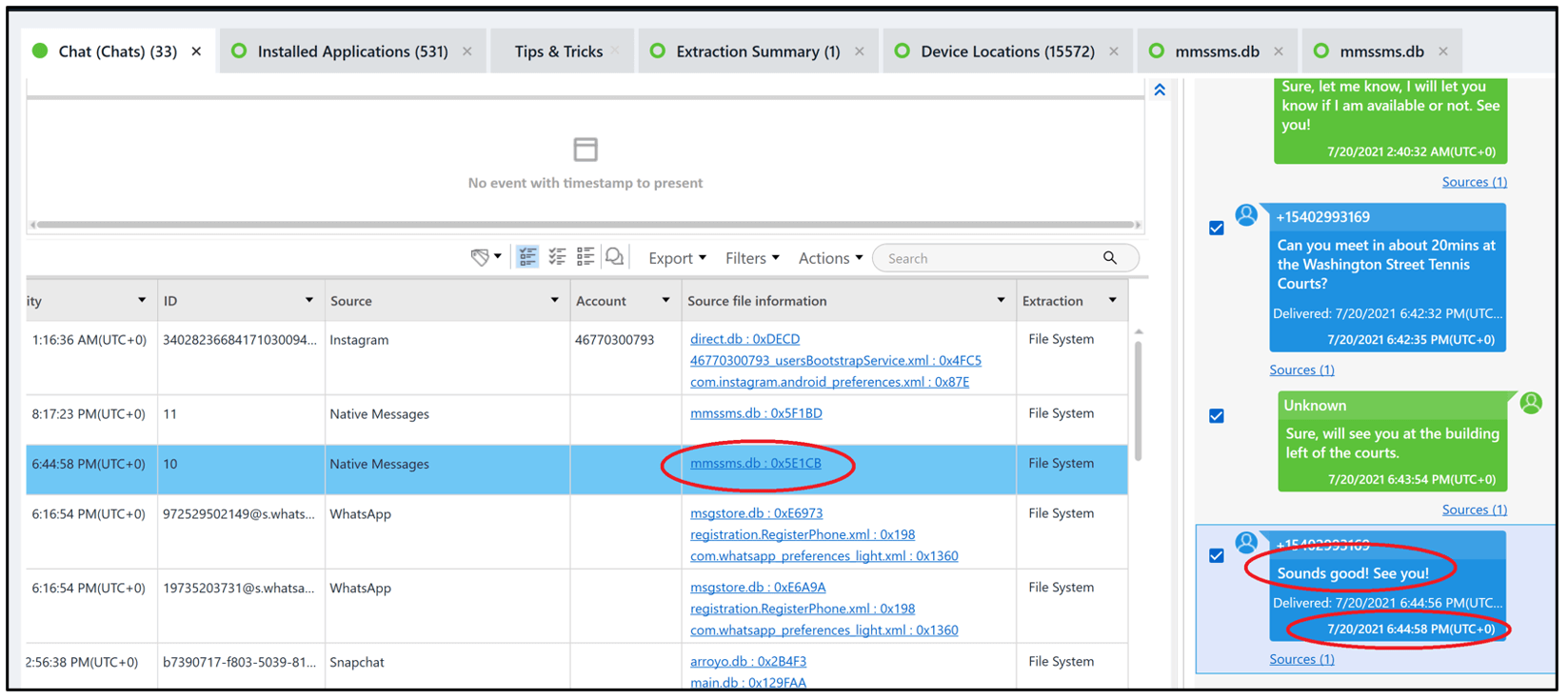
Another option is to go directly to the mmssms.db and search for “Meet”. This method will also provide the answer and the Date&Time tab in the SQLite Viewer in PA can be used to decode the timestamp.
