
Exploring the Windows Activity Timeline, Part 3: The Value of Clipboard Content
In Parts 1 and 2 of this series on the Windows Activity Timeline (just “Timeline” from here on out) we discussed how Cellebrite Inspector and Cellebrite Digital Collector can help investigators find valuable evidence on either Android or Mac devices respectively. We also took a deeper dive into the source database, ActivitiesCache.db, which stores reams of data about actions each user has engaged in on a system (i.e. web browsing and document access). Further, this evidence can be synced across multiple Windows machines that a user logs in to with the same MS account.
Timeline can also store evidence of activities that occurred on non-Windows machines if Office365 is attached to the same account as the MS login account. In this blog, we’ll take a look at a type of user activity that you might not think of when examining this particular artifact – Clipboard content.
Before we begin we should note one thing: Timeline analysis is a fast-moving target. The db itself, as well as the behavior of the system, changes with nearly every Windows release. Even without the constant changes, there are large parts of the Timeline we know little about. There is a lot more work needed here for verification as well as figuring out the unknown parts. With that in mind, this post will provide a bit more detail on the process I used to figure out how the Timeline and Clipboard are connected. Hopefully, this information will help other curious people perform their own testing and add to the body of what is known.
The Problem Statement
When digging around a (long) while ago in the ActivitiesCache.db on one of the test VMs I use, I saw that there was a column in the Activities table, named “Clipboard Payload,“ that had data in it. I had seen the column before, but I had not seen it populated before. It looked something like Figure 1 below. Immediately, my forensics Spidey sense went off telling me this could be interesting, so I dug in.
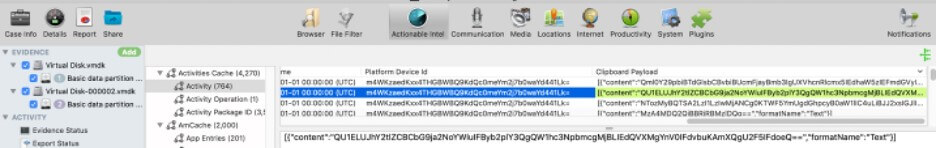
Figure 1
I loaded the VM into Cellebrite Inspector to do some more looking around. The Clipboard Payload column showed some obvious base64- encoded data. The decoded string was “AMD-Backed Blockchain Project Amassing 20K GPUs but Won’t Say Why.” Apparently, I was doing some cryptocurrency reading and copied the article title. But how did the data get there? How long would it stick around? Was it stored anywhere else? Was it only text that could be stored? There were many questions that needed answering, so I decided to do some testing.
Methodology
I had a notion of what some of the answers might be, and there were online sources [1] that had good information, but as I said before, the Timeline changes quickly. To answer some of these questions for myself, I recently spun up a fresh Windows 10 2004 VM and copied and pasted some text. Then I looked in the Timeline db, and there was no populated Clipboard Payload data. So, that was not super helpful.
Some brief googling reminded me that Windows 10 version 1809 added some new clipboard features: “Clipboard History” and “Clipboard Cloud Sync” [2-8]. I hypothesized that if the right configuration options (we’ll see them below) were selected, Windows would keep a limited history of text and images a user copied using “CTRL-C.” They could then be accessed with the WinKey-V key combo. Depending again on the settings, some types of copied data might even be synced across machines.
I then tried the Clipboard History key combo WinKey-V in my 2004 VM and got this sad message:

Figure 2
I assumed I needed to tinker with some settings. After more googling I turned on Clipboard History in Settings → System → Clipboard:
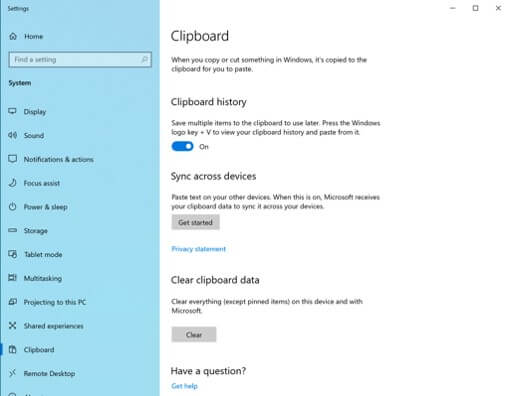
Figure 3
Then I copied some text from my web browser, tried the WinKey-V again, and behold:

Figure 4
But when I looked in the Timeline db again, there still was no populated Clipboard Payload data. Luckily there were more settings to toggle.
