Physical Analyzer Cloud
Lawfully Access Cloud-Based Evidence to Accelerate Investigations
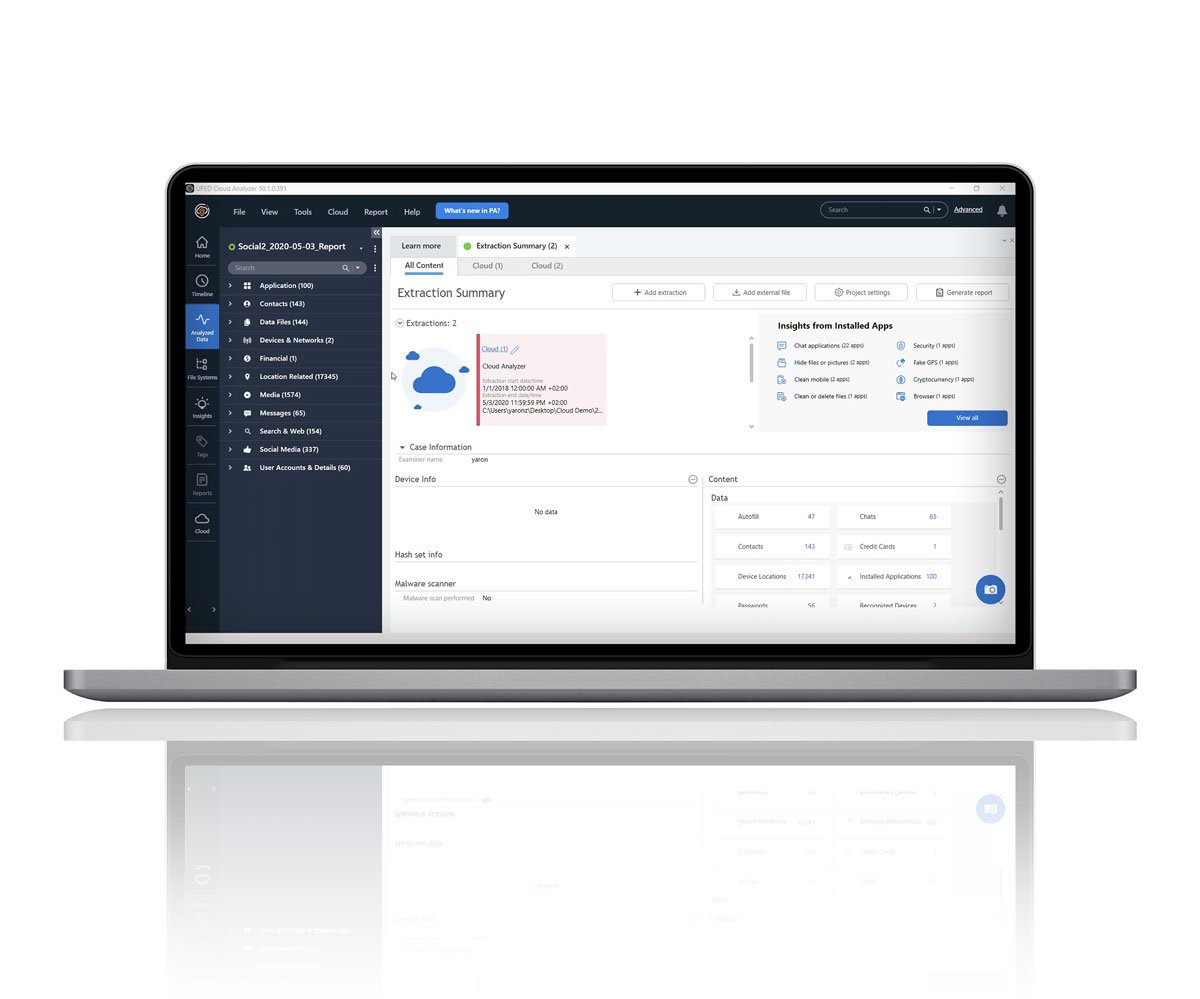
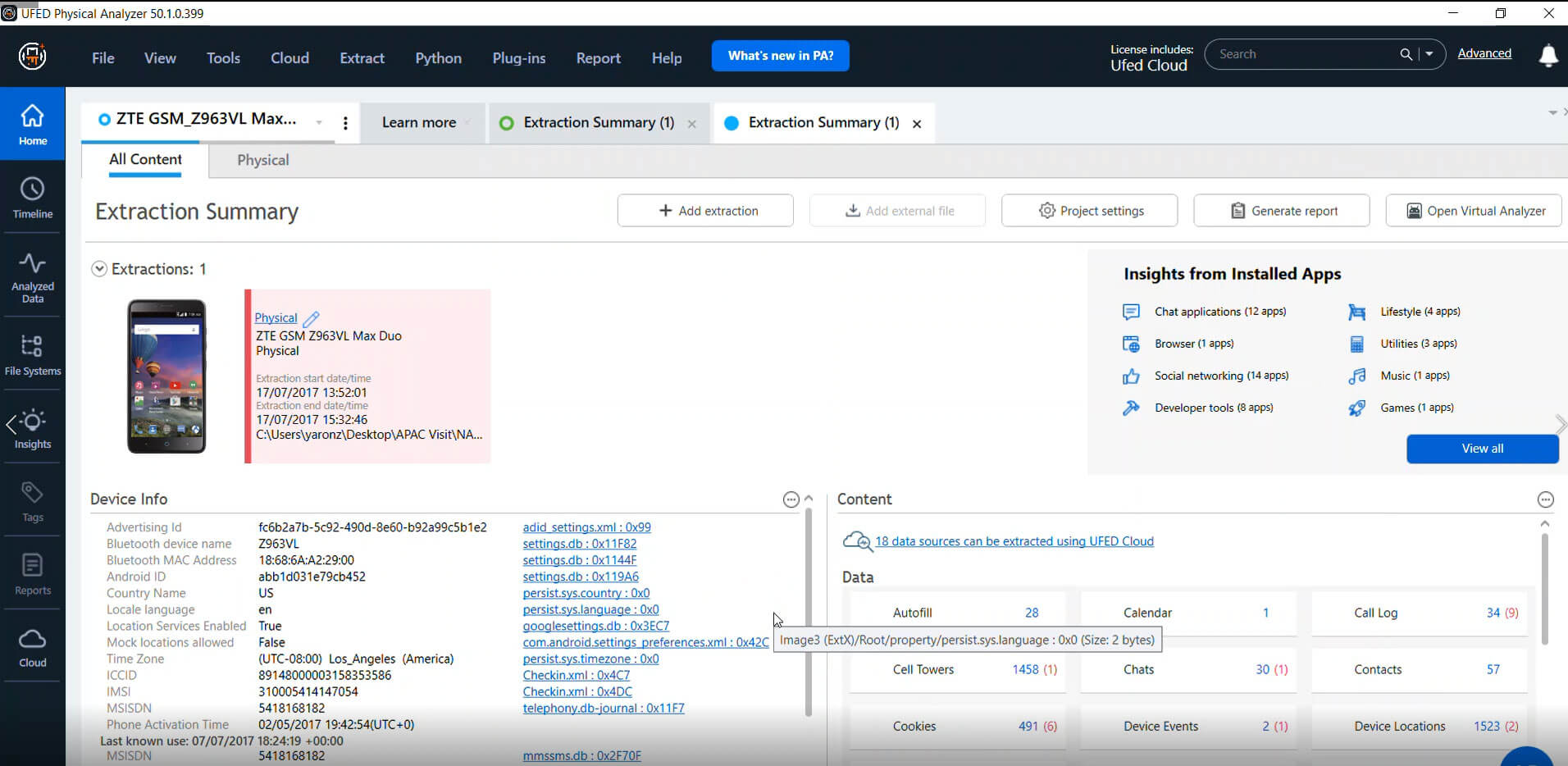
Collect, preserve and analyze public and private-domain, social-media data, instant messaging, file storage, web pages, and other cloud-based content.
Don’t Just Rely on Digital Device Data
Get quick, lawful access to cloud-based data that can help advance investigations.