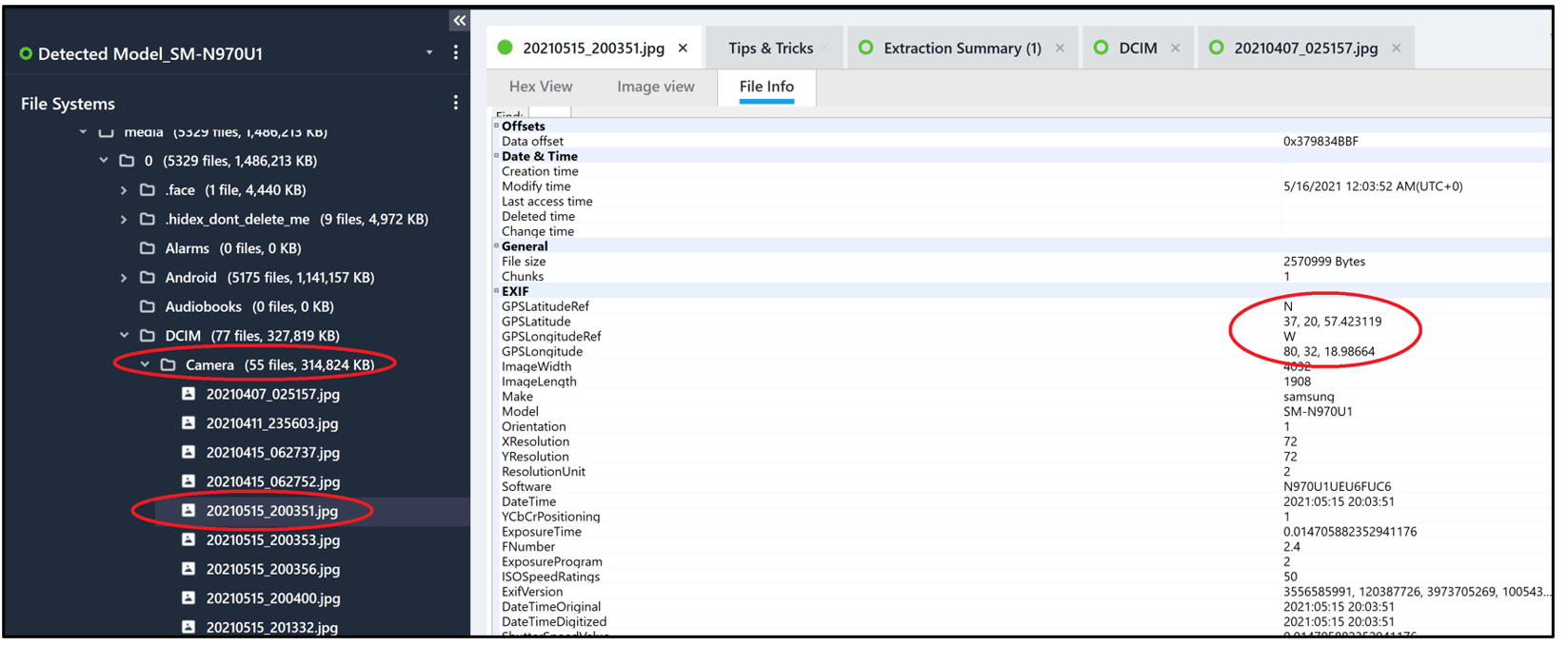
Question 29: location (20 points) – This meeting was a setup in which a police agent arrested Heisenberg. Find evidence that was generated during the estimated time of the meeting in which you can witness (see and hear) Heisenberg’s arrest. What is the location in which this evidence was created? Note: There are only two instances of similar evidence that have geographical locations. (format: Lat,Long example: 33.333,-77.7777)
