How to Use Cellebrite Inspector to Find Actionable Intelligence

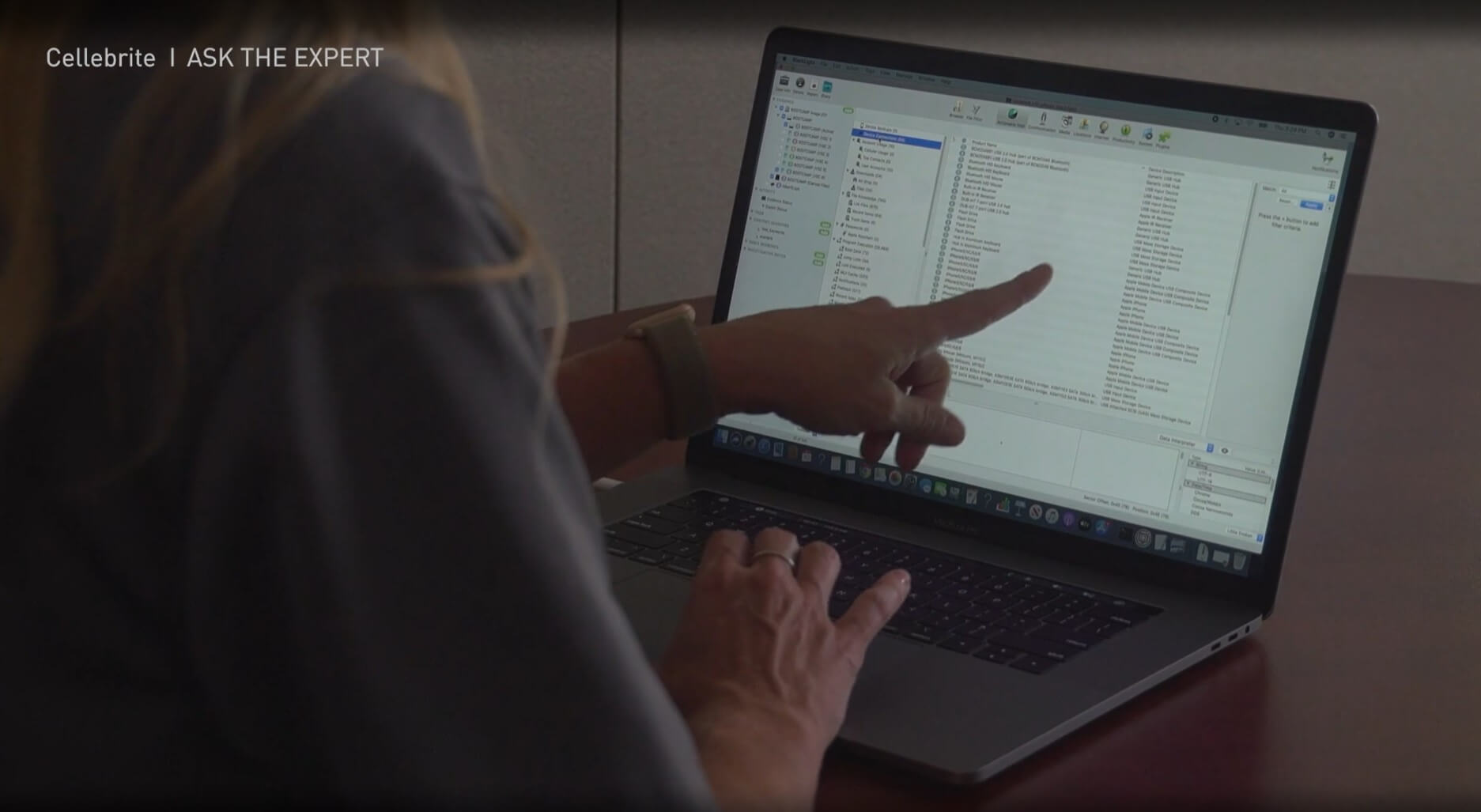
Cellebrite Inspector has a built-in feature called “Actionable Intel,” which is a great place to start when you’re initially looking at your data for an investigation. Actionable Intel includes everything from account usage to program execution. If you’re looking at a Mac, it also has spotlight searches, hidden files, and all the most important aspects needed in an investigation.
