How To Use Cellebrite Physical Analyzer’s New Cloud Feature

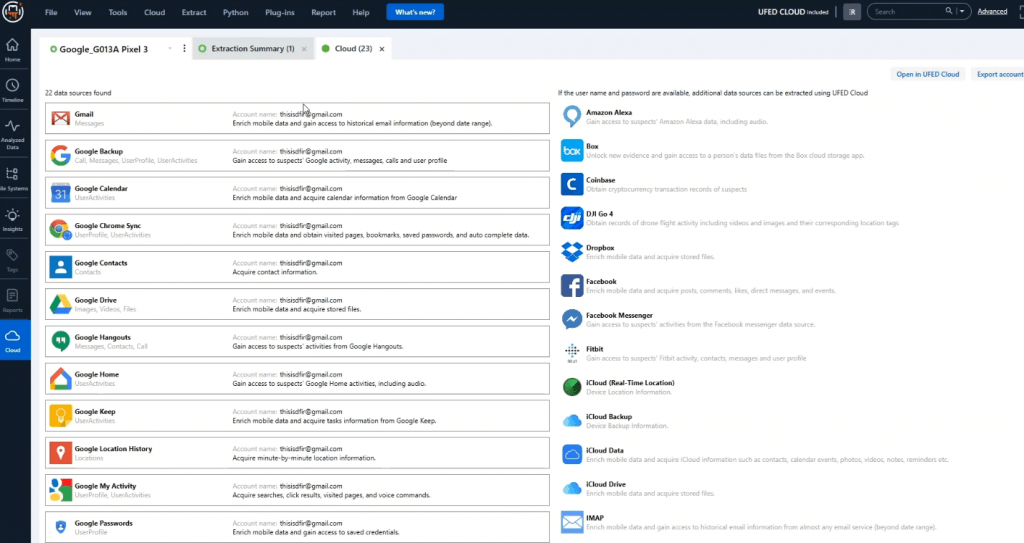
You asked and we listened. Cellebrite Cloud Analyzer and Cellebrite Physical Analyzer (PA) have combined to provide one platform for analysis and collection of cloud data. Within PA, you can export cloud packages that contain tokens and passwords collected from the device. Once exported, these packages can be leveraged to collect cloud data within PA.
Essentially, you are pulling information from the device being examined to capture even more data from the Cloud that pertains to that investigation. Keep in mind, you must have consent or legal rights to pull cloud data.
In addition to exporting cloud packages, PA is capable of collecting data from the Cloud. This includes everything from Google, iCloud, and even most applications that leverage the Cloud for data storage.
This video will walk you through exporting tokens, importing cloud data, and collection techniques. Failures will be explained, as most who try to access cloud data are aware that this process is complex and always changing.
Cellebrite Physical Analyzer has built-in cloud capabilities to give you one platform to collect and analyze all your information. If you already have an image loaded, select the cloud model in order to see all the cloud data collection appear on the screen.
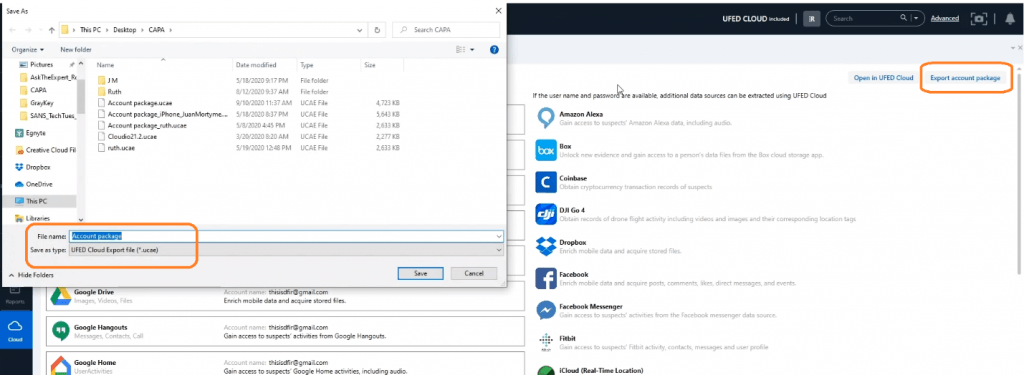
As you export the account package, it will prompt you to do a few things. First, choose where to save the package, save it as a “UCAE file,” name it, and save. Next, it will ask you about associated accounts like Twitter, Skype, Instagram, etc. You can choose to save these or just exit out.
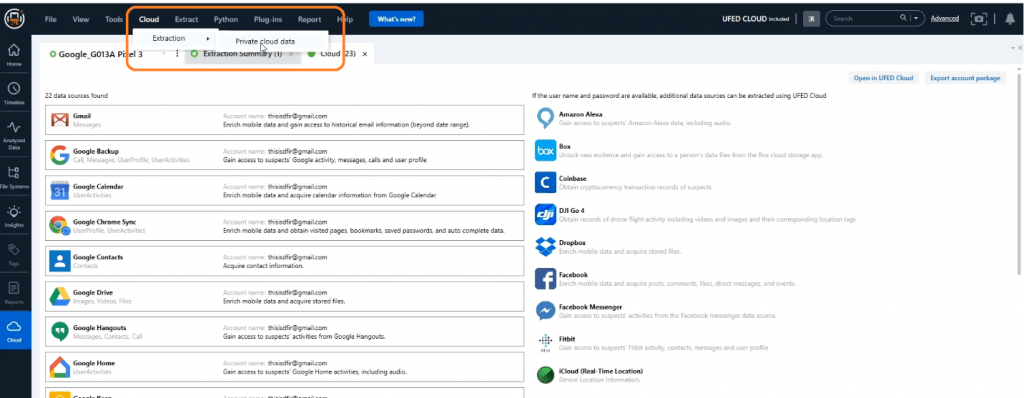
If you want to pool cloud data, go to the top toolbar, and select “Cloud,” > “Extraction” > “Private Cloud data.” You’ll need the first and last name of the suspect or custodian that you’re examining and the consent or a search warrant to ensure that it is done legally and that you have the right to collect this data.