- Gather Social and Cloud-Based Data Easily
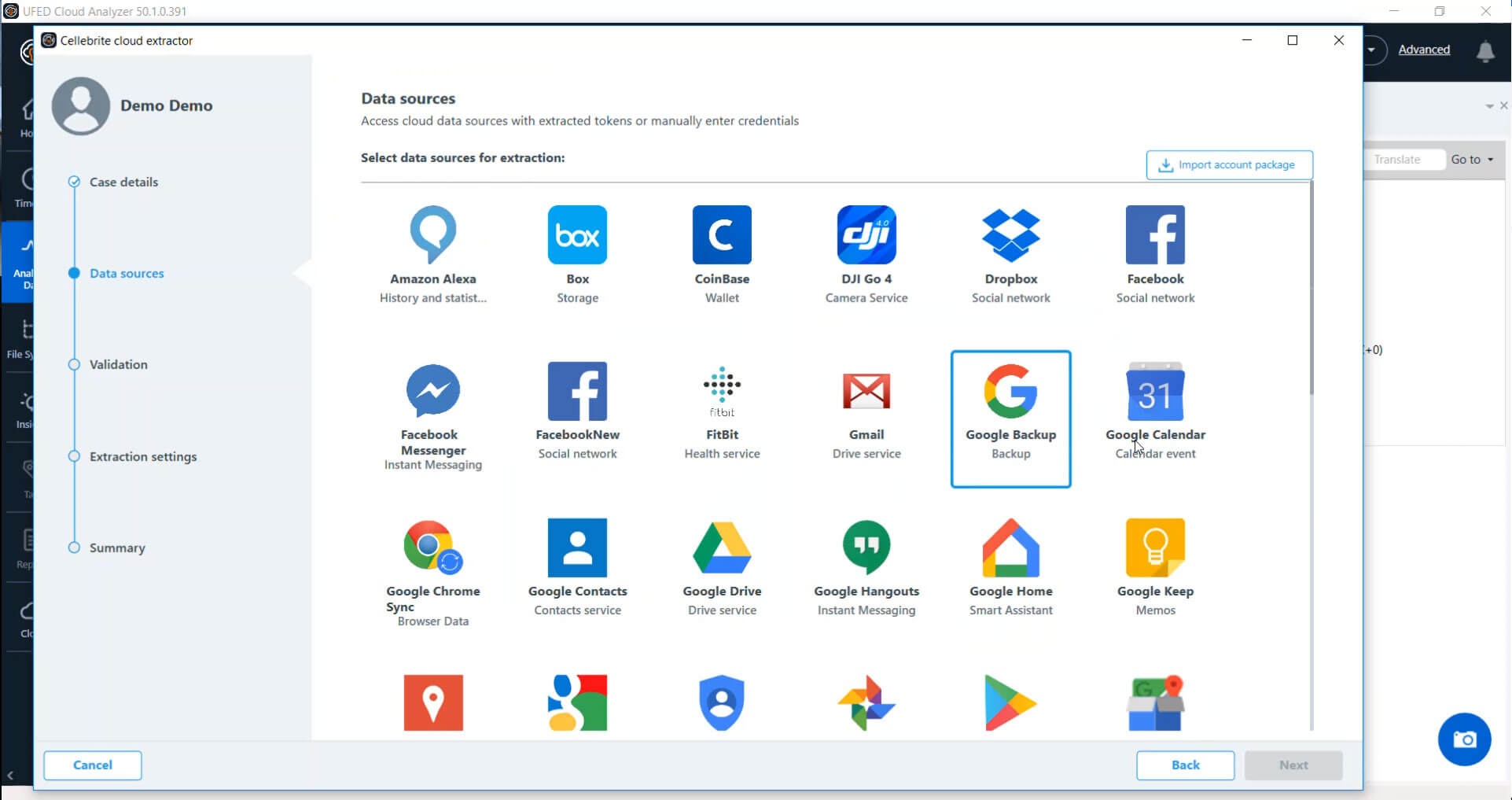
Lawfully access and collect new evidence hiding in social media and private, cloud-based data archives - Fulfill Requests for Cloud-Based Private Data
Gain lawful access to time-sensitive evidence from over 50 of the most popular social media and cloud-based sources - Capture and Review Public Data
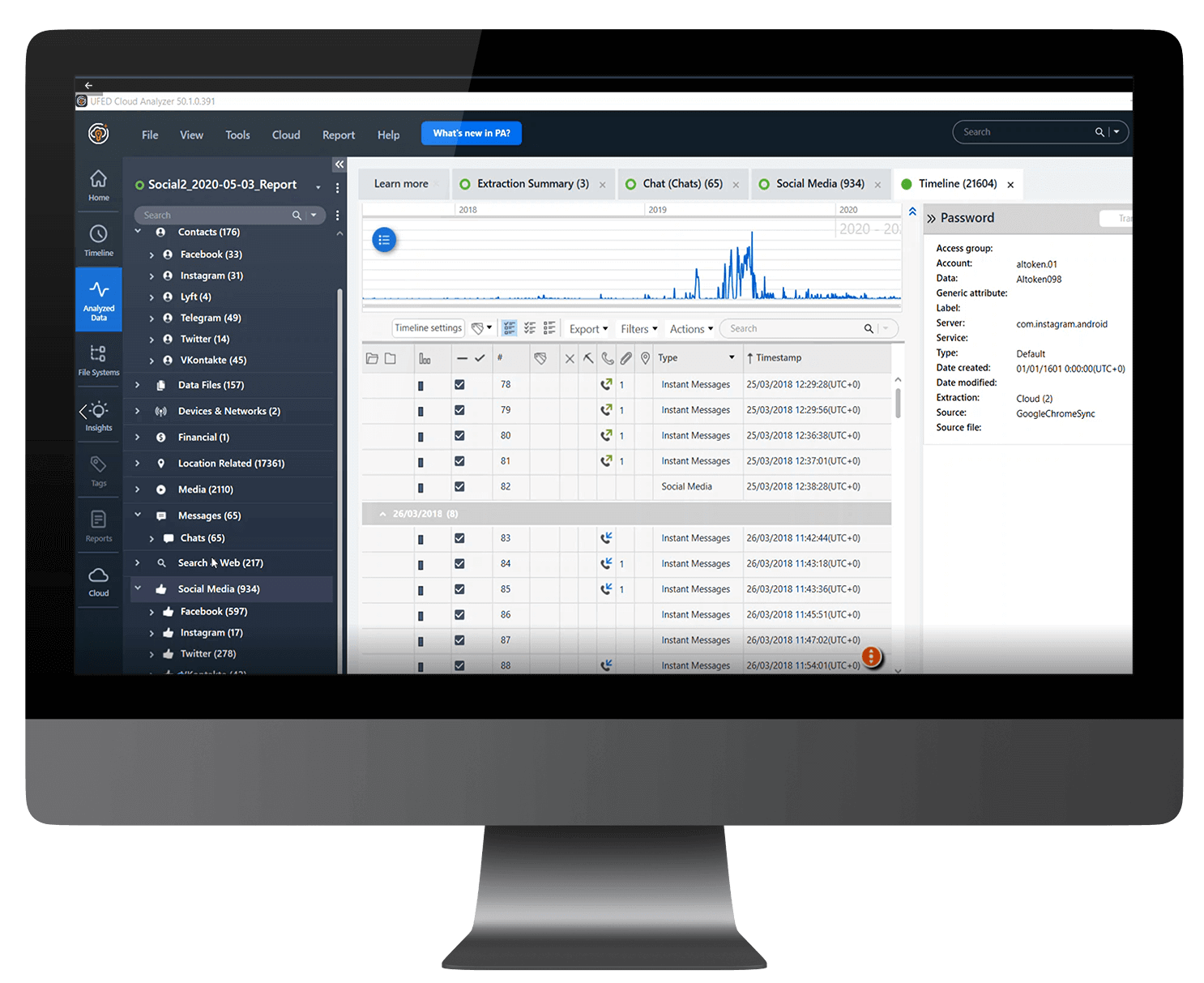
Easily access, view, and incorporate publicly available data into your investigations including location information, profiles, images, files, and social communications from popular apps such as Facebook, Twitter, and Instagram - Visualize Data in a Unified Format
Normalize different cloud data sources in a unified view to analyze them by Timeline, File Thumbnails, Contacts, or Maps formats. Search, filter, and sort available data across platforms
Discover Deeper Evidence Sources
Gain insights into a subject’s intentions and interests by accessing their search history, then map their recent movements minute by minute.
Search Their Searches
Collect a subject’s history of text searches, visited pages, voice-search recordings and translations from Google web history. View text searches conducted with Chrome and Safari on iOS devices backed-up in iCloud.
