Social Media is No Longer a Haven for Criminals
“Over 2.5 quintillion bytes of data are created every single day.” That’s how a recent report posted on Social Media Today described the stratospheric rise in data being generated worldwide. And that’s just the beginning. According to the report, by the end of this year, “it’s estimated that 1.7MB of data will be created every second for every person on earth.”
Much of that information is being stored in the Cloud— a low-cost repository for files and apps, and a universal back-up for phone data, photos, and documents we’d rather not carry on our devices. Today, the Cloud also provides storage for all of our messages sent via email or instant messenger apps. And it is the primary back-up for social media. Also, there is a misconception that all application history is on the device. Uploaded files, web history, and data older than 12 months, is often only available in the cloud.

What The Cloud Can Reveal
Storing data in the Cloud is convenient, but it also leaves us vulnerable to criminal hackers. The Best Practices Guide provided by the National White Collar Crime Center (NW3C) provides a chilling reminder that with so much personal information stored in the Cloud—”account information, message content, location data, recently connected devices, media, connected apps, tokens, web history, contacts and social media activity such as likes, conversations, and messages”—there is much that criminals can take advantage of.
The good news for investigators (and a great irony), is that since criminals are also using data-driven devices and apps (including social media) to communicate, organize, and commit crimes, they, too are leaving a long trail of valuable evidence behind that can be traced.
Smart investigators are following those trails.
Cloud Sourcing By The Numbers
Cellebrite’s 2020 Industry Trends Survey revealed some interesting stats. Here’s how examiners and investigators responded to questions about gathering cloud-sourced evidence.
- 50% of examiners said their cases involve/require access to data stored on cloud sources.
- 50% of examiners submit warrants for data from tech relevant companies
- 9 to 11 weeks is the average time it takes to receive data from a warrant return.
- 17% rise in the legal difficulty associated with using cloud data in the last three years.
- 90+% of investigators said text messages and conversations are the source they review most frequently for evidence followed closely by images, videos, and social media—all stored in the Cloud.
The problem, however, is that data can easily be deleted, and devices can be smashed or burned, destroying evidence trails. This is why it’s critical for investigators to gather evidence either directly from the devices or through consent-based extractions from the Cloud when legally authorized.
Catching Butterflies Isn’t Easy
As simple as it sounds, gathering cloud-based information isn’t easy but it brings tremendous value to an investigation. In a recent Cellebrite Webinar “How To Incorporate Cloud Evidence Into Your Investigations For Maximum Results”, the guest speakers shared real-life cases and how they leveraged cloud location data to resolve them.
Legal Challenges to Social Downloads
Downloading information directly from social media channels presents legal challenges as well:
- Subpoenas, court orders, and search warrants required to access popular social media accounts and cloud-storage providers like Google, Microsoft, and Dropbox can take weeks to acquire.
- How warrants are worded can also be troublesome. If the warrant is too general, you might not get the information you’re seeking. If the warrant language is narrowly worded, you risk missing valuable evidence that might have turned up under a wider search request.
- When legally forced to give up data, social media and cloud companies may deliver documentation that can range from a single piece of paper to terabytes of information. It all depends on how they store and export data.
- Even when they receive a data dump from providers, investigative teams may be forced to sort through large volumes of unstructured data to find potential evidence. This wastes valuable time and resources.
This is why police departments, business IT departments, and military and intelligence agencies are rethinking their digital intelligence strategies.
There Is A Better Way
To solve crimes faster, agencies need a complete end-to-end solution that allows cloud-based data to be:
- Quickly gathered in the field through consent-based extractions.
- Uploaded to a central repository where the data can be managed in a forensically sound manner that ensures the integrity of the evidence until legal permission to access the data can be acquired.
- Analyzed by trained professionals using the latest digital intelligence technologies to connect disparate pieces of evidence that would be overlooked using conventional investigative methods to provide actionable intelligence.
- Managed within a lawful framework that provides court-ready evidence while preserving individual privacy.
The Right Solutions
As the recognized leader in digital intelligence, Cellebrite has a number of solutions that can help investigators solve crimes faster using cloud-based evidence.
