How to Lawfully Collect the Maximum Amount of Data From Android Devices

Join me as I take a look at Android device data collection – a repeated talking point at recent conferences.
People are often concerned about missing files, or why certain application data isn’t parsed. This is important because the extraction will impact your analysis and the investigation.
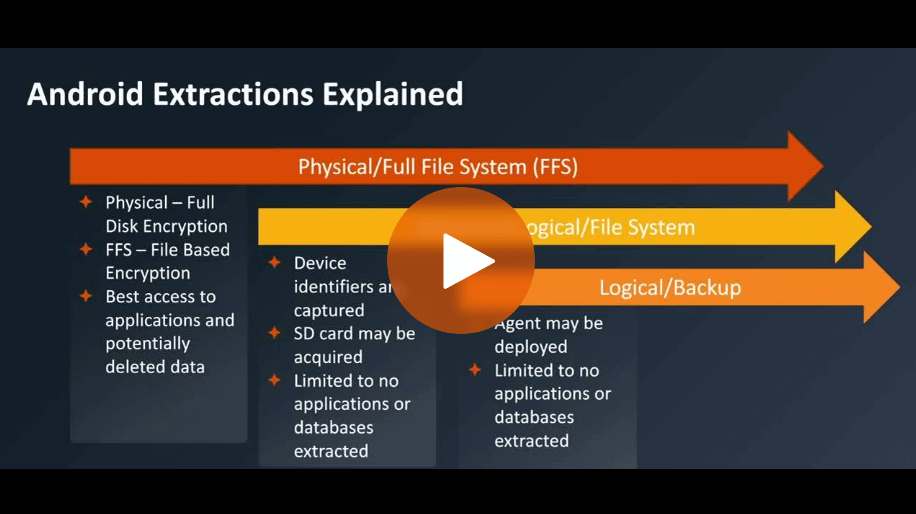
A physical or a full file system extraction is best: the physical will only work for full disc encrypted devices which are the older Androids that you may come across.
The full file system works best on file-based encrypted and newer Android devices and will give the best access, and the most access to the application data of interest.
An advanced logical or a file system is the best way to get simple device identifiers. Even if you get a full file system, you still want to get that advanced logical system because it’s a good way to get the SD card, if there is one, and certain device identifiers. You will most likely get limited or no applications or databases because Android restricts that.
The final issue is a logical backup. You will find that an agent will most often be deployed onto the device, which means you’re installing software onto the phone to extract information. This is consistent across most commercial tools with limited or no applications or databases extracted because Android protects this information.
So, the bottom line is full file system access is your best bet for newer Androids, and otherwise, always try to get a physical system extraction.
Watch the full episode to learn more.