Some of the most important aspects include:
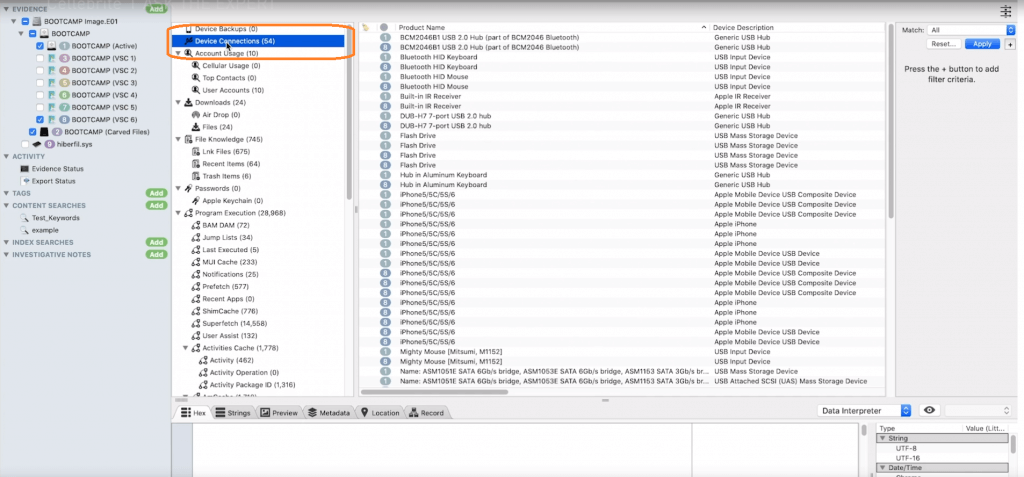
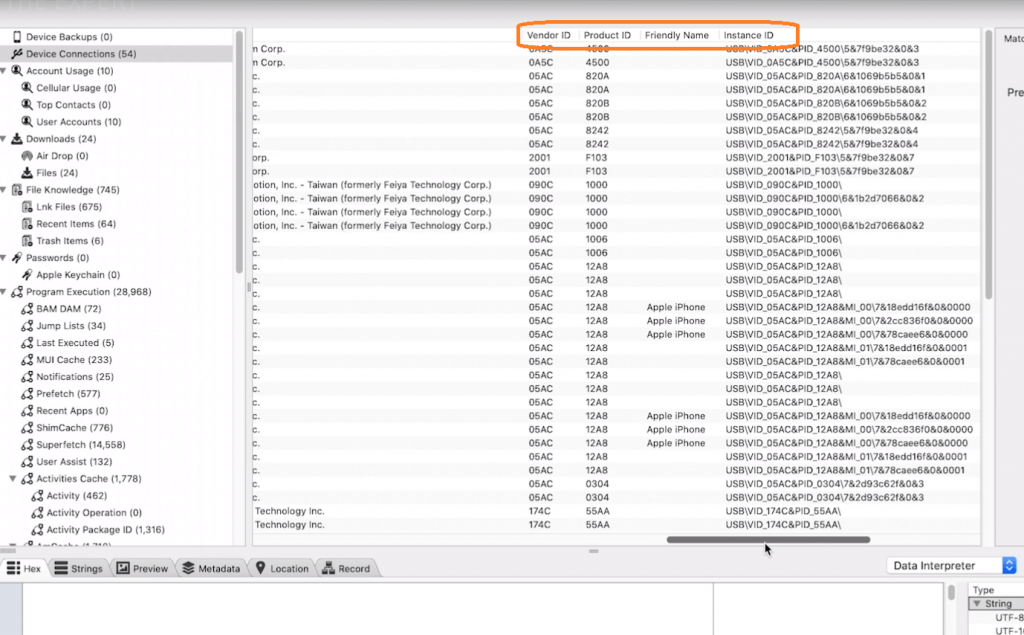
- Device Connections: Not only will Cellebrite Inspector show you all the device connections (iOS and USB devices that were plugged in), but it also breaks through every single thing that the windows registry can do for you. Examples include: first connected, last connected, serial number, type of class, vendor ID, product ID, and friendly name.
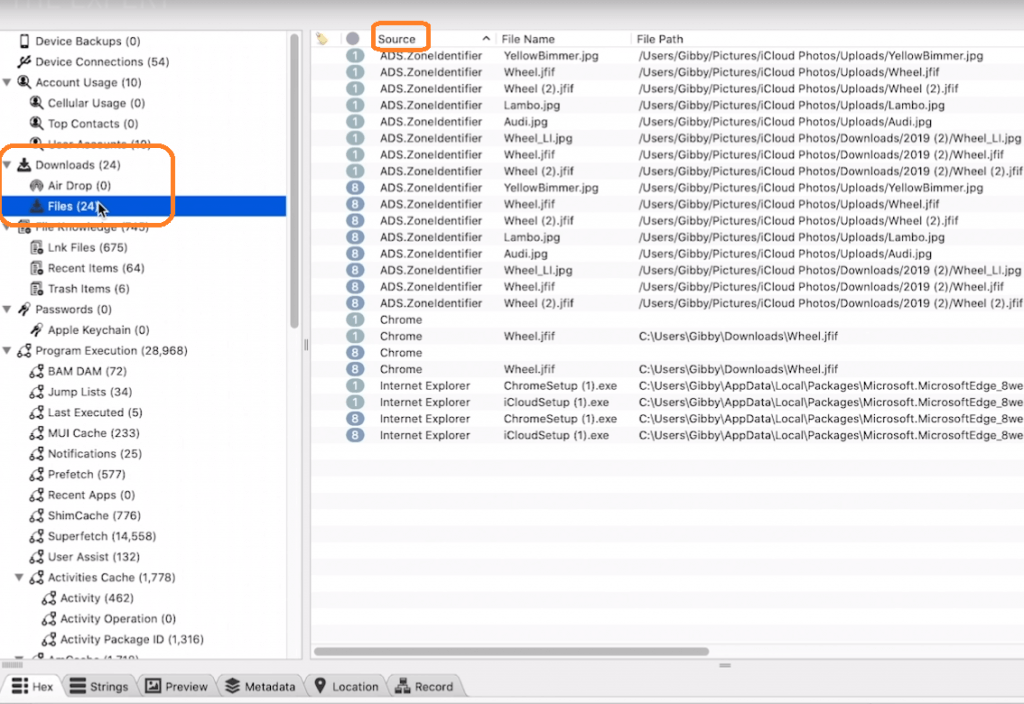
- File Download: This is another great aspect, specifically if you’re working on malware investigations. It provides you with the zone identifier, so you can learn where the person obtained a certain file if it was sent to them or downloaded from the Internet, and how the item arrived on the PC.
