
How a Suspect’s Pattern-of-life Analysis is Enhanced with KnowledgeC Database
Pattern-of-life analysis is usually meant to define a certain type of optical surveillance. However, the wealth of personal activity stored on digital devices, if legally accessed, can immediately show a user’s digital behavior mapped over an extended period of time.
When organized in this way, data can deliver insights into the frequency of routines and the location of behaviors. From internet browsing records to device usage logs, a smartphone constantly records the daily events generated from a smartphone’s user. The analysis of this data can both help to reconstruct past events as well as predict probable outcomes.

Cross-analysis is key
Digital investigators don’t have to infer what the schedule of a person of interest was, or the status of their device during a crime. Cross-analysis of timestamped activity combined with geolocation and device communication data can surface how an individual was relating to the scene of a crime.
In a recent investigation, the Australian Homicide Squad of the Victoria Police was able to extract GPS logs from a murder suspects’ phone. This led to the exact location of the deceased victim and helped solve the case.
Digital Forensics Analysts can now apply a constraint-based approach to selectively combine a persons demographic details such as sex, physical condition and social preferences, with external constraints such as transportation, time of day and day of the week. When adding a third axiom of data from a user’s mobile device to this mix of intelligence, a suspects relevance to a crime becomes apparent.
This data that potentially connects a suspect to a crime can typically be found in the knowledgeC database of an iPhone.
What exactly is the knowledgeC* database?
The knowledgeC database stores an event log of multiple processes that run within an Apple device ranging from application usage to speaker output switching.
*KnowledgeC.db is the database behind the coreduet daemon in iOS meant to synchronize states between apple products.
How does knowledgeC data enrich digital investigations?
The knowledgeC database can become a digital intelligence goldmine as it opens a window into a phone owner’s actual usage. Investigators can then take a closer look at application activity that includes when an app was installed, opened, and all of the spotlight searches performed.
Insight into when a device was locked or unlocked can indicate that a device was in the hands of its owner at a certain point and place in time. For example, if right after an unlock event, someone searches for something, looks at Apple Maps or opens WhatsApp – it is reasonable to conclude that it was the owner.
Some of the additional information could include when the device was plugged into a charger or PC, login events – whether successful or failed, screen status and much more. This data can reconstruct a user’s timeline and determine facts such as when a message was viewed or if a phone was in the hands of its owner at a specific time.
Here is a real-life dangerous driving case that illustrates the importance of digital data in any investigation. Without the data extracted from the driver’s phone, he may not have been proportionately charged and sentenced. Cellebrite UFED 4PC and Cellebrite Physical Analyzer were used to reveal the messages he was sending in WhatsApp while driving. Read the full case study here.
Cellebrite Physical Analyzer retrieves knowledgeC data
With Cellebrite Physical Analyzer 7.19, the above mentioned knowledgeC data is available for review after an iPhone data extraction is performed. This data is only accessible via a full file system extraction, performed either with the help of Cellebrite Advanced Services or Cellebrite Premium.
The decoded data is displayed in two new models, the Device Events – where you can find the results of the knowledgeC parser (analyzed data tree) – and the Application Usage Log.
The table below shows the start time, end time, and type of the event including its values. The event type shows if a display is on or off, orientation of the device, if the device is locked or not, if the device was connected to an electric output and more.
See specific event marked below:
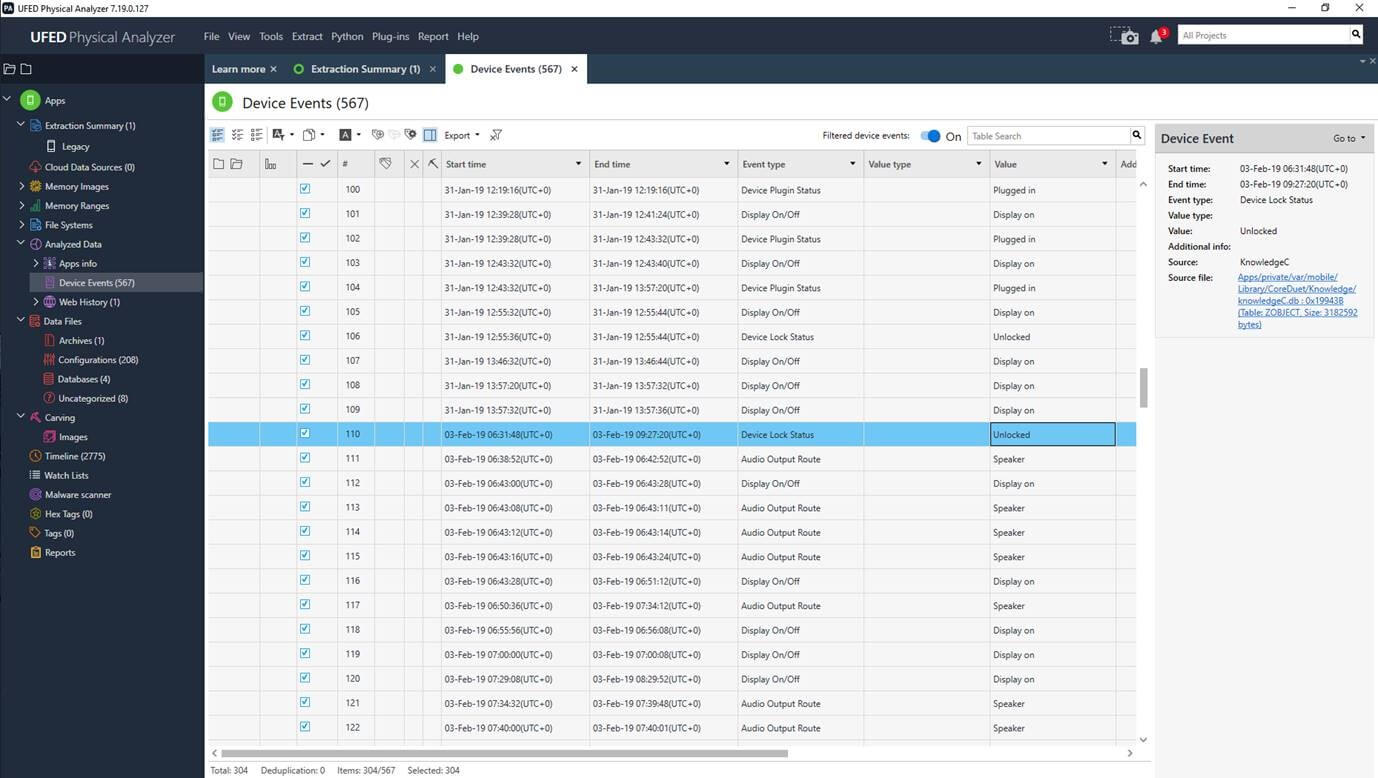
The Device Events model represents various device and operating system events including power events, device lock status, charging status, login events (whether successful or failed) and screen status (back lit, unlit or dark).
In conclusion
Activity-based intelligence can be a critical factor in digital intelligence investigations when uncovering the activities of a person of interest using their smartphone. When investigators can identify which applications were used and answer the ‘when’ and ‘why’ with digital evidence, resolution of cases can be expedited.
