
Part 2: Walk-Through of Answers to the 2021 CTF – Marsha’s PC
This is the second walk-through explaining how we arrived at the answers to the recent Capture the Flag event.
Keep in mind that in this article we reference blogs written by various DFIR community members who wrote about the CTF and proposed alternative paths to the answers which we arrived at. This is great and demonstrates the versatility and effectiveness of digital forensics skillsets to achieve the same results.
Read the CTF backstory here: “Part 1: Walk-Through of Answers to the 2021 CTF – Investigating Heisenberg’s Android Device.”
Let’s dive into questions concerning Marsha’s PC.
Question 7: Backup & Syncing – Marsha’s PC (10 points)
Were any backups located on the PC? If so, what is the name of the device that was backed up?
Hint: Load the extraction into Cellebrite Inspector and look at the artifacts under Actionable Intel. (0 points)
Flag: Marsha’s iPhone
The easiest way to solve this is to look under ‘Actionable Intel’ in Cellebrite Inspector. Under ‘Device Backups,’ you will see that Marsha’s iPhone was connected. A trick I also like to recommend to people is to search for the keyword “MobileSync” or “info.plist” on the PC to locate the path of the backup.
Inspector provides additional information about the backup under ‘Actionable Intel’ as seen below:

Question 41: User Activity – Marsha’s PC (10 points)
When did Marsha last change the password on her PC? (The answer must be shown as YYYY-MM-DD HH:MM:SS)
Hint: Examine user accounts or registry keys that store user account information. Inspector is helpful here. (0 points cost)
Flag: 2021-03-23 19:22:12
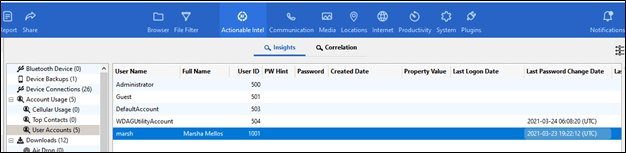
Most tools parse the SAM Hive from the Windows Registry, which stores the last password change for users. Inspector parses this as shown below under User Accounts in Actionable Intel.
Question 42: User Activity – Marsha’s PC (20 points)
Some computers have settings to force password resets. Marsha’s PC does not have this ruleset. Which user key stores this information?
Hints:
- Windows Registry tracks a lot about users (0 points)
- When you find Marsha’s SID, convert that to determine which user key is associated with her information.
Flag: 000003E9
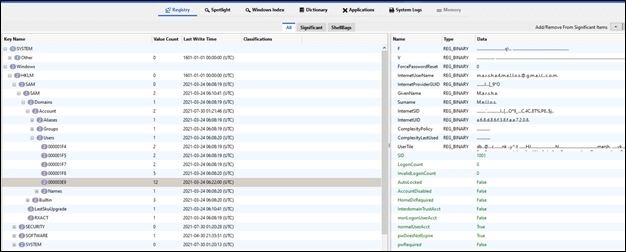
This is a fun one and conversions matter when examining the Windows Registry. Her SID is 1001 which converts from decimal to HEX 3E9. The SAM hive in the Windows Registry will store this information as shown below.
Question 43: Settings and Notifications – Marsha’s PC (10 points)
What is Marsha’s timezone set to on her PC? (Make sure your answer says THIS STANDARD TIME. The word “time” must be in your answer.)
Hint: Windows Registry knows it all.
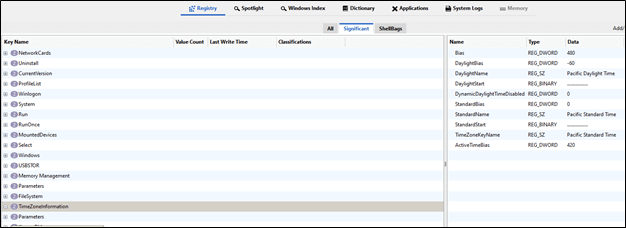
Flag: Pacific Standard Time
The System Hive within the Windows Registry stores the timezone settings for the machine. The full path is HKLM\SYSTEM\ControlSet001\Control\TimeZoneInformation.
Question 44: User Activity – Marsha’s PC (20 points)
On Marsha’s PC, what is the path for how the user landed on a directory named “DELETEME”? (Provide the full path as the user would see it. For example – c:\users\marsha\desktop\deleteme).
