Physical Analyzer 7.58 – iOS Features and Parsing Enhancements for Mobile Device Forensics
At Cellebrite we aim to parse the latest and greatest artifacts, applications, and operating system updates. If you are a mobile forensic examiner, you know this isn’t an easy feat as everything is constantly changing. This blog will highlight features that have been added into PA 7.57 and 7.58 for iOS devices. Each release of Physical Analyzer will add enhancements to make your examinations a bit easier.
This blog will cover the following:
-
-
- FindMy
- iOS Hidden Photos
- iOS 16 Biomes
-
FindMy
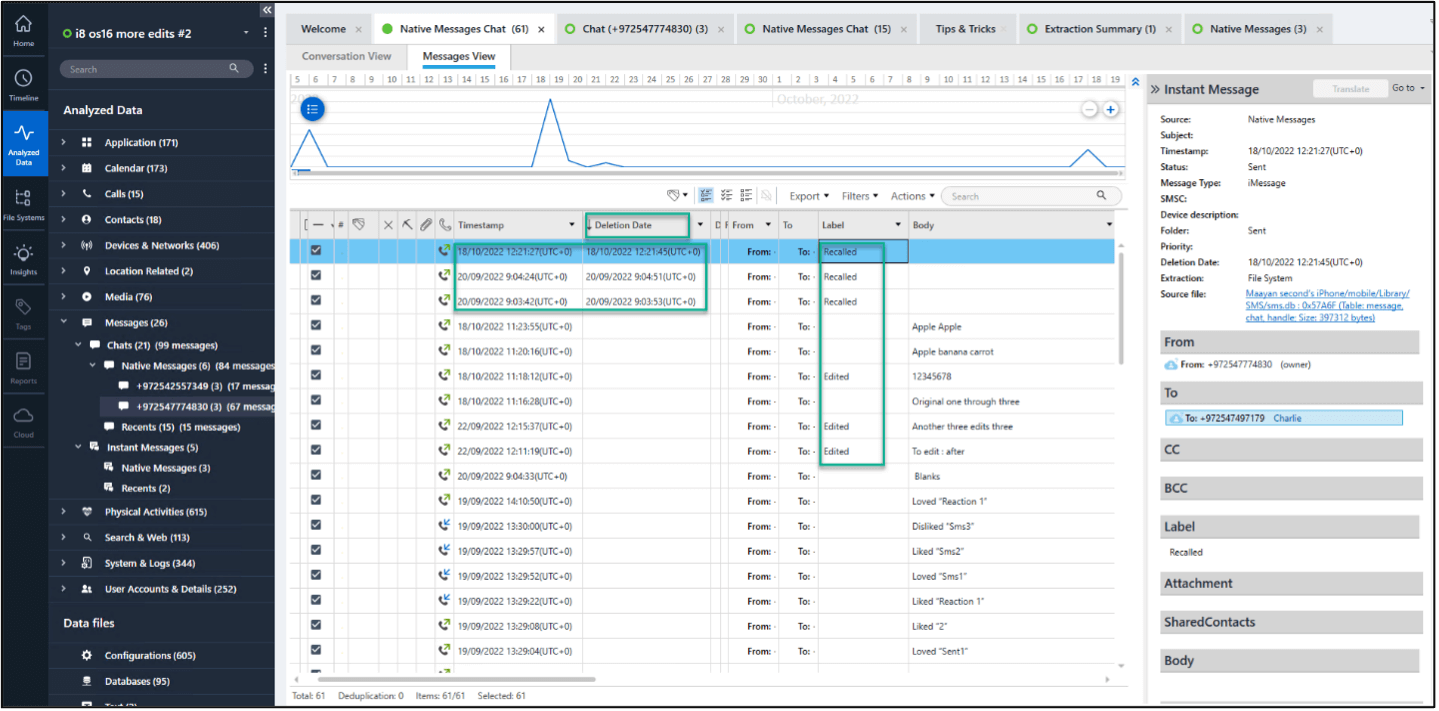
FindyMy iOS device artifacts can be helpful in investigations. Physical Analyzer now supports parsing of these artifacts to include accounts, devices, locations and more. This includes linked devices such as AirTags, AirPods, Macs, etc. When you follow the source files, it will lead you to /private/var/mobile/Library/Caches/com.apple.findmy.fmipcore.