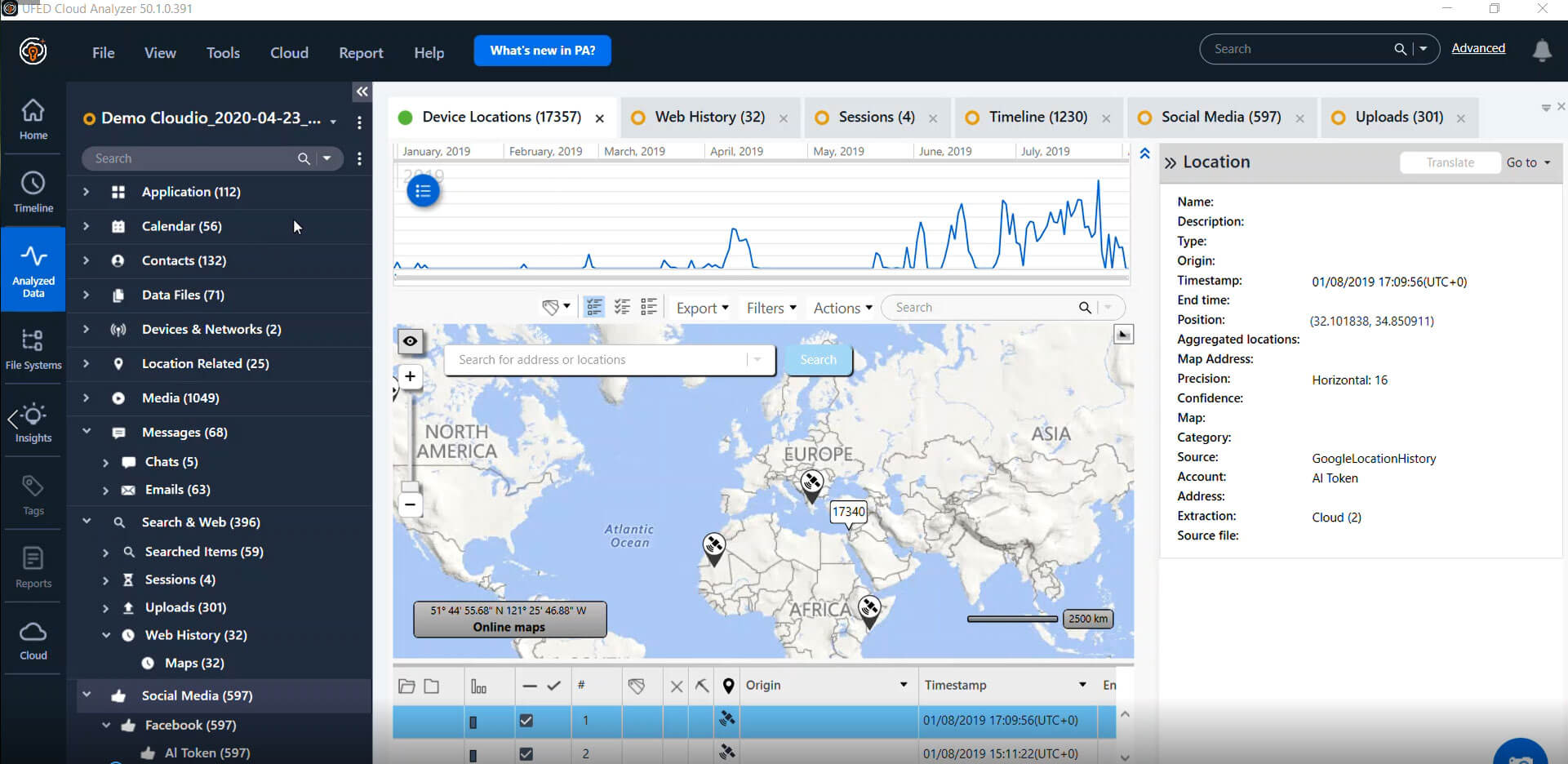
Explore Location History
Collect detailed location information from a suspect’s or victim’s private Google Location History, in order to track time-stamped movements minute by minute.
Track Online Behavior
Analyze posts, likes, events, and connections to better understand a suspect’s or victim’s interests, relationships, opinions and daily activities.
Start Solving Cases Faster
Find out how Cellebrite Digital Intelligence solutions can help your investigations.
Accelerate Justice through Expert Digital Intelligence Training
Embark on your educational journey with Cellebrite Training, where we prioritize your success. Our comprehensive courses empower you to accelerate your examination workflow, strengthen investigations, and close cases faster.
Gain mastery over techniques, tools, and methodologies crucial for navigating digital investigations with confidence. We focus on your success, guiding you to be more efficient, productive, and esteemed in the dynamic field of digital investigations.
- Learn more
Acquire the basics to collect, preserve, and analyze data across public and private domains, including social media, files, and more.

Cellebrite Cloud Data Examiner (CCDE)
- Learn more
Specialize in advanced analysis and search techniques utilizing Physical Analyzer.

Cellebrite Certified Physical Analyst (CCPA)