Hints:
- Shellbags are parsed by many tools. The shell will show you the path to arrive at specific files and folders. (0 points)
- The UsrClass.dat file stores shell items that may be helpful. (5 points)
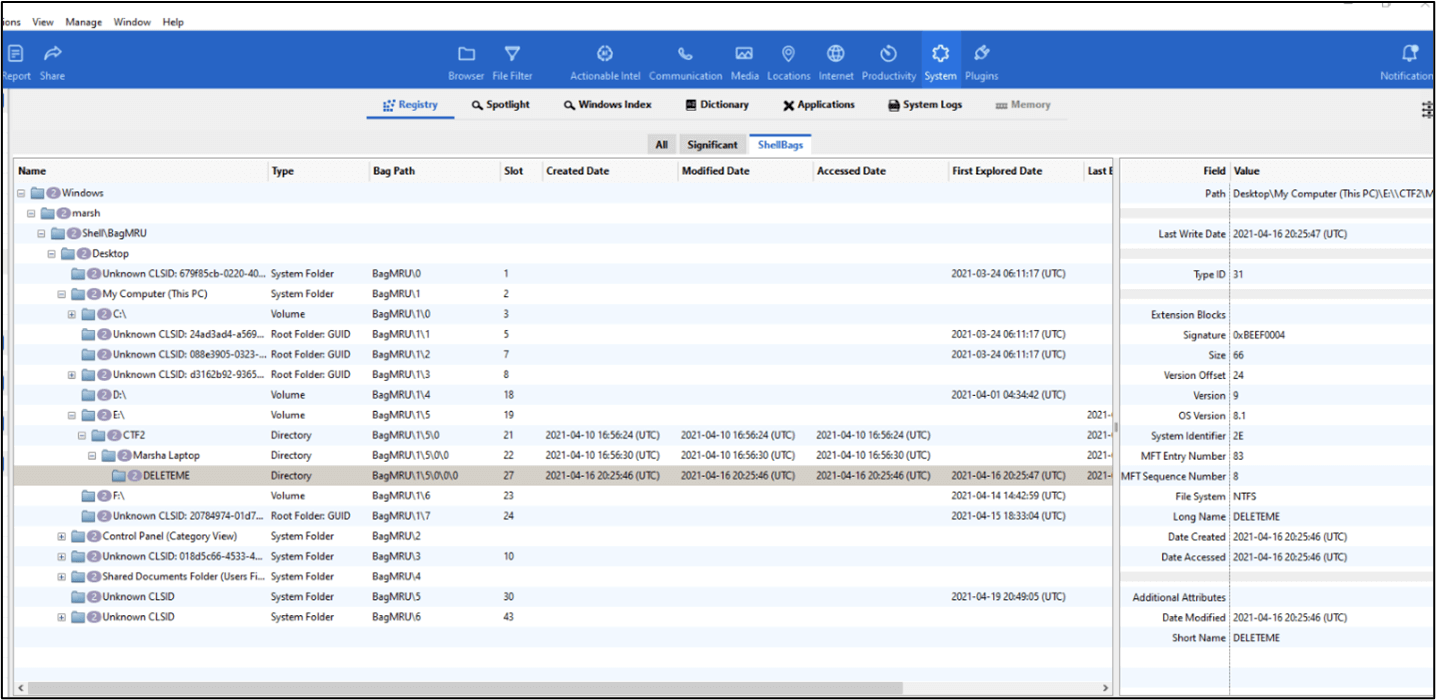
Flag: E:\CTF2\Marsha Laptop\Deleteme
Shell items track the path the user took to land on specific files and folders. In Inspector, ShellBags can be examined by selecting ‘System’ and then ‘ShellBags.’ This should be able to point you in the right direction and provide you with the full path for the answer. This can also be found by manually examining the UsrClass.dat.
Question 45: Application Analysis – Marsha’s PC (10 points)
Marsha searched for anti-forensic methods on her PC. What did she search for other than “how to wipe my data” in regards to securing her phone?
Hint: Look at parsed browser data for recent searches.
Flag: “encrypt my fone”
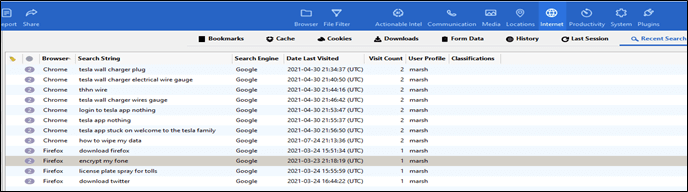
Since we are talking about searching for information, it should have brought you to internet artifacts. In Inspector, under Chrome Browsing History, you can see the answer ‘encrypt my fone’.