Flag: 37.2249,-80.4159
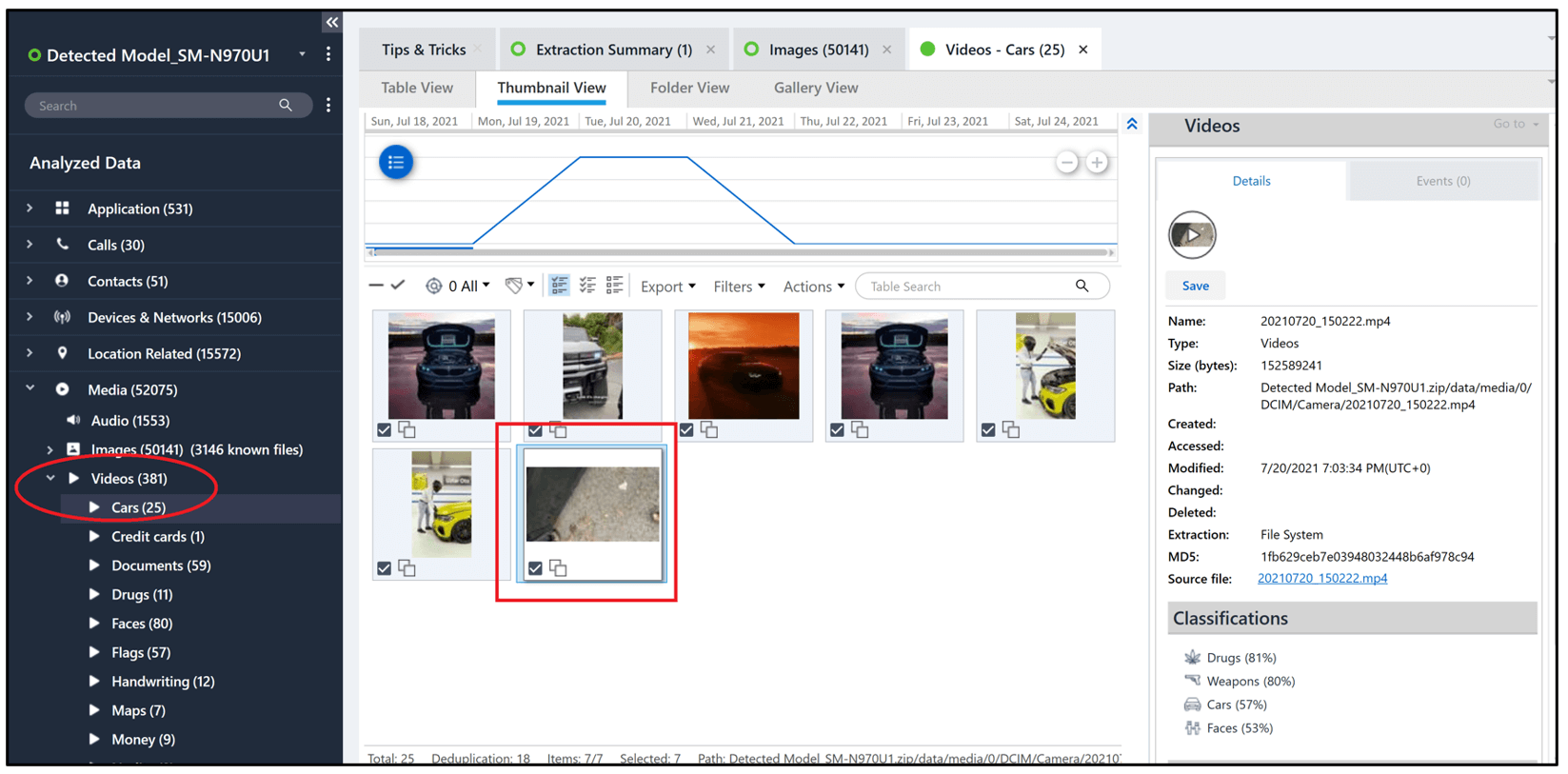
Read this question closely. It says “see and hear” which is likely to be a video. We also know the date of the meeting. A quick way to approach this question is to filter on videos with coordinates or by the timestamp. We find the answer quickly this way when we examine 20210720_150222.mp4.