Next, I enabled the “Sync across devices” setting to turn on “Clipboard Cloud Sync.”
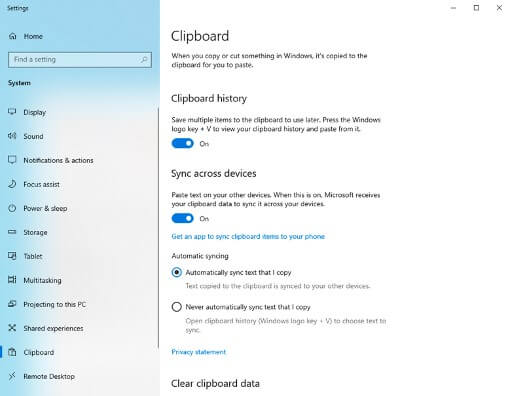
Figure 5
Now, I thought this might have a better chance of working, so on the fresh 2004 VM I did the following (see Figure 6 below):
-
- Logged in with one of my test MS accounts
- Opened Notepad
- Inserted a timestamp for good measure
- Wrote some text
- Selected the text
- Right-clicked and copied the text
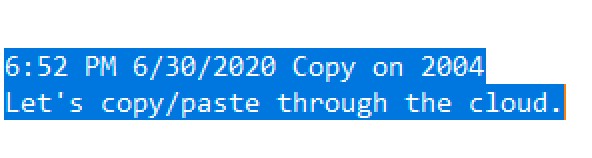
Figure 6
Then I opened up another machine, this one was a Windows 10 1809 test VM, and did the following:
- Logged in with the same MS account as on the 2004 VM
- Made sure it had the same clipboard settings
- Opened Notepad
- Inserted a timestamp
- Right-clicked and selected “paste”
Note: Be careful not to have copied/pasted anything else in this VM before.
Et viola! The text I had copied above in the 2004 machine pasted in the 1809 machine (see Figure 7 below).
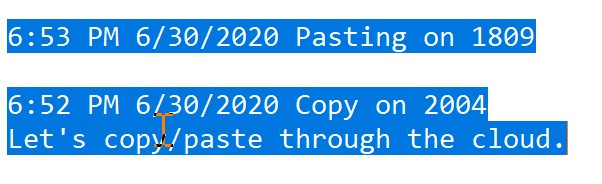
Figure 7
This time when I took a quick look at the Timeline db on the 2004 machine, I saw some Clipboard Payload data populated. Now I was making some progress.
I then decided to take a closer look at the Timeline dbs from both the 2004 and 1809 machines and, using what we’ve seen in the previous posts and what we know now, see how this all worked in the Timeline.
To test this, I did the following:
- Opened Cellebrite Inspector and created a new case
- Added the VMDKs from each of the VMs to the case
- Made sure “Actionable Intel” processing was selected (it is by default)
- Looked at the Actionable Intel → Program Execution → Activities Cache section.
Going back and looking at the timestamps in my Notepad files from Figures 6 and 7 above, I noted that my copy/paste start time was around 6:50 PM on June 30, 2020. Then I sorted by Start Time and immediately noticed that there were many duplicate “Guid Id” entries in Figure 8 below (e.g., “AF42”… in rows one and three, and “F2FE”… in rows two and four are the same).
We know from previous posts that these are supposed to be unique identifiers for Activities. Our previous posts also showed us that we see duplicates here because the Activities have been synched across the two machines since I used the same MS account on both.