Question 46: Device Connections – Marsha’s PC (10 points)
What was the drive letter associated with the media from which Digital Collector was run? (Make sure the form is as follows – h:\\)
Hint: Perform a keyword search in Cellebrite Digital Collector, or look for USB activity. (0 points)
Flag: d:\
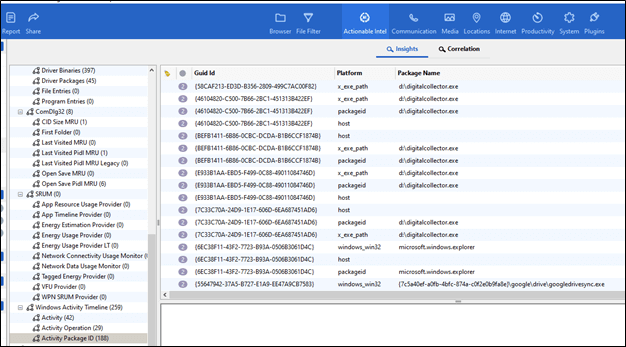
There are many places you can find the answer to this one. We leveraged ‘Actionable Intel’ in Inspector and then selected ‘Activity Package’ under ‘Windows Activity Timeline.’ You can also find the answer by examining ‘Event Logs’ and the Windows Registry.
Question 47: Device Identification – Marsha’s PC (10 points)
Which operating system is running on Marsha’s PC?
Hint: List the answer exactly as it is stated by the tools or in the Windows Registry.
Flag: Windows 10 pro
The Windows Registry stores information on the current operating system here: /Windows/System32/config/SOFTWARE. In Inspector, this can be found under ‘System’ and ‘Significant.’ The current version has the answers.
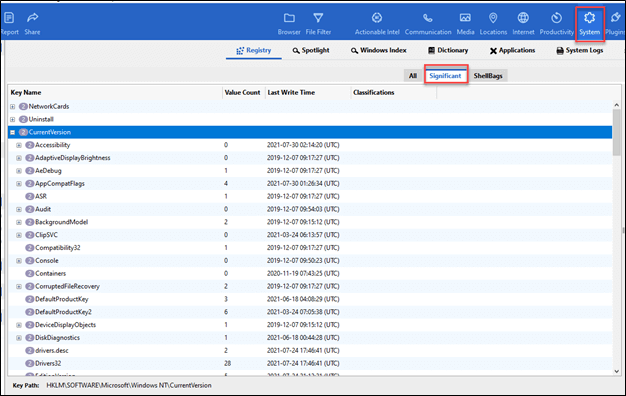
The view on the right pane shows the artifacts from the Current Windows Version.

Question 51: Device Connections – Marsha’s PC (50 points)
When was Beth’s device “trusted” on Marsha’s PC? A “trust” is something the user must establish between the device and the PC. (Answer must be in the following format: YYYY-MM-DD HH:MM:SS)
Flag: 2021-04-06 22:32:34
Even though this question may sound simple when searching a connected device, it’s not as simple as you may think. The twist to this, which we hope you picked up on, is the trust, and not just the connection.
When an iOS device is trusted, a lockdown file is created. You need to look under – C:\ProgramData\Apple\Lockdown. You need to determine which one applies to the device and look at the created time which gives you the answer.
Another way to find it is to use the File Filter view in Inspector then while searching for plist files, look for the device UDID that can be found in Beth’s extraction. The answers may not always be in one place when multiple devices are in use.

Question 52: Application Usage – Marsha’s PC (20 points)
How many times was OneNote run on Marsha’s PC?
Hints:
- This information is stored in the Registry Hive that is associated with the user on the PC. (0 points)
- Think Program Execution to help find this answer. (5 points)
Flag: 2
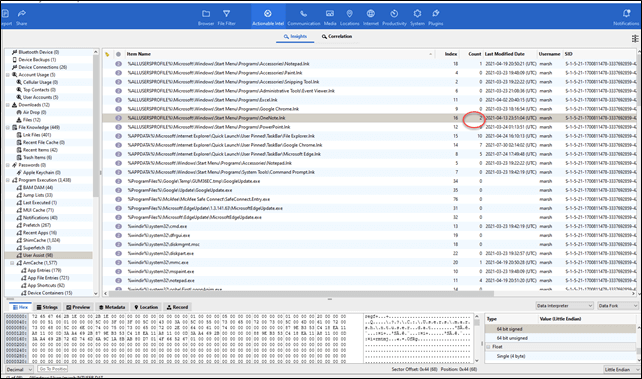
The place you should be looking for is under UserAssist, then under Actionable Intel. If you find the shortcut link to OneNote, you can see that it has been run two times.
Question 53: Application Analysis – Marsha’s PC (20 points)
What was the high temperature provided in the Bing weather notification on Marsha’s PC? (Answer must be provided as an integer, ie. 72)
Hints:
- Search for parsed notifications. (0 points)
- Actionable Intel is your friend in Inspector. Start with notifications stored there. (5 points)
Flag: 89
The best place to start looking for this is in notifications. If you filter for Bing and review the notifications, you will find the results for the temperatures. You need to select the highest temperature for that day.
