Device Type

Episode 21: I BEG TO DFIR – How iOS Biome Data Reveals Digital Evidence in iOS Forensics – Digital Forensics Webinar

Cellebrite Leads the Way: Unlocking the Latest iOS Versions and iPhone Devices

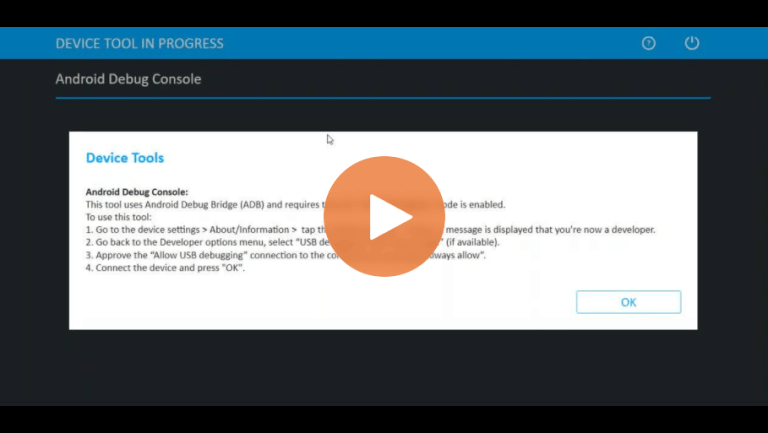
Android Forensics, Smart Flow, Selective File System Extraction
Part 2 of Cellebrite Solutions 2022 Update Summary
iOS Forensics Advanced Logical File System Extraction and CHECKM8 for iPhones
Part 1 of Cellebrite Solutions 2023 Update Summary
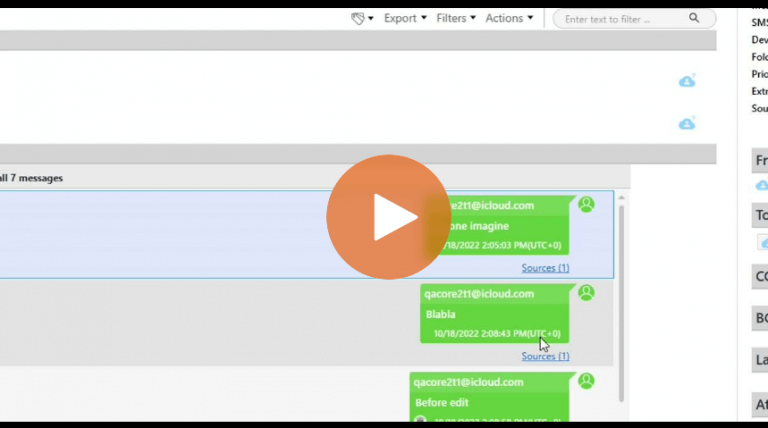
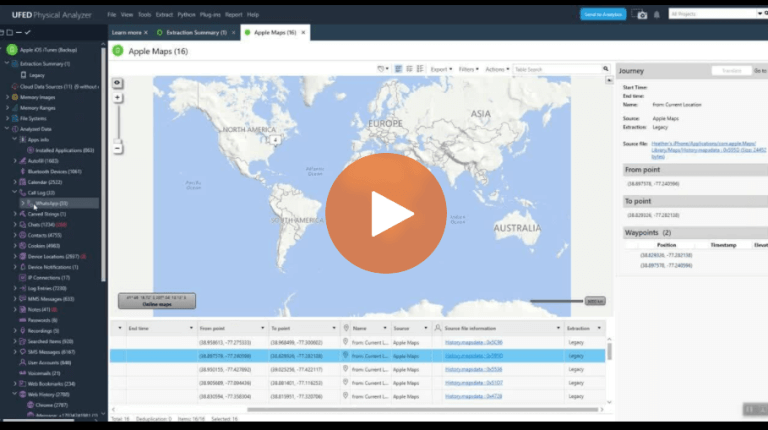
How to Examine Sent Messages Using New Mobile Forensics Features for iOS 16 in Physical Analyzer

Part 2: Walk-Through of Answers to the 2021 CTF – Marsha’s PC

Part 1: Walk-Through of Answers to the 2021 CTF – Investigating Heisenberg’s Android Device

6 Ways Cellebrite Premium Enterprise (ES) Has Become the Industry Game-Changer by Increasing Your Labs’ Capabilities Like Never Before