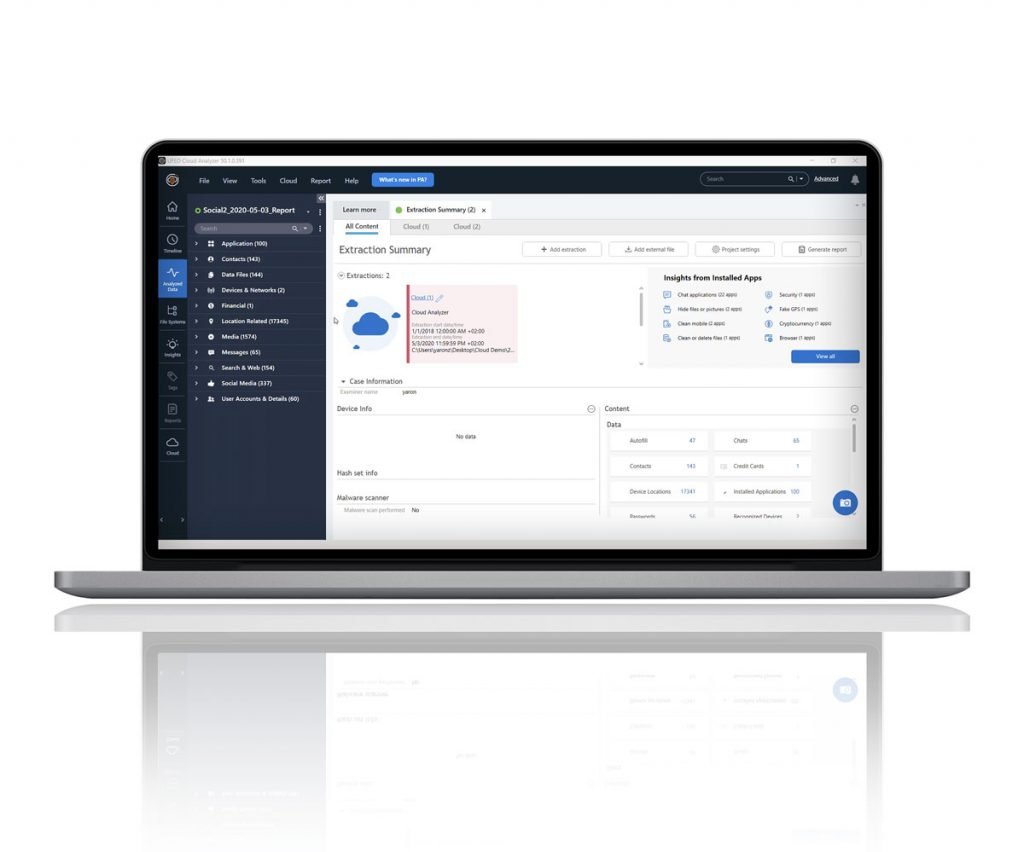
Access Cloud Data: Cellebrite UFED Cloud allows users to extract, preserve, and analyze public- and private-domain social media data, instant messaging, file storage, web pages and other cloud-based content using a forensically sound process. Easily search, filter, and sort data to quickly identify suspects, victims, locations, and more—all within pre-approved legal boundaries.
Cellebrite UFED Cloud Analyzer supports data capture in four main methods; Public domain access using an avatar, entering user credentials, utilizing a device account package with tokens, or using a computer account package.
Extract cloud Tokens: Cellebrite’s flagship extraction solution Cellebrite UFED, enables access to cloud tokens and maximum data from popular applications on both iOS and Android devices.
Review persona profile and event timeline: Cellebrite Physical Analyzer allows you to bring in the data from all the cloud sources, translate the content where relevant and perform a thorough review of the data.
Manage Your Devices: the Cellebrite Commander can manage all deployed devices with ease and optimize how forensic tools are used.
Teams can perform complex analysis of DI data and collaborate in real time to discover hidden evidence in text messages, images, and videos to reveal connections, group hierarchies, and communication patterns.
Case Studies
The following case studies show how accessing cloud-based evidence can solve a wide range of crimes.
Digital Intelligence Leads To Multiple Arrests In Nepal Drug Bust – Nepal police used leads from extracted phone and cloud data to arrest multiple suspects and discover links to higher-ups in a drug cartel.
GPS Data Extraction Helps Change The Focus Of A Murder Investigation In Brazil – Cellebrite UFED Cloud identified crucial digital evidence to solve the case of a violent homicide in Brazil.
Summary
Cellebrite is the recognized leader in providing reliable and forensically sound access to physical devices, including cloud data and social media account information. Cellebrite also provides powerful analytics powered by AI and advanced algorithms to automate time-consuming and repetitive data-sorting tasks.