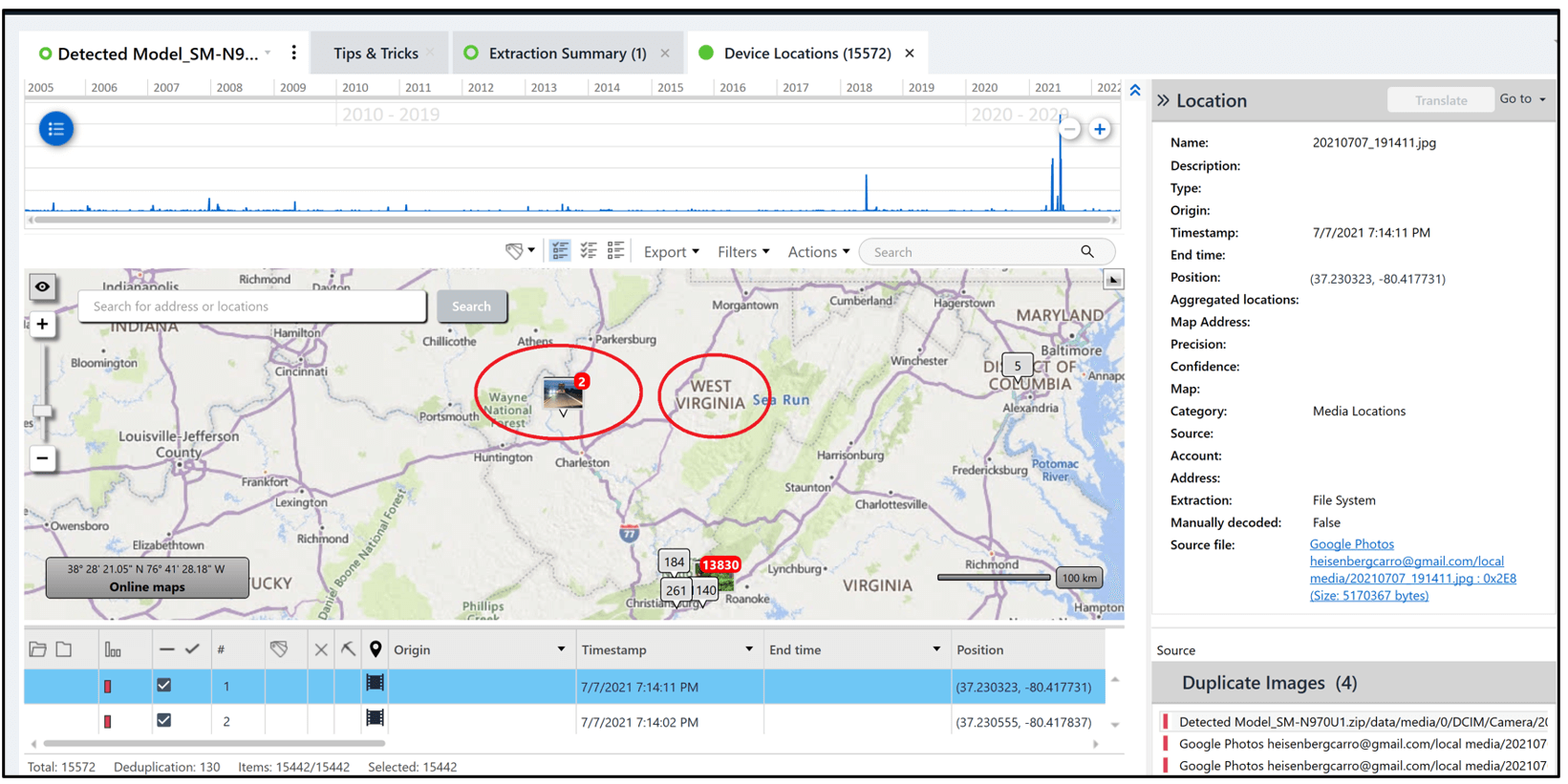
Question 21: WV (10 points) – Based on retrieved data from the device, the phone operated in West Virginia. True/False?
Flag: True
A quick triage will allow you to quickly answer this. We looked at Location data and saw photos associated with West Virginia.
Question 22: Camera (10 points) – How many native images on the device contain location data?
Flag: 55 or 57
One way to answer this is to sort by images in Physical Analyzer and then filter by Metadata and Images with Locations, which will show 57 results. If you go to Locations and then Native, you get 55 results. We accepted both responses. The two images missing from Locations are related to the SMS message. Again, always validate!