Question 54: Native Applications – Marsha’s PC (20 points)
When was cmd(dot)exe last run on Marsha’s PC? The answer must be provided in the following format: YYYY-MM-DD HH:MM:SS. (“dot” is written here due to constraints of webpage security parameters)
Hints:
- Evidence of execution is what you are looking for. Consider files that track an executed app. (0 points)
- Wouldn’t it be nice if you could “fetch” this answer out of Program Executions? (5 points)
Flag: 2021-07-30 02:13:55
‘Prefetch Files’ track the last runtime for programs on the PC. This is found under Actionable Intel in Inspector or in the native prefetch files on the PC. /Windows/Windows/Prefetch/CMD(dot)EXE-0BD30981.pf

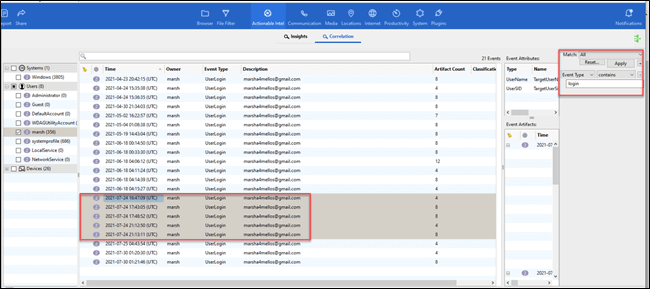
Question 58: User Activity – Marsha’s PC (20 points)
How many times did Marsha log in to her computer on July 24th, 2021? (The answer must be an integer.)
Hints:
- Inspector will help you with Actionable Intelligence. (0 points)
- Filter and search correlations. (5 points)
Flag: 5
You can either examine the Windows Event Logs for this information or you can use Inspector to filter under ‘correlations.’ Below, you can see how to select the filter. Select the “+” and then type the Event Type “login” which will render a result.
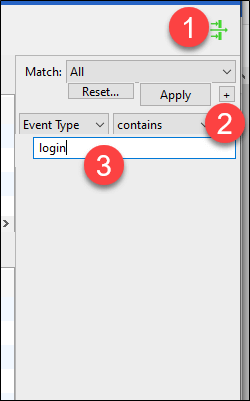
From here, sort by date and you will see five log-ins for Marsha on the date of interest.
Question 59: Device Connections – Marsha’s PC (20 points)
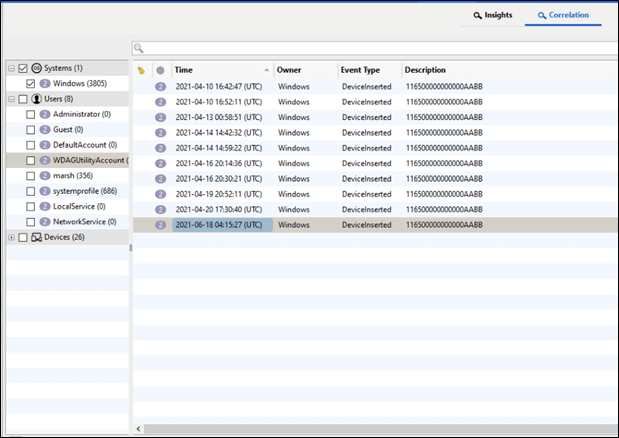
How many times was the USB, with the serial number “116500000000000AABB,” inserted into Marsha’s PC between April 10th to Jun 18th, 2021?
Hints:
- Inspector correlations are helpful. (0 points)
- Filtering is your friend. Filter by event and description. (5 points)
Flag: 10
This question can be solved in Inspector with some simple filtering or by examining the Event Logs and Windows Registry. In Inspector, select the filter (1), then “+” (2) and enter “DeviceInserted” as Event Type (3). Click the “+” again (4) and copy and paste the device ID “116500000000000AABB” as Description (5).
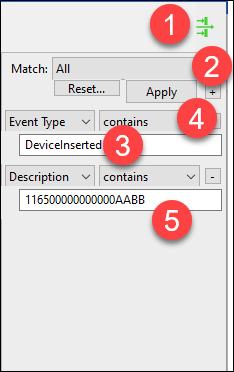
The results are rendered, and you can see the dates and times for which that USB was inserted into Marsha’s PC.
So, that is it for Marsha’s PC. We hope you enjoyed this part of the CTF and are even better prepared for another round of CTF questions in the spring of 2022.
We also want to give credit to others who took the time to share their walk-throughs. It’s important to read these blogs as the author may have derived the answer via a different file, artifact, or tool.
Thank you for taking the time to share your results!
Reference link:
https://medium.com/@williamskosasi/cellebrite-ctf-2021-writeup-b73d821a708