How to Use the Selective File System Extraction in Cellebrite UFED
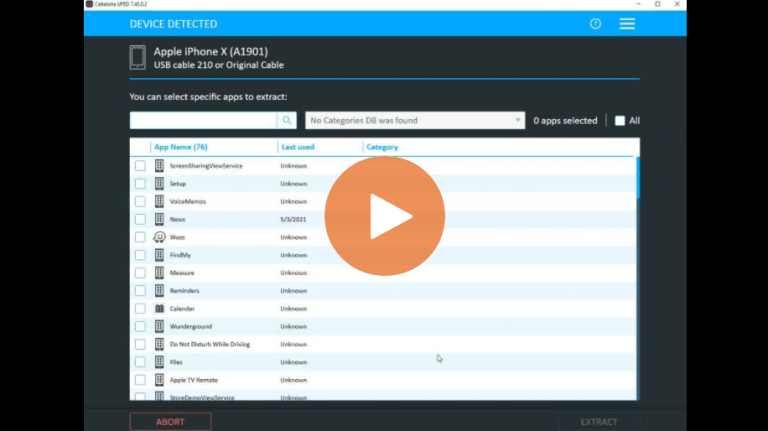
Cellebrite UFED Selective File System Extractions Now Available for iOS Devices

Selective Mobile Forensics Decoding in Cellebrite Physical Analyzer
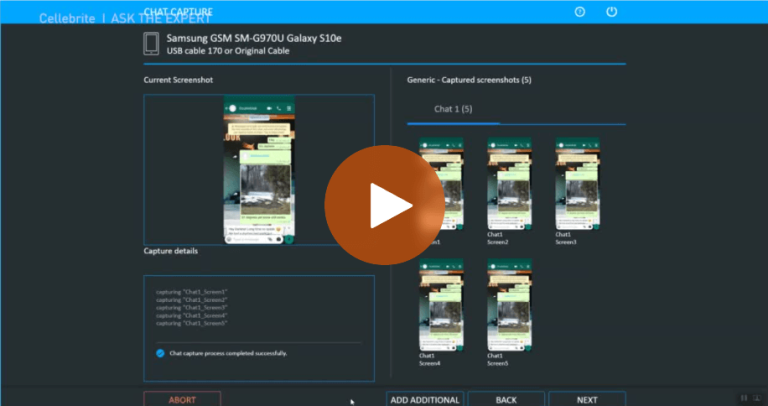
Chat Capture: Collect Data from Android Devices with Cellebrite UFED
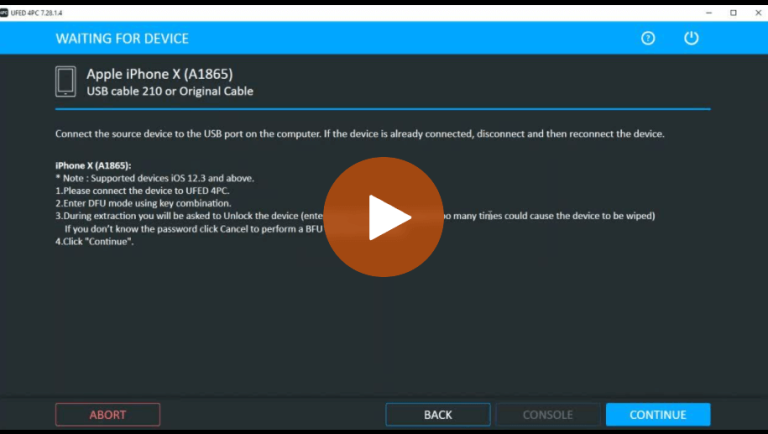
How To Perform BFU Data Collection Using checkm8 in Cellebrite UFED
All Cellebrite UFED Options for iOS Data Collection in UFED

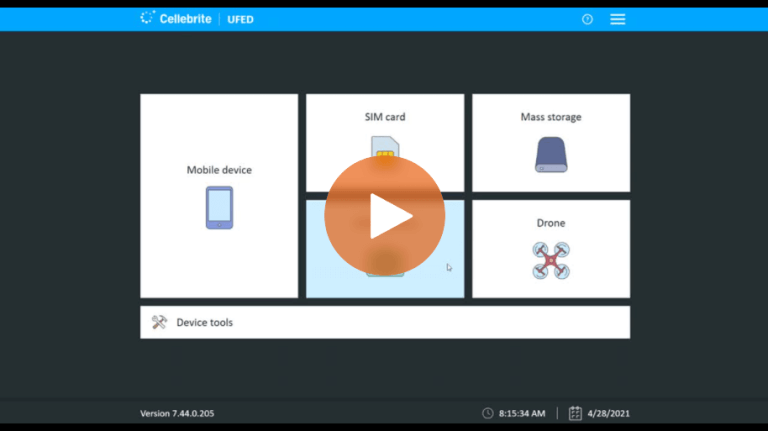
UFED Fundamentals Matter – You Asked, We Answered
Unencrypted vs. Encrypted Data Dump From an iPhone with iOS13 – Cellebrite Physical Analyzer