Android Forensics, Smart Flow, Selective File System Extraction
Part 2 of Cellebrite Solutions 2022 Update Summary
Cellebrite released many updates to its digital intelligence and forensics solutions in 2022. These updates were covered in a recent on-demand webinar you can watch here.
This blog is part 2 in the series and will highlight the mobile device forensic tool updates supporting Android devices. You can read Part 1 here: iOS Forensics Advanced Logical File System Extraction and Checkm8 – Cellebrite Solutions 2022 Update Summary.
Android Live consent-based collection
We have introduced the universal Android Live consent-based collection which is a unique industry-leading capability that provides the widest range of coverage for lawfully unlocked Android devices. The extraction method has been introduced in the latest UFED – Version 7.60, and is being added to the Android Smart Flow.
Universal Android Live supports the most popular SoCs (System on Chip) in the market:
- Qualcomm MTK
- Kirin
- Unisoc (Speadtrum)
- Exynos
- and the newly introduced SoC JLQ used in the Xiaomi Pro C
This capability supports a very wide range of devices that were not previously supported. And it comes with no known security patch level limitations. Some of the supported devices:
- Samsung A12, A21, S22 Ultra series
- Google Pixel models, including the Pixel 7 and 7 Pro
- Xiaomi and Oppo models
- OnePlus
- Honor 70 Pro Plus
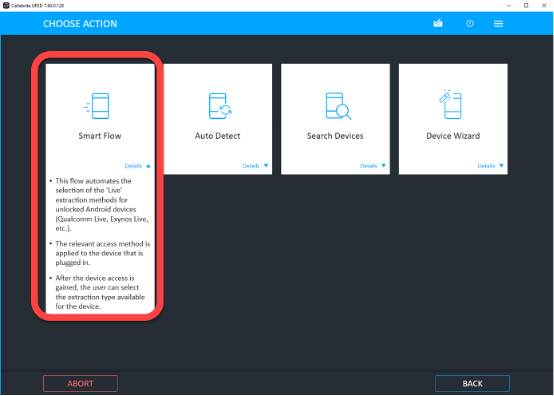
Smart Flow
Keeping up with the ever-changing mobile device industry is challenging, so the digital forensics examiner must quickly be able to properly identify a device and select the relevant profile to start the extraction process efficiently.
Universal Android Live has been added to this investigative flow in UFED 7.60, so it provides support for devices that have not been previously supported by the Live methods.
Watch the video below – How to Maximize Your File System Extractions With UFED Smart Flow in Mobile Forensics

Smart Flow is a simplified flow that automatically selects the appropriate Live assessment method for unlocking and directing devices like the Qualcomm Live and Exit Nodes Live.
So using it is simple: select the device profile and method, and by connecting the device the relevant assessment method will be automatically applied. After gaining device access, select one of the extraction types presented for the device.
This simplifies the Android flow down to one pattern and there’s no need to search for the right profile to use. Start with Smart Flow if you are about to lawfully unlock and extract from an Android device, rather than looking for the right profile or method to use.
Selective File System Extraction
This enables you to select the key artifacts you are authorized to collect from the device. Although a full file system extraction is usually recommended because it provides the most information, selective file system extraction is useful when there is a time constraint.
In the selective file system list, you can choose either the app’s location or tokens. And in the latest release of UFED 7.60, the first beta release of the selective extraction by file is added to the list.
This capability enables you to transverse the file system and select the specific folders and files to extract. All the relevant metadata of the files is retained, and the forensic integrity of the file remains intact. Additional filtering and other capabilities will be added in the second phase of the release.
Watch the video below – Ask the Expert: How to Use the Selective File System Extraction in Cellebrite UFED – Heather Mahalik

More and more of the SoCs are now supported in the live extraction method as a generic capability. This capability is not limited to any security patch level and supports a very wide range of consent devices.
All the live extraction methods are now fully automated in Smart Flow, and these live methods are also available in the explicit device profiles. All the live methods are improved, like Qualcomm Live, MTK Live, Kirin Live, and Exynos Live. Other devices are also added.
Android 13 Beta
This is the first to market full file system supporting eligible devices running on Android 13 Beta. We built the ability to perform a full file system extraction for certain tested Android devices that we assessed using the relevant live matters during the beta. Not all the eligible devices were tested with Android 13 Beta, so if you come across any devices that are not supported, reach out to us and let us know.
Collect Secured Apps
The Android Keystore system lets you store cryptographic keys in a safe location in order to make it difficult to collect them from the phone. The keys can be used for encryption and decryption operations without entering the application because the cryptographic operation is handled in the operating system with a hot web back system.
With the Collect Secure Apps feature, you can collect and decode the data from more applications that leverage this Keystore for additional security. The secure applications included in this capability are:
- Samsung Health
- Pluto Mail
- Samsung Rubin
- Instagram Crowd Token
All these supported applications can be collected on Android devices running operating systems through to Android 12. To successfully extract them, use the live extraction and full file system extraction methods.
APK Downgrade
UFED now supports the APK Downgrade extraction on Android 12 devices. We have added additional applications to these extraction methods, including FM WhatsApp, WhatsApp Plus, and Telegram X.