Episode 19: Nothing to see here – I BEG TO DFIR – Smart Flow for Mobile Device Forensics

Aired on: December 13th, 2022
Duration: 45 minutes
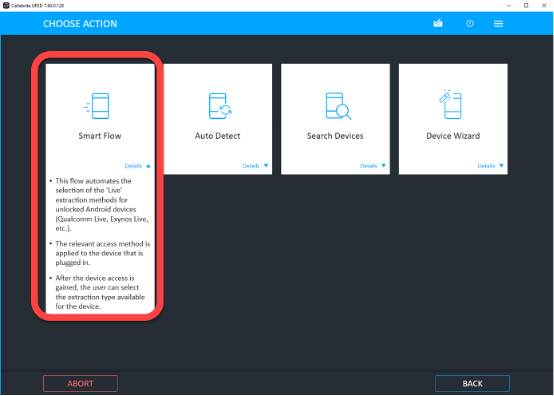
Navigating the file system extraction profiles can get confusing at times.
As there are many mobile forensics methods to choose from, specific models, or using generic ones, how do you determine where to start?
UFED’s Smart Flow has revolutionized this process by making it simple, with just one button. We will also cover the new selective extraction features in this new version.
Note: You can view the answers to the questions about how these new features can help your investigations below in the Q + A section.
So, in this session of I Beg to DFIR, Heather Mahalik, Cellebrite’s Senior Director of Digital Intelligence, and Product Specialists Ronen Engler and Paul Lorentz discuss UFED Smart Flow and its many capabilities.
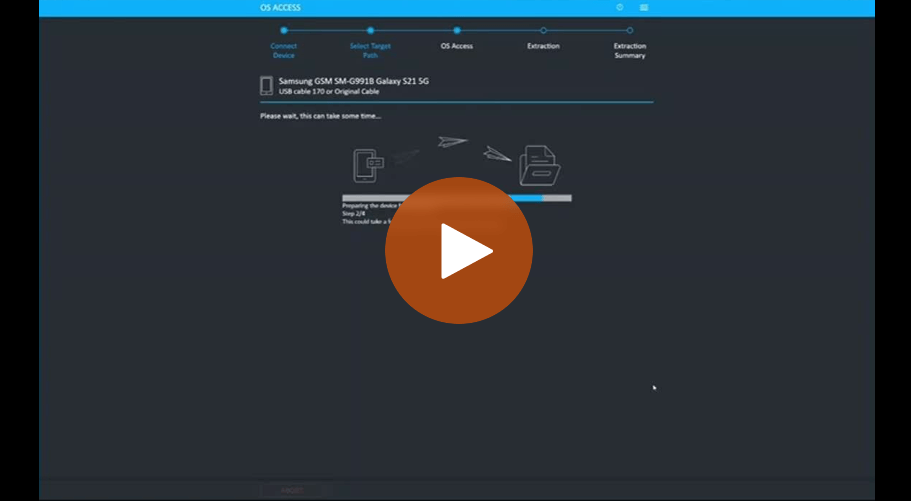
Challenge identifying a device
During training classes and real sessions where people work with devices, they sometimes struggle to identify the device. This is because there are so many different devices, and even when looking at a specific model, such as a Samsung Galaxy S21, there are multiple models of that which could have different chipsets.
So, the fragmentation of the devices out there is the first challenge. Even when you select the right device in UFED, over the years we have added many different capabilities such as:
- Logical extraction
- Advanced logical
- File system
- Physical extraction
And even within these methods, there are different backend communication methods that we utilize with the devices – whether we’re using APIs to extract the data and we only get access to certain data, or with an advanced method utilizing a mix of backup data or some other ways to extract data from media that could be different from databases.
Then there are different levels as we go deeper, like getting file system if it’s a partial file system, or user data file system or the entire file system all the way to physical extractions.
It can be very confusing and difficult to keep up to date with all the new features in some of the tools which makes your job very difficult, as it’s hard to stay on top of everything.
This is what led us to come up with UFED Smart Flow in Physical Analyzer (PA) version 7.60 which simplifies the process and provides many capabilities for users.
We had some very good flows but relied on the user to understand which type of device they were working with. asking themselves:
- Is it a Qualcomm-based device?
- Is this an MTK device?
- Which chipset is it?
- Which security patch level is on the device?
We began adding features, starting off with Qualcomm Live, and made tweaks. These were very generic capabilities and all for unlocked devices.
Watch the tip Tuesday short video below by Heather on How to find the Qualcomm Live feature in UFED.