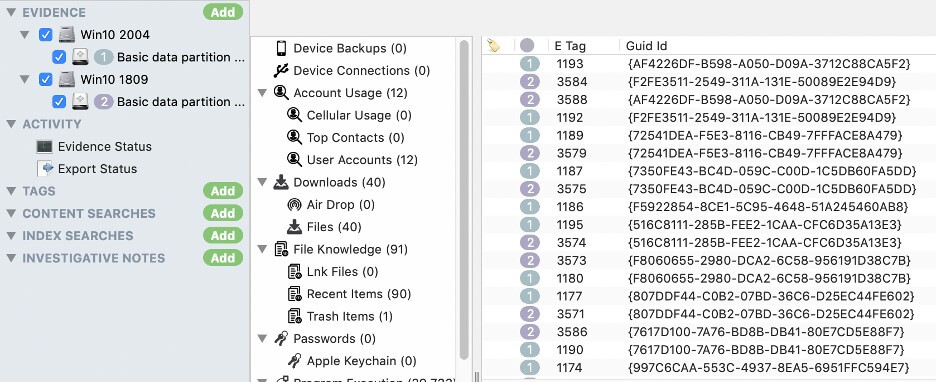
Figure 8
The duplicate data can sometimes be useful, but other times it can make things more difficult. This time it seemed like the latter case so, first I just looked at the Activities Cache from the 2004 machine by selecting just the Win10 2004 machine in the Evidence section of the “Component List.” This eliminated the duplicate entries, as we can see in Figure 9 below.
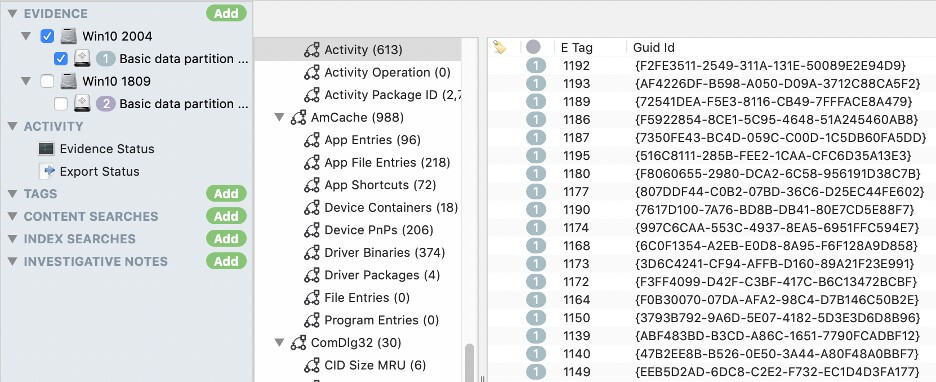
Figure 9
After sorting by “Start Time” we can see (Figure 10 below) 6-7 entries that might be relevant given the time frame when I did the copying and pasting. The “App Id” column tells us that all but one of the entries is related to Notepad. (Side note: I also used Cellebrite Inspector’s view filter to remove some other unrelated Activities.)
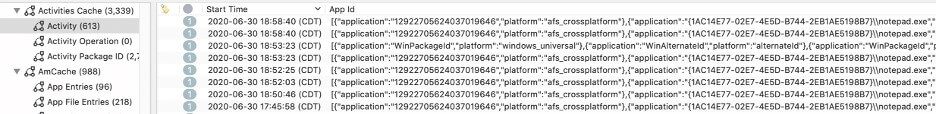
Figure 10
Scrolling right (see Figure 11 below) we can see that these Activities originated on two different machines based on the two different Platform Device IDs listed. Using the technique outlined in our previous post, you may remember that we can determine that the yugS… entries originated on the 1809 machine, and the mWKk… entries originated on the 2004 machine.
I then focused only on the entries originating on the 1809 machine, and as we can see in Figure 11 below, there is an Activity Type 5 for opening Notepad and an Activity Type 6 for engaging with the app. (The Activity Type 5 and 6 appear to be in reverse order, but on examining the Start Time, they both began at the same second, so they are listed in arbitrary order.) We can see the file “Notepad” was used to access in the “App Activity Id column: morecopypasta.txt file.” This is where we pasted in the text in Figure 7 above.
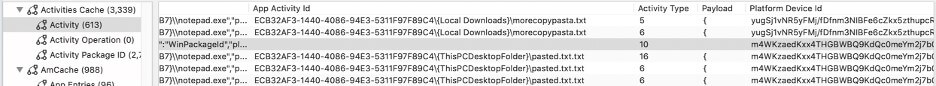
Figure 11
If we now focus on the entries originating on the 2004 machine, we can see there are four relevant lines in Figure 11 above. Two of them are Activity Type 6 meaning the user was engaged with the Notepad app. The file that Notepad was used to access we can see in the App Activity Id field: pasted.txt.txt.