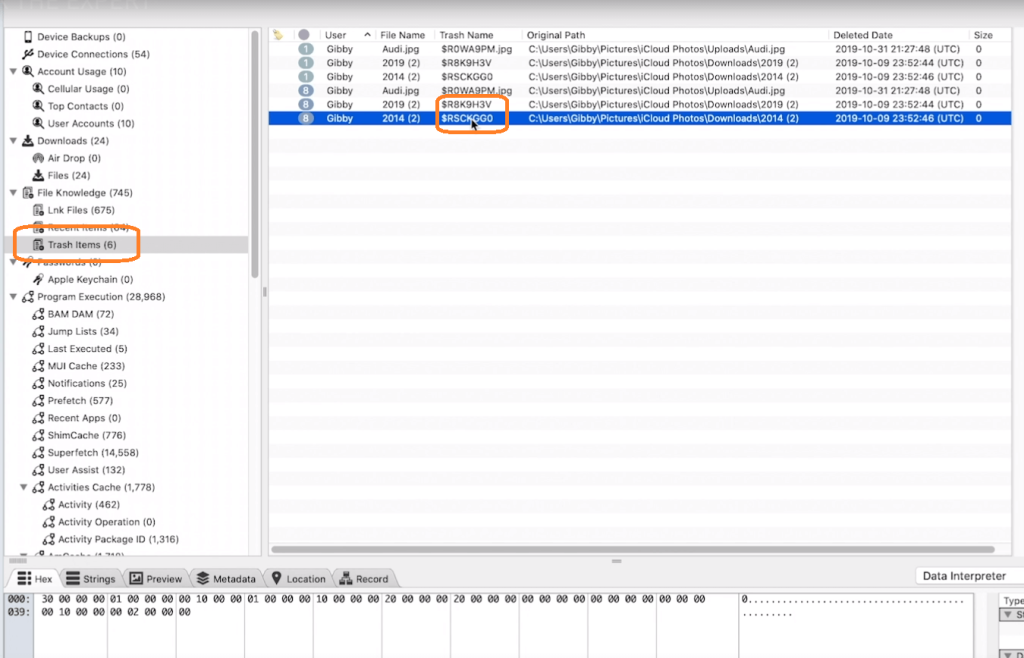
- Trash Items: Under file knowledge, there is also an important and useful section of “Trash Items.” If a file still exists in the trash can, it can still be recovered. That is a huge clue that you need to go there and dig for items like this.
- WordWheelQuery: Under program execution, there is a WordWheelQuery that goes into the window registry.
All these items are parsed within one little icon that’s called “Actionable Intel” which adds a lot of impact to your investigations. I’m going to show you some of my favorites.
Device connections is a great function. I worked many cases in my career where we cared about USBs that are plugged into a system, whether it’s a Mac or a PC. This is a great place for you to find this information. Here I can see everything from iOS devices to USB devices that were plugged in. If you work in an environment with BYOD, this is really important for you.
Not only will it show you the device connections, it literally breaks through every single thing that the windows registry will do for you such as first connected, last connected, serial number, type of class NSC/USB, or was it simply a phone that was plugged into that system, vendor id, product id, and friendly name.
Keep in mind that if someone reformats a USB and plugs it into the system, the friendly name may change, but the hardware serial number will not. So you want to make sure that you’re aware of these things and Inspector is going to give you a clue on that.
Now let’s dig down a little bit deeper. We have accounts and we have files, so “file download” is a great place to start if you’re working on a malware investigation. It will give you the zone identifier so you know where the person got that file, and whether it was sent to them or downloaded from the Internet. How did that item arrive on that PC?
One of my favorites under file knowledge is “trash items.” If you look closely at these and you see the dollar sign r files, is the dollar sign recoverable? The file still exists in the trash can and you can recover it and that is a clue that you need to go there and dig for items like this.
Again program execution, what the user is typing in WordWheelQuery is important. If you open up a Windows search or you click on the magnifying glass on your PC and you type “Heather,” you’ll see all the searches that appear. That’s called a WordWheelQuery and that goes into the Windows registry.