We added these new capabilities and access methods to give you a full file system or physical extraction. However, the responsibility was still on the user to discover if the method was listed under their profile to enable them to get the richest type of extraction.
This is where Smart Flow came in, by introducing a simplified way to automatically go through those flows to give you access. The difference in the new version of UFED Smart Flow is we added a new feature, the universal Android Live, following the naming convention that we did in the past.
This is a new capability for advanced access that gives escalated privileges to a wide range of devices that were not supported in the past. It expands coverage exponentially and supports a very large number of devices.
It gives you escalated privilege which is an admin level of access to devices to give you full access and the details of the extraction that you want. It takes away the guessing game of whether a device is supported or not.
That’s why we recommend starting with Smart Flow. It’s going to apply the proper method without you having to ask if it’s possible. It automatically does it.
We are going to be adding more documentation to show which types of devices are supported. It is a generic capability that we know supports hundreds, if not thousands, of devices, including the entire Google Pixel line, to be able to have access to a full file system extraction. We’re removing the guessing from knowing which profile to pick.
You may have to be patient with it because it’s a generic method that goes through all the methods to identify the best one for the device you are working on. But it does work and then it’s magic when it actually finds the right fit and continues the process. It opens the door completely to full access and extractions. Not only did we combine the flow, but we made it easier, and we also added a new method that only exists in Smart Flow.
The universal Android Live access is part of Smart Flow, so if you’re going to try to access other devices, that new access method is only available through Smart Flow. Your best chance to access escalated privilege extractions is through using the new version of Smart Flow. We added the new access method and select by file.
Privacy, speed and targeted collections are very important, so we provide the ability to specifically leverage the escalated privilege that Smart Flow provides and then drill down into the file system and choose the specific file you want to extract.
It’s a forensically sound extraction method that gives you the highest level of privilege, meaning admin control over devices. Selective extractions have been around for a while, but not to the extent of having full escalated privileges to get access.
This subject is covered in several Tip Tuesdays sessions.
Full file system access is required because logical extractions are not good enough anymore, especially with Android. Most of the user data is not going to be included in any logical or advanced logical backup type extraction with Android. We need access to the actual files that are tracking all the activity and give us access to the databases as well.
And this is where I think Android is really different from iOS because on iOS you can get an encrypted backup file and a lot of user data. But it’s different with Android and this is what makes it very difficult. We want privileged escalation, even if it’s in a temporary form in order to access those databases.
Samsung Rubin
With UFED we get access to things like Samsung Rubin, all of the screen time and the artifacts behind the scenes that give us a better look at what was accessed, when it was accessed, and how it was accessed. Those deep-level artifacts are what we all really need to solve most investigations. We’re working with encrypted apps, so this isn’t going to be a total solution for encrypted apps. Some of the apps will remain encrypted depending on your level of extraction and the type of privileged escalation that you get.
Watch the video: How to Use Samsung Rubin in Cellebrite Physical Analyzer

But remember to use Chat Capture which a lot of people forget about. Include it at the end of every Android acquisition you do. It’s great because you can choose generic and go in and manually control what you actually capture from the Android device and it can be included in your report.
Watch the video: Ask the Expert: Chat Capture – Collect Data from Android Devices in Cellebrite UFED

When it comes to encrypted vaults, these do matter, and we’ve seen secure folders on many devices. This comes back to why privilege matters. We’re not only dealing with encryption at the device level, you’re also dealing with it now in the application and the vault piece as well. So this makes it increasingly difficult to gain access to the data you need.
Remember, you can’t do a logical extraction and expect magic to happen in your analysis. If you have an extraction and don’t understand why Physical Analyzer is not parsing it, it’s because you didn’t pull the data correctly – so use Smart Flow.
Final Thoughts
- You can reach us for information or to give feedback at: ibegtodfir@cellebrite.com
- We also have a channel in the Forensics Discord channel, so you can email questions there or post messages to us.
- Every time that there’s a big new feature in PA or UFED, we try to show them in two minutes or less on the Cellebrite website under Resources. That’s where you’ll find Tip Tuesdays, Carved from Unallocated, blogs, I Beg to DFIR, and Ctrl+Alt+Delete.
- Ctrl+Alt+Delete runs on the first Wednesday of every month, while I Beg to DFIR runs on a different day of every month.
- So make sure you stay tuned for those. If you have topics you would like us to cover, just let us know. We also host guest speakers on Ctrl+Alt+Delete. If you have something you want to share, just reach out to: heather@cellebrite.com to get you scheduled
 Heather Mahalik Senior Director of Digital Intelligence at Cellebrite
Heather Mahalik Senior Director of Digital Intelligence at CellebriteOver 18 years experience in digital forensics and has been an expert of choice for law enforcement and intelligence agencies. She has worked high profile cases from child exploitation to Osama Bin Laden’s digital media. Heather likes wine, bourbon, reading, researching, and traveling.
 Paul Lorentz Product Specialist at Cellebrite
Paul Lorentz Product Specialist at CellebriteClose to 15 years in Canadian Law Enforcement before joining Cellebrite. Last assignment was in the Computer Forensic Unit, conducting examinations related to file ranging from child exploitation, organized crime and homicides. Likes Hockey, fishing, and beaver tails.
 Ronen Engler Product Specialist at Cellebrite
Ronen Engler Product Specialist at CellebriteApplying over 20 years of engineering experience, holding Masters of Science in Electrical Engineering from NYU and handling special projects for 10 years now @ Cellebrite – even though Twitter banned him.