This is the file I copied the text out of in Figure 6 above. There is also Activity Type 16, which tells us that Notepad was used for a copy or paste operation. And we can see Activity Type 10, which tells us that Clipboard activity occurred.
If we look further into Activity Type 16 (Copy/Paste) in Figure 12 below, the Group ID tells us that the operation was a Copy operation. The Clipboard Payload, when decoded from the base64 is:
6:52 PM 6/30/2020 Copy on 2004
Let’s copy/paste through the cloud
This matches the text I copied above, as seen in Figure 6.
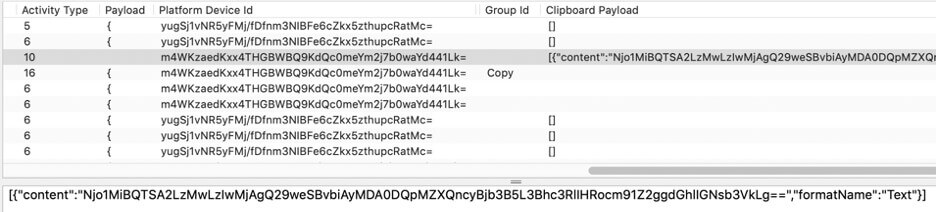
Figure 12
It is important to note that Activity Type 10 is not directly tied to Notepad by its App Id, App Activity Id, or any other field. We can only infer that copied or pasted text in the Clipboard Payload itself was copied from/paste to Notepad.
While most data gets synced between machines, not everything does. Let’s take a look at the same time frame in the Timeline db from the 1809 machine in Figure 13 below.

Figure 13
It looks pretty similar to the 2004 db, but when we scroll over a bit (see Figure 14 below), we see that one entry is missing.
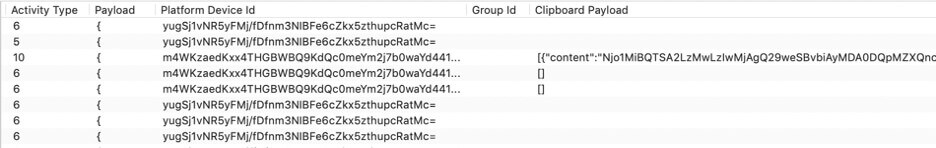
Figure 14
There is no Activity Type 16 shown in the 1809 Timeline db. We might have expected to see an Activity Type16 with a Group Id of “Paste” to match the other Activity Type 16 with a Group Id of “Copy.” I certainly did and with a different version of the Timeline we might have. But it wasn’t there now. Remember how we said this was a quickly moving target? Now that we have some understanding of how all of this looks in the Timeline db, let’s get back to our original set of questions in the Problem section above.
Results
After reviewing the above (and doing some additional spot testing specifically geared to answering our questions), we deduced the following:
How did the Clipboard Payload data get there?
In the experiment above we copied data on the 2004 machine and pasted it on the 1809 machine. This resulted in Clipboard Payload being populated with the base64-encoded version of the copied text. But further testing has found that all that is required to populate the data is to copy the text. No pasting is required.
How Long Does It Stick Around?
Looking at the Timeline database in Figure 15 below, we can see that each Activity has a Start Time and an Expiration Time. If we look at the difference between them, it always exactly 12 hours. And we know that Activities are deleted from the db on expiration. Putting this together means that copied text will stick around in the db for 12 hours and then be deleted.
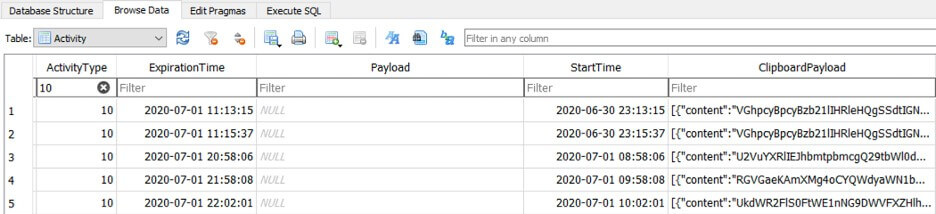
Figure 15
Is Clipboard data stored anywhere else?
After scouring the Timeline db for the 2004 machine, I found no other places that the Clipboard data was stored. However, knowing that different versions of Windows behave differently, I looked at the 1809 machine and found that for Activity Type 10, the Payload field holds a copy of the Clipboard Payload data.