FindyMy iOS device artifacts can be helpful in investigations.
iOS Hidden Photos
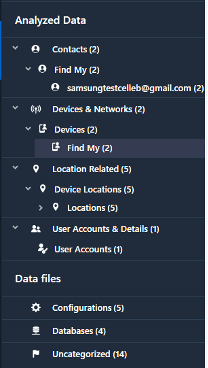
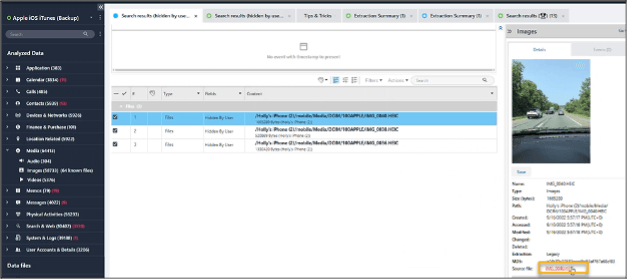
Our parsing efforts and the work of our developers often come from a customer request. Recently, a customer needed to filter photos hidden by the user on an iOS device. This capability was covered in a Tip Tues and is available in Physical Analyzer 7.58. To leverage this feature, you must search for “Hidden by User” in the loaded iOS extraction.
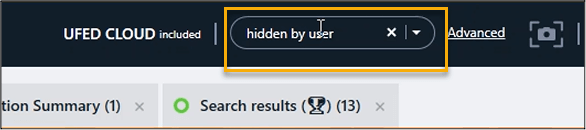
Search for “Hidden by User” in the loaded iOS extraction.
Next, you can select the search results from one device of interest or all. This list is what the query below can be used to validate. You should be provided with a complete listing of the photos the user hid on their iOS device.
A complete listing of the photos the user hid on their iOS device.
To validate or to better understand how we are parsing this, do the following. When you find an image of interest, select the source file.
When you find an image of interest, select the source file.
The final thing to validate is the flag shown below when looking at the File Info tab in Physical Analyzer.
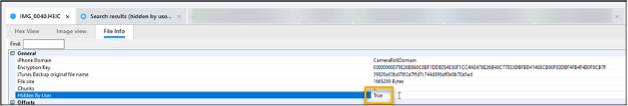
Validate the flag shown below when looking at the File Info tab in Physical Analyzer.
Hidden photos are important as this is an intentional action by the device user. Heather wrote a query that can be used to parse the photos.sqlite database to create a quick list of hidden images and videos. To leverage this, open the database in the SQLite Wizard and paste the query provided below.
This can also be used with external SQLite database viewers. Make sure you use the correct version of the query based on the iOS version. Feel free to modify this query as needed. It’s fantastic for validating your find inside of Physical Analyzer when you run the keyword search recommended above.
iOS 14 – iOS 16 – Show Hidden Photos
Select
z_pk,
zfilename AS "File Name",
zduration AS "Duration in Seconds",
case
when ztrashedstate = 1 then "Deleted"
else "N/A"
end AS "Is Deleted",
case
when zhidden =1 then "Hidden"
else 'N/A'
end AS "Is Hidden",
datetime(ztrasheddate+978307200,'unixepoch','localtime') AS "Date Deleted",
datetime(zaddeddate+978307200,'unixepoch','localtime') AS "Date Added",
datetime(zdatecreated+978307200,'unixepoch','localtime') AS "Date Created",
datetime(zmodificationdate+978307200,'unixepoch','localtime') AS "Date Modified",
zdirectory AS "File Path"
from zasset
order by “Is Hidden” ASC
iOS 13 and below – Show Hidden Photos
Select
z_pk,
zfilename AS "File Name",
zduration AS "Duration in Seconds",
case
when ztrashedstate = 1 then "Deleted"
else "N/A"
end AS "Is Deleted",
case
when zhidden =1 then "Hidden"
else 'N/A'
end AS "Is Hidden",
datetime(ztrasheddate+978307200,'unixepoch','localtime') AS "Date Deleted",
datetime(zaddeddate+978307200,'unixepoch','localtime') AS "Date Added",
datetime(zdatecreated+978307200,'unixepoch','localtime') AS "Date Created",
datetime(zmodificationdate+978307200,'unixepoch','localtime') AS "Date Modified",
zdirectory AS "File Path"
from zgenericasset
order by “Is Hidden” ASC
I used ArtEx in the example below to validate using the query provided. Note: this photos.sqlite is different from the evidence shown in the Physical Analyzer screenshot above, but the concept is what matters.