When prompted to enter the time zone, it is best to use the original extracted value rather than the local time.
Create a UFDR, include the original zip file containers, and select the path to save it.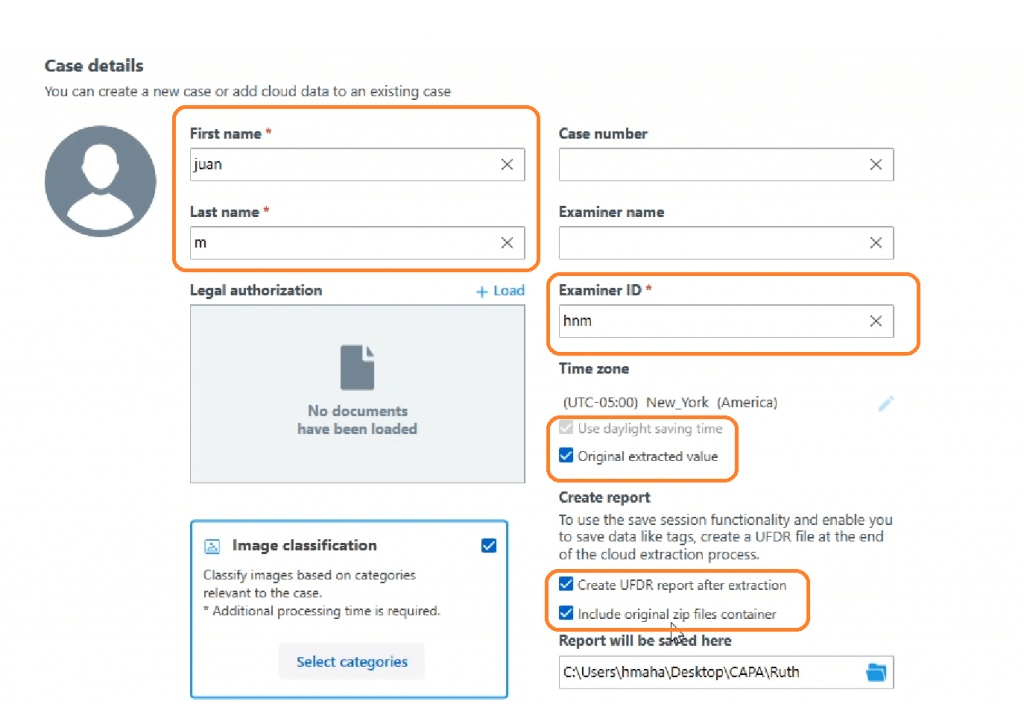
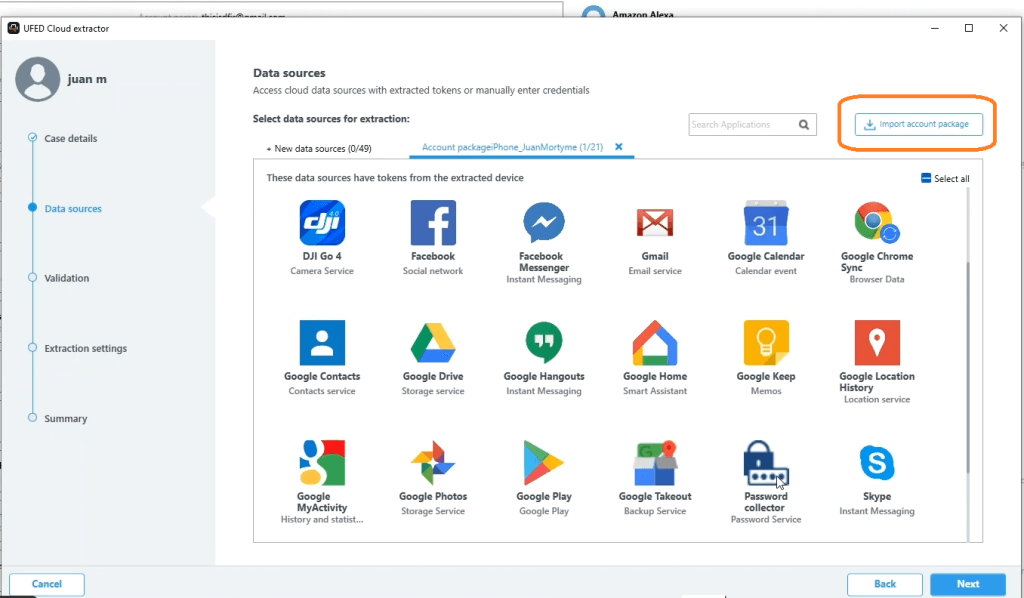
Next, it is necessary to choose if you want to import account packages. If so, choose what you want to select, e.g., TikTok, Password Extractor, Skype, etc.
The next point of validation is to look for any errors. A common error appears if someone has changed the password rendering the tokens or certificates invalid. If this occurs, simply click to see the password if possible or remove the selected item until the proper credentials can be obtained.
When choosing the date range, keep in mind that the longer the time frame you choose, the longer the data collection will take. Also, make sure you are only collecting data that you have the right to access. Finally, press “Next” to go through and collect all the cloud data where the extraction will parse naturally inside Physical Analyzer.