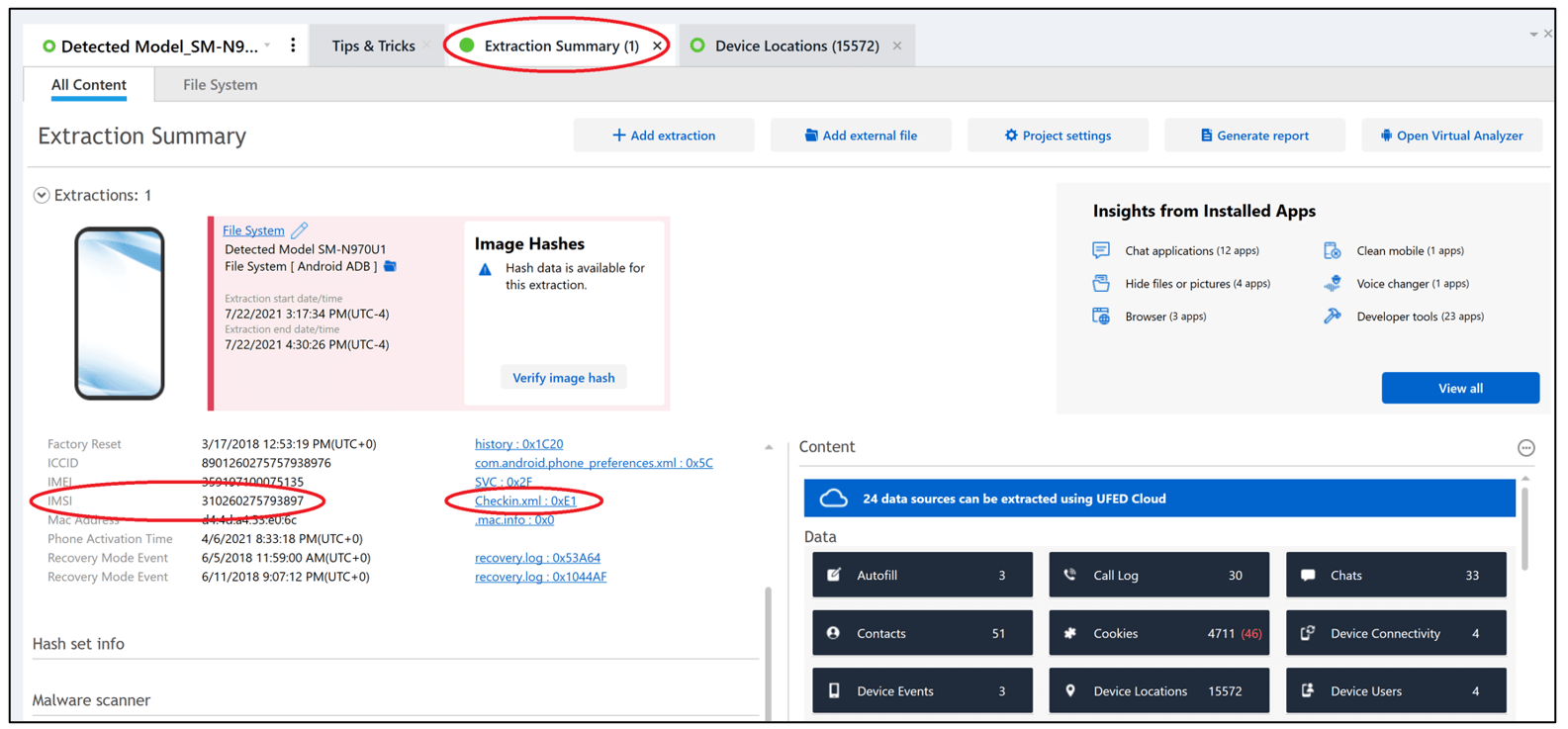
Question 23: Device info (10 points) – What is the IMSI of the device?
Hint 1: Device Info
Flag: 310260275793897
Within Physical Analyzer, this answer is found in Device Info.
We also want to give credit to others who took the time to share their walk-throughs. It’s important to read these blogs as the author may have derived the answer via a different file, artifacts, or using another tool. Thank you for taking the time to share your results!
Finally, thank you Alexis Brignoni, and those who contribute to ALEAPP!
https://www.stark4n6.com/2022/06/cellebrite-ctf-2022-heisenbergs-android.html
https://www.dfirblog.com/cellebrite-2022-ctf-writeup/
Read and follow the other walk-throughs at the following links:
- Part 1: https://cellebrite.com/en/part-1-ctf-2022-write-up-marshas-pc/
- Part 3: https://cellebrite.com/en/part-3-ctf-2022-write-up-marshas-ios-device/
- Part 4: https://cellebrite.com/en/part-4-ctf-2022-write-up-beths-ios-device/