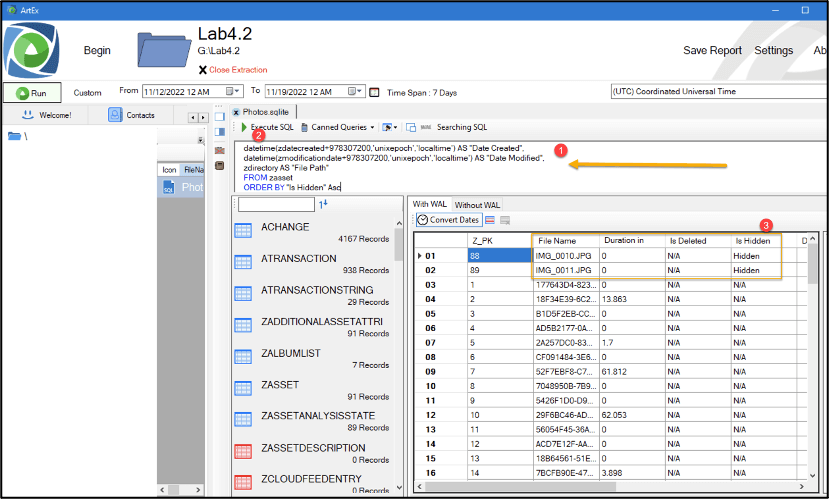
Use ArtEx to validate using the query provided.
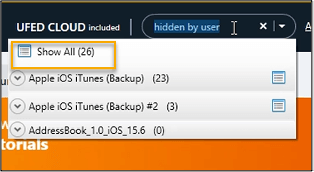
iOS16 Edit and Unsend Messages
iOS 16 introduced the ability to edit and unsend messages when the sender and receiver both have iOS 16 running on the Apple device. Prior to the release of iOS 16, our own Ian Whiffin blogged about the changes made to the sms.db when these user-created changes occurred. Physical Analyzer parses the sms.db and provides new values “Edited’ and “Recalled” where “Recalled” means unsent.
As stated in Ian’s blog, you only have about 15 mins to modify the original message. In addition, Physical Analyzer added another value for “Deletion Date” for messages when it is known when they were deleted, NOT just the unsent or “Recalled” messages.