Take a look at Figure 16 below from the 1809 machine where the Payload content in the bottom right panel matched the Clipboard Payload.
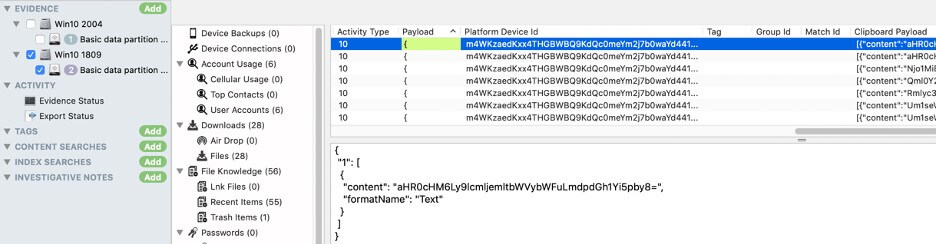
Figure 16
In Figure 17 below from the 2004 machine, however, the Payload field is empty.
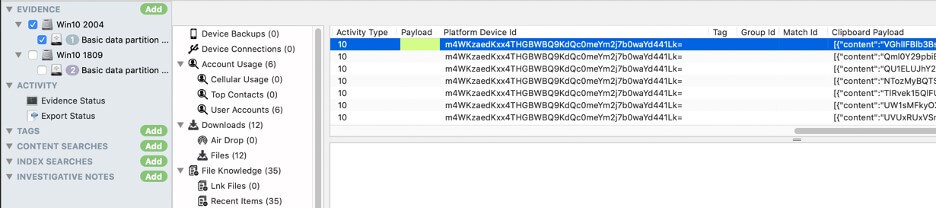
Figure 17
There is also some evidence that clipboard data may be stored outside of the timeline, but that is beyond the scope of today’s analysis.
Is Only Text Stored?
When we look at the Payload in Figure 16 above, we can see that the format name is “text.” This implies that there could possibly be non-text data stored in the Payload and therefore Clipboard Payload fields. There are even several sources (see reference below) that say that the Cloud Clipboard handles text and images.
Unfortunately, I have tried several methods to get an image to sync via the Clipboard Cloud Sync, or in the Timeline db and have not been able to make it happen. Maybe it’s a function that will work in the future; there’s some configuration to toggle, or I just didn’t “do it right.”
As you can see, diving into Timeline can reveal all kinds of information that you might not have thought to look for. Cellebrite Inspector and Cellebrite Digital Collector were designed to help make finding all of these new pieces of information much easier whether you’re tackling a Windows-based or Mac-based device.
We hope you found this series of blogs useful. Learn more about how Cellebrite Inspector and Cellebrite Digital Collector can help advance your investigations, here.
References
Below are some important references for those who would like to dig deeper into Timeline.
Forensic Analysis of Timeline, Clipboard History, and More
*** Definitely go see all the info and tools from Costas Katsavounidis here:
[1] Costas: https://github.com/kacos2000/WindowsTimeline
Forensic Analysis of Clipboard History
[2] https://thinkdfir.com/2018/10/14/clippy-history/
General Clipboard Information
[3] https://www.howtogeek.com/351978/using-windows-10s-new-clipboard-history-and-cloud-sync/
[4] https://community.windows.com/en-us/stories/cloud-clipboard-windows-10
Videos from MS
[6] https://channel9.msdn.com/events/Build/2017/B8108
[7] https://channel9.msdn.com/Events/Windows/Windows-Developer-Day-Fall-Creators-Update/WinDev011
[8] https://channel9.msdn.com/Events/Connect/2017/B111
Some Timeline Database Field Descriptions
The Developer Perspective
Activity
[10] https://docs.microsoft.com/en-us/graph/api/resources/projectrome-activity?view=graph-rest-1.0
History Item
[11] https://docs.microsoft.com/en-us/graph/api/resources/projectrome-historyitem?view=graph-rest-1.0
[12] https://docs.microsoft.com/en-us/windows/uwp/launch-resume/useractivities
Project Rome
[13] https://github.com/Microsoft/project-rome
Graph API
[14] https://developer.microsoft.com/en-us/graph
BBT Webinars and Blog Posts
https://cellebrite.com/en/windows-10-activity-timeline-an-investigators-gold-mine/