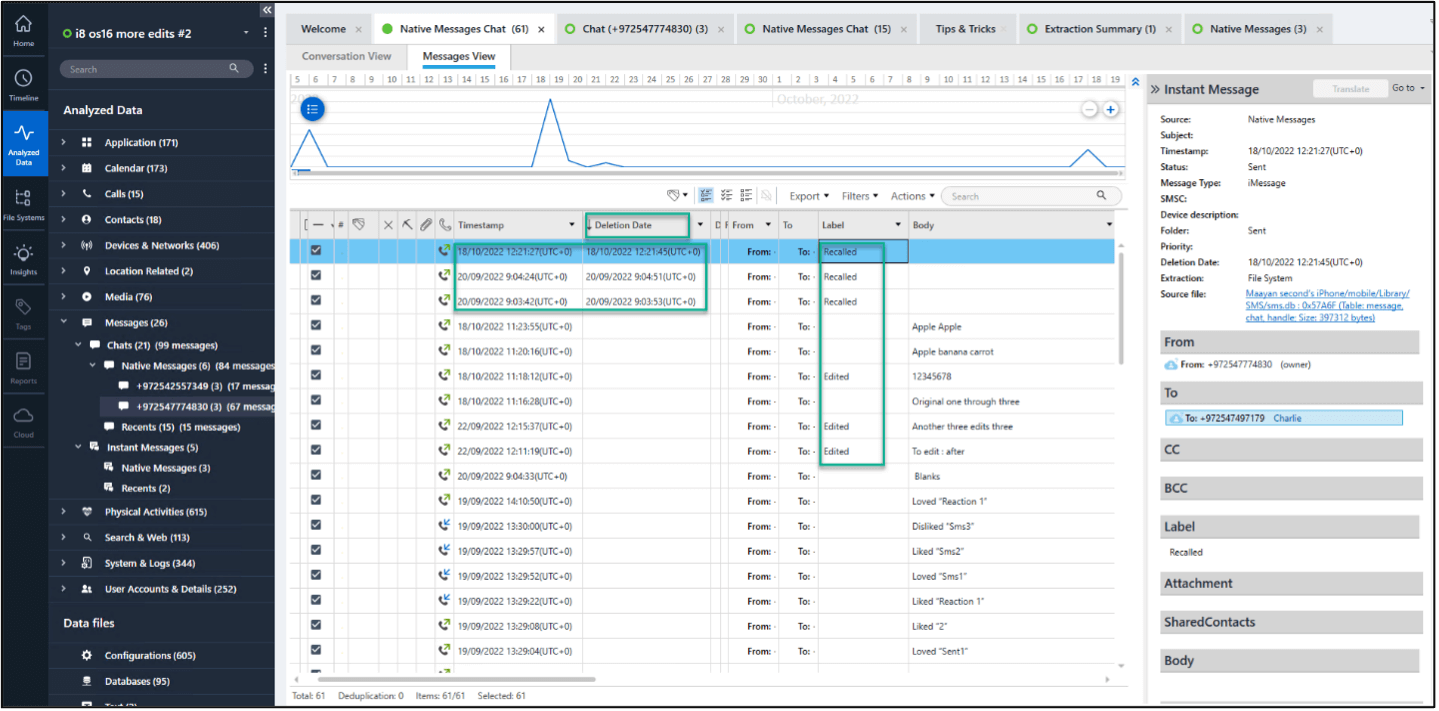
Physical Analyzer added another value for “Deletion Date” for messages when it is known when they were deleted.
For Undo Sent Messages(‘Recalled’) no Messages or attachment can be recovered. Edit messages are linked and the examiner can use the “Go To” button in Physical Analyzer to review the conversation.
In the example below, the message was edited 3 times you will see 4 entries (3 of them will have the value “edited” in the label field). The timestamp on the “edited” messages is the time they were edited or changed by the user. With exception of the most recent message edit, the rest of the edited messages (including the original) will be shown as “deleted” in Physical Analyzer.
If we look at the messages below, the arrows are pointing to the previous message, prior to the edit(s). These messages will be annotated with a trash icon (essentially marked as deleted because it was changed by the user.)
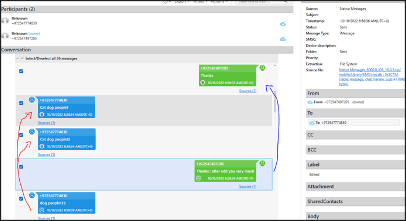
These messages will be annotated with a trash icon.
The message that is intact is the latest version that was kept by the user. Meaning the only version that wasn’t edited or unsent. An easy way to hop to the conversation and see all revisions is to leverage the “Go To” button in Physical Analyzer.
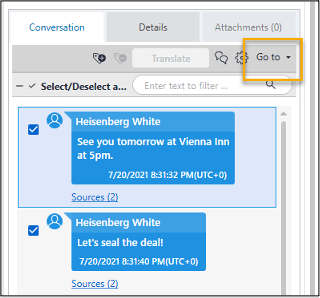
An easy way to hop to the conversation and see all revisions
For more information on the unsend and edit feature in iOS 16, read Ian Whiffin’s blog post on the topic: https://www.doubleblak.com/blogPosts.php?id=27